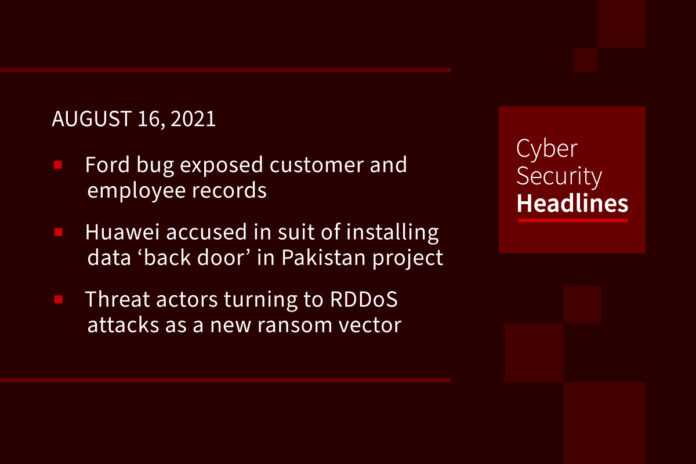
Ford bug exposed customer and employee records from internal systems
A bug on Ford Motor Company’s website allowed access to sensitive systems and proprietary data such as customer databases, employee records, and internal tickets. The data exposure stemmed from a misconfigured instance of a Pega Infinity customer engagement system running on Ford’s servers. Researchers reported their findings to Pega in February of this year, and the issue was also reported to Ford around the same time via their HackerOne vulnerability disclosure program. The vulnerability was patched relatively quickly, however the researchers are expressing frustration around Ford’s unwillingness to cooperate on this issue of disclosure.
Huawei accused in suit of installing data ‘back door’ in Pakistan project
California-based contractor Business Efficiency Solutions says in a lawsuit filed Wednesday in California district court that Huawei required it to set up a system in China that gives Huawei access to sensitive information about citizens and government officials from a safe-cities surveillance project in Pakistan’s second-largest city of Lahore. In comments to The Wall Street Journal last September, Huawei acknowledged setting up a separate version of the Lahore system in China, but said it was only a test version that was “physically isolated from the customer’s live network.” U.S. officials have long alleged Huawei gear could enable Chinese espionage in the countries that install it. Huawei has repeatedly said its gear is safe and that it would never spy on behalf of any government.
Threat actors turning to RDDoS attacks as a new ransom vector
A ransom DDoS attack is an extortion scheme in which cybercriminals either launch a DDoS attack and then demand ransom to stop, or they may ask for the ransom first by threatening with a DDoS attack if not paid. The Neustar International Security Council (NISC) analysis disclosed that nearly 70% of organizations were targeted with RDDoS attacks, and 36% agreed to pay the ransom. The research revealed that only 24% of organizations said they know how to respond to RDDoS attacks. RDDos does not require time and planning like malware or ransomware does and has the added benefit of being harder to trace back to its origin,” said Neustar’s Rodney Joffe.
(CISO Mag)
UK security chiefs issue guidance to ministers over WhatsApp use
Ministers and civil servants conducting “government by WhatsApp” have been at risk of being targeted by hackers, leading to new advice from security chiefs about how to improve their privacy. The cabinet secretary, Simon Case, revealed that the Government Security Group had issued fresh guidance across government after high-profile stories about hackers exploiting WhatsApp. Among the requirements was advice on how to secure devices using two-factor authentication implying that such authentication was not always used routinely.
Thanks to our episode sponsor, Copado

To get a free demo, visit Copado.com.
Job ad published by the UK’s Ministry of Defence reveals secret hacking squad
The UK Ministry of Defence is looking for an extraordinary talented electronics engineer for its secretive unit located in Hereford. The mobile hacker squad, named MAB5, was revealed by a job ad published by the UK’s Ministry of Defence on an external website. The MoD is offering a salary of £33k to and will be tasked with delivering prototype solutions directly to the soldiers and officers of a unique and specialized military unit.” The job ad refers to the MAB5 as “a small military unit that specialises in the provision of novel and ground-breaking science and technology prototypes for operational requirements.”
Amazon considers tracking worker keystrokes
Data theft, insider threats and imposters accessing sensitive customer data have apparently gotten so bad inside Amazon, the company is considering rolling out keyboard-stroke monitoring for its customer-service reps. A confidential memo from inside Amazon described a high exfiltration risk, especially among outsourced employees working from home in countries like India and the Philippines. It’s considering using a company called BehavioSec, which uses the aggregate data of a user’s mouse clicks and keystrokes to develop a profile of their typical behavior. Once that baseline of typical behavior is established, the BehavioSec tool will identify when someone’s activity is unusual.
Google may cut pay of staff who work from home
The technology giant has developed a pay calculator that lets employees see the effects of working remotely or moving offices. Some remote employees, especially those with a long commute, could have their pay cut without changing address. A Google spokesperson said: “Our compensation packages have always been determined by location, and we always pay at the top of the local market based on where an employee works from. Other big tech companies including Microsoft, Facebook, and Twitter have offered less pay for employees based in locations where it is more inexpensive to live, but smaller firms such as Reddit and Zillow have said they will pay the same no matter where employees are based, saying that this improves diversity.
(BBC News)
Be sure to wipe down your workout after your workout
Security researchers have found vulnerabilities in the Wodify fitness platform that allows an attacker to view and modify user workouts and payment records from any of the more than 5,000 gyms that use the solution worldwide. Wodify has yet to confirm the roll out of a patch, despite being given ample time to address the security issues. Leveraging the bug requires authentication, after which an attacker can insert malicious JavaScript code into a target user’s workout comment that would trigger a cross-site scripting (XSS) attacks. Dardan Prebreza, Senior Security Consultant at Bishop Fox first notified Wodify of his findings more than half a year ago and was told in April that the bugs would be fixed within 90 days.