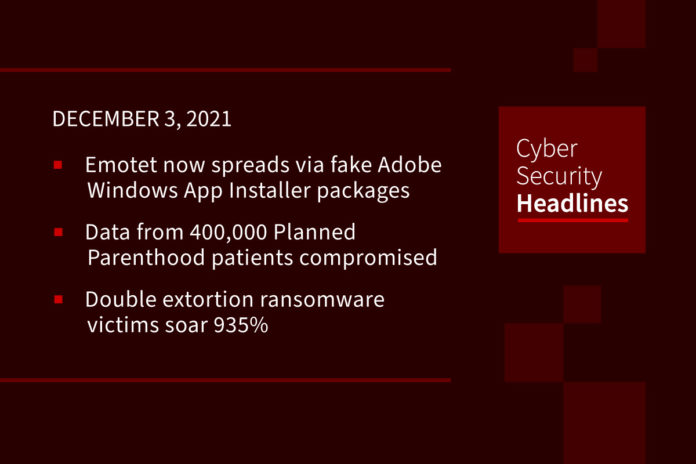
Emotet now spreads via fake Adobe Windows App Installer packages
eCommerce servers are being targeted with remote access malware that hides on Nginx web servers in a way that makes it virtually invisible to security solutions. The threat received the name NginRAT, a combination of the application it targets and the remote access capabilities it provides and is being used in server-side attacks to steal payment card data from online stores. NginRAT was found on eCommerce servers in North America and Europe that had been infected with CronRAT, a remote access trojan (RAT) that hides payloads in tasks scheduled to execute on an invalid day of the calendar. NginRAT has infected servers in the U.S., Germany, and France where it injects into Nginx processes that are indistinguishable from legitimate ones, allowing it to remain undetected.
Data from 400,000 Planned Parenthood patients compromised
Planned Parenthood Los Angeles (PPLA) found suspicious activity on its computer network on October 17. In response to the breach, the organization notified law enforcement and a third-party cybersecurity investigative team, which is conducting an ongoing investigation into the breach. The cybersecurity team determined that a cyberattacker accessed the PPLA network between October 9 and 17, installed malware and ransomware and exfiltrated files containing patient data from the Planned Parenthood system including patient names, birth dates, insurance information and clinical data including diagnosis and treatment information.
Double extortion ransomware victims soar 935%
Group-IB’s Hi-Tech Crime Trends 2021/2022 report covers the period from the second half of 2020 to the first half of 2021. During that time, an “unholy alliance” of initial access brokers and ransomware-as-a-service (RaaS) affiliate programs has led to a surge in breaches, it claimed. In total, the number of breach victims on ransomware data leak sites surged from 229 in the previous reporting period to 2371, Group-IB noted. During the same period, the number of leak sites more than doubled to 28, and the number of RaaS affiliates increased 19%, with 21 new groups discovered. Group-IB warned that, even if victim organizations pay the ransom, their data often end up on these sites.
Jack Dorsey’s Square changes its name to Block
Days after Jack Dorsey resigned as chief executive of Twitter, his other company is changing its name. Square, the digital-payments company he owns and runs, will now go under the new corporate name of Block. The individual businesses owned by Block, “building blocks”, as the company put it, such as Square and music-streaming platform Tidal, retain their original names. This rebrand has been planned for over a year, and as Block states from Twitter, “we’re here to build simple tools to increase access to the economy.”
Thanks to our episode sponsor, Votiro
CISA adds Zoho, Qualcomm, Mikrotik flaws to ‘Must-Patch’ list
The U.S. government’s cybersecurity agency has updated its catalog of “known exploited vulnerabilities” and set deadlines for federal agencies to apply fixes for security defects in software made by Qualcomm, Mikrotik, Zoho and the Apache Software Foundation.
Citing evidence of active exploitation against five specific vulnerabilities, the Cybersecurity and Infrastructure Security Agency (CISA) warned that further delays in applying available fixes “pose significant risk to the federal enterprise.” Federal agencies have until December, 15, 2021 to apply patches for a pair of Zoho ManageEngine ServiceDesk flaws that have been at the center of documented APT attacks over the last few months.
FBI document shows what data can be obtained from encrypted messaging apps
A recently discovered FBI training document shows that US law enforcement can gain limited access to the content of encrypted messages from secure messaging services like iMessage, Line, and WhatsApp, but not to messages sent via Signal, Telegram, Threema, Viber, WeChat, or Wickr. The document, obtained earlier this month following a FOIA request filed by Property of the People, a US nonprofit dedicated to government transparency, appears to contain training advice for what kind of data agents can obtain from the operators of encrypted messaging services and the legal processes they have to go through. A copy of the document is available for view at therecord.media
Nine WiFi routers used by millions were vulnerable to 226 flaws
Security researchers analyzed nine popular WiFi routers and found a total of 226 potential vulnerabilities in them, even when running the latest firmware. The tested routers are made by Asus, AVM, D-Link, Netgear, Edimax, TP-Link, Synology, and Linksys, and are used by millions of people. The front-runners in terms of the number of vulnerabilities are the TP-Link Archer AX6000, having 32 flaws, and the Synology RT-2600ac, which has 30 security bugs.
UK Cabinet Office fined £500,000 over New Year honors list data breach
UK’s data watchdog levied the fine after the home addresses of the 2020 New Year honors recipients were published on 27 December 2019 on the gov.uk website. The Information Commissioner’s Office (ICO) found officials failed to put in place “appropriate technical and organizational measures” to prevent the unauthorized disclosure of personal information in breach of data protection law. The list included prominent public figures such as Elton John, as well as more than a dozen MoD employees and senior counter-terrorism officers.