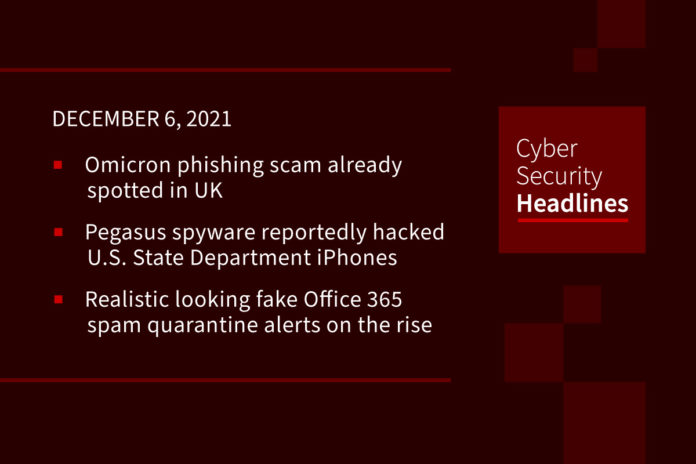
Omicron phishing scam already spotted in UK
U.K. consumer watchdog “Which?” has raised the alarm that a new phishing scam, doctored up to look like official communications from the National Health Service (NHS), is targeting people with offers for free PCR tests for the COVID-19 Omicron variant. Sent by text, email and even offered over the phone, threat actors are contacting people across the U.K. offering them what they say are new test kits specifically designed to detect the Omicron variant. The emails are littered with grammatical errors and ask for £1.24 as a delivery fee giving the scammers access to the target’s banking information as well as standard PII.
Pegasus spyware reportedly hacked iPhones of U.S. State Department and diplomats
Apple reportedly notified several U.S. Embassy and State Department employees that their iPhones may have been targeted by an unknown assailant using state-sponsored spyware created by the controversial Israeli company NSO Group, according to multiple reports from Reuters and The Washington Post. At least 11 U.S. Embassy officials stationed in Uganda or focusing on issues pertaining to the country are said to have been singled out using iPhones registered to their overseas phone numbers, although the identity of the threat actors behind the intrusions, or the nature of the information sought, remains unknown as yet.
Realistic looking fake Office 365 spam quarantine alerts on the rise
A new series of phishing attacks are using fake Office 365 notifications asking the recipients to review blocked spam messages held in quarantine, with the end goal of stealing their Microsoft credentials. The emails use quarantine[at]messaging.microsoft.com address with an official Office 365 logo and other standard footer material. Details of the quarantined spam message are provided along with personalized subject headings to create a sense of urgency. However, they still come with text formatting issues and out-of-place extra spaces that would allow spotting these emails’ malicious nature on closer inspection.
Cuba ransomware gang hacked 49 US critical infrastructure organizations
A flash alert published by the FBI has reported that Cuba ransomware actors have compromised at least 49 entities in five critical infrastructure sectors, including but not limited to the financial, government, healthcare, manufacturing, and information technology sectors. The group’s ransomware encrypts files on the targeted systems using the “.cuba” extension. Cuba ransomware has been actively distributed through the Hancitor malware, a commodity malware that partnered with ransomware gangs to help them gain initial access to target networks.
Thanks to our episode sponsor, Tines
Phishing scam targets military families
Threat researchers at Lookout are helping to take down a phishing campaign targeting members of the United States military and their families. The scammers impersonate military support organizations and personnel to commit advance fee fraud, stealing sensitive personal and financial information for monetary gain. The campaign uses a series of websites designed to appear as though they are affiliated with the military, including Department of Defense services advertisements for extra realism. Researchers were able to pinpoint Nigeria as the source of the scam from a phone number that one of the web developers accidentally left on the draft version of the site.
CISA warns of vulnerabilities in Hitachi Energy products
(CISA) has published six advisories to inform organizations about the availability of security patches and notifications for vulnerabilities impacting RTU500 series bidirectional communication interface, Relion protection and control IEDs, Retail Operations and Counterparty Settlement and Billing (CSB) software, the Asset Performance Management (APM) Edge software for transformers, and the PCM600 update manager. The security flaws can allow threat actors to trigger a DoS condition, execute arbitrary code, eavesdrop on traffic, access or modify data, install untrusted software packages. Some of the flaws are remotely exploitable. The full list of the advisories is available on the Hitachi website.
Feds charge two men with claiming ownership of others’ songs to steal YouTube royalty payments
The US Attorney’s Office of Arizona on Wednesday announced the indictment of two men on charges that they defrauded musicians and associated companies by claiming more than $20m in royalty payments for more than 50,000 songs played on YouTube. The men perpetrated their fraud by falsely representing to YouTube and to an intermediate company responsible for enforcing their music library, that they were the owners of a wide swath of music and that they were entitled to collect any resulting royalty payments. YouTube has not yet respond to a request from the Register for comment.
Virtual yacht sells in the Sandbox metaverse
The Sandbox is a metaverse in which users can monetize virtual spaces and experiences using Ethereum currency to make purchases. The most expensive NFT in the history of the metaverse has just been sold, a luxury yacht with a value of $650,000. The virtual mega yacht, named “The Metaflower” has a DJ booth, helicopter landing strips and a Jacuzzi among other amenities. However, what really makes it interesting is that the ship will have access to the “Fantasy Marina”, a set of 100 private islands with luxury homes being developed by the same developers who built the ship.
(Entrepreneur.com)