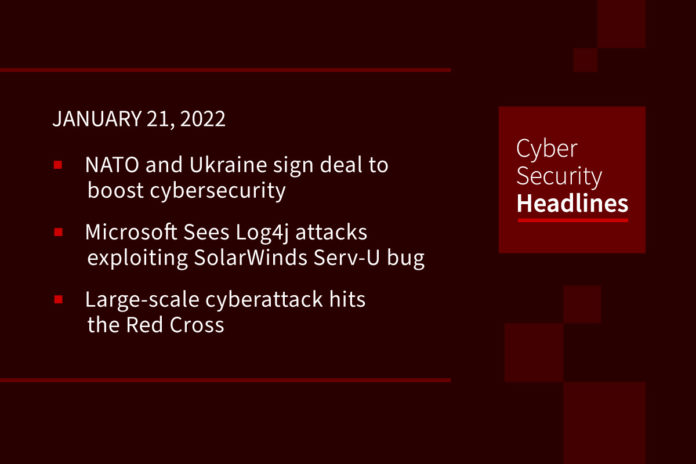
NATO and Ukraine sign deal to boost cybersecurity
The agreement comes after a series of cyberattack incidents in Ukraine and heightened tensions over Russia’s invasion. According to a statement from NATO’s Secretary-General Jens Stoltenberg, cybersecurity experts from NATO will be working together with Ukraine to confront the rising cyberthreats in the region. The new cybersecurity collaboration allows Ukrainian access to NATO’s malware information sharing platform along with enhanced cyber cooperation.
(CISOMag)
Microsoft Sees Log4j attacks exploiting SolarWinds Serv-U bug
Threat actors have weaponized a newly discovered bug in SolarWinds Serv-U file-sharing software to launch Log4j attacks against networks’ internal devices, Microsoft warned on Wednesday. SolarWinds issued a fix the day before, on Tuesday. The vulnerability, tracked as CVE-2021-35247, is an input validation flaw that could allow attackers to build a query, given some input, and to send that query over the network without sanitation, Microsoft’s Threat Intelligence Center (MSTIC) said.
Large-scale cyberattack hits the Red Cross
A cyberattack compromised personal and confidential data on more than half a million people helped by at least 60 Red Cross and Red Crescent organizations around the world, the International Committee of the Red Cross announced Wednesday. The organization said the exposed information belonged to highly vulnerable groups, including families separated by conflict. As a result of the attack, the ICRC temporarily shut down its “Restoring Family Links” program, which helps reunite families separated by conflict, disaster, or migrations. The ICRC is “working as quickly as possible to identify workarounds to continue this vital work,” according to a news release.
Crypto.com confirms accounts hacked, $34 million withdrawn
The world’s third-largest cryptocurrency has confirmed that a multi-million dollar cyberattack led to the compromise of around 400 of its customers’ accounts. The company’s CEO Kris Marszalek told Bloomberg Live that customer funds are not at risk. The total amount of unauthorized withdrawals across different cryptocurrencies was totaled at approximately US$34 million and affected 483 Crypto.com users. “In the majority of cases, we prevented the unauthorized withdrawal, and in all other cases customers were fully reimbursed. “
Thanks to our episode sponsor, Datadog

OpenSea goes down, taking NFTs and cryptowallets with it
OpenSea, one of the most popular marketplaces for non-fungible tokens or NFTs, is suffering a “database outage,” the company announced on Thursday. As a result, several services which rely on OpenSea’s APIs, including the popular crypto wallet MetaMask, are having trouble displaying NFTs. In other words, because OpenSea is down, some NFT owners who just bought their tokens may not be able to see their expensive JPEGs even in their crypto wallet. Security researcher Jane Manchun Wong, stated “I just think too many platforms are reliant on OpenSea. And it becomes a single point of failure, especially when OpenSea has not been stable lately,” Wong told Motherboard in an online chat.
(Vice)
FBI links Diavol ransomware to the TrickBot cybercrime group
The TrickBot Gang, aka Wizard Spider, are the developers of malware infections that have played havoc on corporate networks for years, commonly leading to Conti and Ryuk ransomware attacks, network infiltration, financial fraud, and corporate espionage. The TrickBot Gang is most known for the TrickBot banking trojan, but is also behind the development of the BazarBackdoor and Anchor backdoors. In June 2021, researchers noticed Diavol and Conti ransomware payloads deployed on a network in the same ransomware attack. After analyzing the two ransomware samples, similarities were discovered, such as their use of asynchronous I/O operations for file encryption queuing and almost identical command-line parameters for the same functionality. The FBI was likely able to formally link Diavol to the TrickBot Gang after the arrest of Alla Witte, a Latvian woman involved in the development of ransomware for the malware gang.
Box 2FA bypass opens user accounts to attack
Researchers at Varonis Threat Labs have revealed that a bypass on the cloud-based file-sharing service, which claims 97,000 companies and 68 percent of the Fortune 500 as customers, worked on accounts that used one-time SMS codes for two-factor authentication (2FA) verification. In a proof-of-concept exploit, they were able to achieve the bypass by stealing a session cookie. This cookie comes when a one time password is set up by Box to be sent to a customer by SMS. If the user doesn’t navigate to the verification page, no SMS code is generated, but a session cookie still is.
Zoom vulnerabilities impact clients, MMR servers
Two vulnerabilities recently disclosed to Zoom could have led to remote exploitation in clients and MMR servers, researchers say. On Tuesday, Project Zero researcher Natalie Silvanovich published an analysis of the security flaws, the results of an investigation inspired by a zero-click attack against the videoconferencing tool demonstrated at Pwn2Own. Silvanovich found two different bugs, a buffer overflow issue that impacted both Zoom clients and Zoom Multimedia Routers (MMRs), and the other was an information leak security flaw central to MMR servers. A lack of Address Space Layout Randomization (ASLR), a security mechanism to protect against memory corruption attacks, was also noted. The vulnerabilities were reported to the vendor and patched on November 24, 2021. Zoom has since enabled ASLR.
(ZDNet)