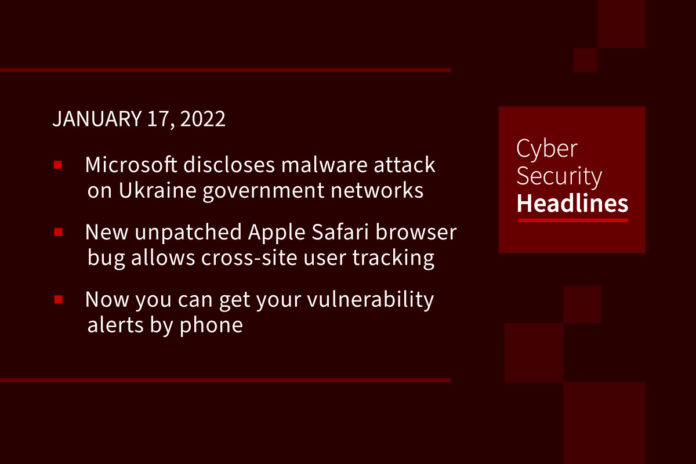
Microsoft discloses malware attack on Ukraine government networks
Microsoft said late Saturday that dozens of computer systems at an unspecified number of Ukrainian government agencies have been infected with destructive malware disguised as ransomware.The disclosure suggesting an attention-grabbing defacement attack on official websites was a diversion. The extent of the damage was not immediately clear. The disclosure followed a Reuters report earlier in the day quoting a top Ukrainian security official as saying the defacement was indeed cover for a malicious attack.
(AP News)
New unpatched Apple Safari browser bug allows cross-site user tracking
A software bug introduced in Apple Safari 15’s implementation of the IndexedDB API could be abused by a malicious website to track users’ online activity in the web browser and worse, even reveal their identity. The vulnerability, dubbed IndexedDB Leaks, was disclosed by fraud protection software company FingerprintJS, which reported the issue to the iPhone maker on November 28, 2021. IndexedDB is a low-level JavaScript application programming interface (API) provided by web browsers for managing a NoSQL database of structured data objects such as files and blobs. “This is a huge bug,” developer advocate for Google Chrome Jake Archibald tweeted. “On OSX, Safari users can (temporarily) switch to another browser to avoid their data leaking across origins. iOS users have no such choice, because Apple imposes a ban on other browser engines.”
Microsoft Defender weakness lets hackers bypass malware detection
Threat actors can take advantage of a weakness that affects Microsoft Defender antivirus on Windows to learn locations excluded from scanning and plant malware there. The issue has persisted for at least eight years, according to some users, and affects Windows 10 21H1 and Windows 10 21H2. Like any antivirus solution, Microsoft Defender lets users add locations (local or on the network) on their systems that should be excluded from malware scans. This is usually done to prevent antivirus from affecting the functionality of legitimate applications that are erroneously detected as malware. Security researchers discovered that the list of locations excluded from Microsoft Defender scanning is unprotected and any local user can access it.
Linux malware sees 35% growth during 2021
The number of malware infections targeting Linux devices rose by 35% in 2021, most commonly to recruit IoT devices for DDoS (distributed denial of service) attacks. IoTs are typically under-powered “smart” devices running various Linux distributions and are limited to specific functionality. However, when their resources are combined into large groups, they can deliver massive DDoS attacks to even well-protected infrastructure. Besides DDoS, Linux IoT devices are recruited to mine cryptocurrency, facilitate spam mail campaigns, serve as relays, act as command and control servers, or even act as entry points into corporate networks.
Thanks to our episode sponsor, Datadog

North Korea pulled in $400m in cryptocurrency heists last year
The North Korean government made off with almost $400m in digital cash last year, according to a report from Chainalysis. The attackers went after investment houses and currency exchanges to steal the cryptocurrencies, using use mixing software to make masses of micropayments to new wallets, before consolidating them all again into a new account and moving the funds. Bitcoin used to be a top target but Ether is now the most stolen currency, accounting for 58 per cent of the funds filched.
Russian court remands REvil hackers
A Moscow court on Saturday remanded eight hackers in custody for two months as Russia cracks down on the REvil cybercrime group. Eight members of the prominent hacking group Moscow’s Tverskoi district court to remain in custody until mid-March. They could face up to seven years in prison if convicted. On Friday, Russia said it had dismantled the hacking group REvil, which carried out a high-profile attack last year on US software firm Kaseya, following a request from Washington.
How quick thinking stopped a ransomware attack from crippling a Florida hospital
CNN.com on Sunday carried a feature story about Jamie Hussey, IT director at Jackson Hospital in south Florida, which was recently hit by the Mespinoza ransomware. Hussey quickly realized that the charting software, which was maintained by an outside vendor, had been infected. The article describes his fast switch to “downtime procedures” meaning shifting staff to pen and paper while physically disconnecting the hospital’s electronic health records system from the rest of the computer network to check them for malicious code before reconnecting to the system. Although a story about a hospital being attacked is nothing new, the article shows how Hussey and his newly hired assistant – a cybersecurity graduate – took the reins to ensure a safe recovery for the hospital and its patients. “”Lock it down and piss people off,” he said, adding, “It’s what you have to do just to secure your network.” The article is available at CNN.com – do an internal search for Florida, hospital, ransomware, or check our link at CISOSeries.com.
(CNN)
Now you can get your vulnerability alerts by phone
An infosec pro fed up with having to follow tedious Twitter accounts to stay on top of cybersecurity developments has set up a website that phones you if there’s a new vuln you really need to know about. Bugalert, founded by product manager Matt Sullivan, is a crowdsourced venture that he hopes will take the pain out of trying to tell the signal from the noise when security researchers make high-impact vulnerability disclosures. Bugalert will depend on vetted volunteers who send push alerts to registered subscribers. Bugalert’s GitHub page lets Sullivan “select a number of repository maintainers who are geographically dispersed” for round-the-clock coverage.”