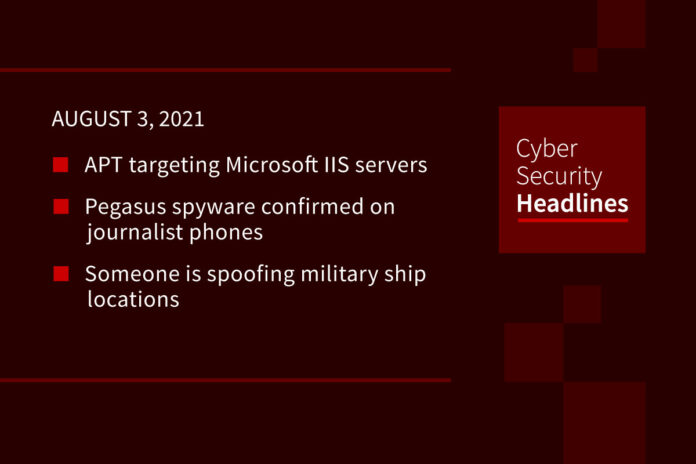
APT targeting Microsoft IIS servers
Researchers at the security firm Sygnia discovered the campaign, believed to be carried out by the APT “Praying Mantis.” The attackers are targeting high-profile entities using exploits in Microsoft Internet Information Services or IIS servers, using “a custom-made malware framework, built around a common core, tailor-made for IIS servers” that loads in memory, making it hard to trace. Praying Mantis initially uses an arsenal of ASP.NET web application exploits to get an initial foothold before targeting the IIS servers. The researchers found “major overlaps” in how the group works with the nation-sponsored actor named “Copy-Paste Compromises.”
Pegasus spyware confirmed on journalist phones
French intelligence investigators say Pegasus spyware has been found on the phones of three journalists, including a senior staff member at the country’s international television station France 24. This is significant because it’s the first time an independent authority has corroborated the findings of Forbidden Stories, a Paris-based nonprofit media organisation, and Amnesty International, both of who initially had access to a leaked list of 50,000 numbers that are believed to have belong to people of interest by clients of the Israeli firm NSO Group since 2016, and shared access with their media partners.
Someone is spoofing military ship locations
According to an analysis by the nonprofit SkyTruth and Global Fishing Watch, since August 2020, over 100 warships from at least 14 European countries, Russia, and the US have had locations faked using the automatic identification system or AIS. These faked locations were often in disputed or into territorial waters of another country and lasted up to days at a time. Researchers were not able to tie the faked signals to any country, organization, or individual, but shared common characteristics indicating they came from the same actor. Part of the problem is that AIS is an unencrypted system, with some in the security community calling for adding digital signatures to each AIS transmission.
(Wired)
It’s like bug bounties but for algorithms
Twitter announced the algorithmic bias bounty challenge, offering prizes between $500 to $3,500 for researchers who “identify potential harms” of the company’s image cropping model. Twitter is re-releasing the code for its image cropping model, and participants will build their own assessments on it based on both quantitative and qualitative methods. One of the things Twitter is most interested in seeing is what researchers qualify as “potential harms,” which they hope to use to inform future algorithm development.
(ZDNet)
Thanks to our episode sponsor,
PlexTrac

Now we have to worry about pneumatic tubes
The security firm Armis published details on a series of nine security vulnerabilities called PwnedPiper impacting the TransLogic Pneumatic Tube Systems, currently used in over 3,000 hospitals to move things like lab samples and medicine. An attacker on a hospital’s internal network could effectively use the vulnerabilities to take over the entire tube network. Given the recent rash of ransomware attacks against healthcare organizations, this widely used system could open the door for further threat actors. TransLogic says a software update for all but one of the vulnerabilities has been developed, with a mitigation technique available for the unpatched vulnerability.
Empty npm package gets 700,000 downloads
The package has a one-character length name, the “-” symbol, and racked up the download since being published on the registry in early 2020. Inside the 0.0.1 version were three skeleton files, a typical index, package.json, and ReadMe. Despite seemingly having no point in existing, the package is a dependency for over 50 npm packages, although these appear limited to fairly scant download numbers. Bleeping Computer speculated that the high number of downloads could be due to typographical errors when adding a flag to a npm terminal command. The ReadMe indicates the package was created by a script, and there doesn’t appear to be anything malicious in the package.
Researcher finds a block to the PetitPotam vulnerability
Last month, a security researcher detailed the PetitPotam vulnerability, which forces Windows machines and domain controllers to authenticate against a malicious NTLM relay server. The actors would use this to send a request to a targeted domain’s Active Directory Certificate Services via HTTP, opening the door to let them assume the domain controller’s identity. In response, Microsoft issued guidance on how to mitigate NTLM relay attacks. Now security researcher Craig Kirby published how to block the remote unauthenticated PetitPotam attack vector using NETSH filters.
European Space Agency launches hackable satellite
That description was passed along by security stalwart Bruce Schneier, commenting on the ESA’s launch of a “ flexible software-defined satellite,” designed to be repurposed after its initial launch. The satellite has a planned 15-year lifespan. Bruce hopes it includes “strong encryption, and good key management” but even with it, wonders if it will prove a tempting target to other nations.
(Scheier)