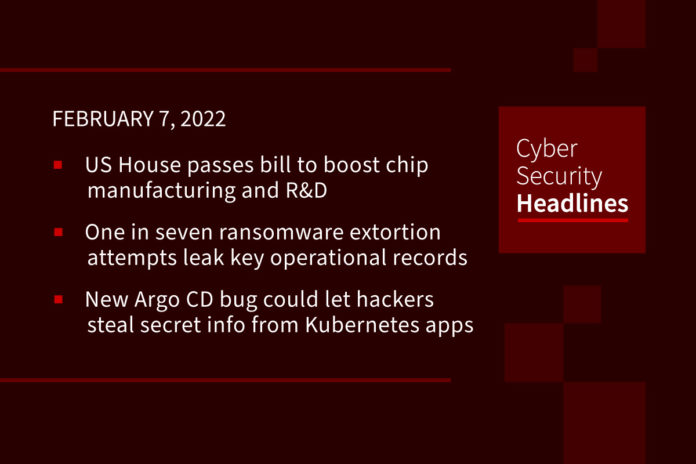
US House passes bill to boost chip manufacturing and R&D
On Friday the US House of Representatives passed a bill that will to equip America to boost semiconductor production and lift its economy to better compete with China. The law bill, called America Competes Act of 2022, includes $52bn in funding to help semiconductor companies build new factories, and to fund research and development. The draft legislation also earmarks $45bn in funding to boost the supply chain and alleviate problems related to chip shortages, which have hit key sectors, such as consumer electronics and automotive. The next step is reconciliation with the US Senate’s version of the bill, the US Innovation and Competition Act, which passed in last June.
One in seven ransomware extortion attempts leak key operational tech records
Once, ransomware was used en masse to infect systems and extort blackmail payments from the general public, normally in cryptocurrency such as Bitcoin (BTC), but now, operators are targeting high-value targets for larger payoffs. In what some cybersecurity experts call “big game hunting,” ransomware groups go for large enterprise firms, utilities, hospitals, and key supply chain players. Research performed independently by Mandiant and Cisco Secure show how thieves will patiently penetrate networks in order to steal employee credentials, asset tags, third-party vendor agreements and legal documents, project files, product diagrams, process documents, spreadsheets, visualizations, and in one case, the proprietary source code of a satellite vehicle tracker’s GPS platform. Access to this type of data can enable threat actors to learn about an industrial environment, identify paths of least resistance, and engineer cyber-physical attacks.
(ZDNet)
New Argo CD bug could let hackers steal secret info from Kubernetes apps
Users of the Argo continuous deployment (CD) tool for Kubernetes are being urged to push through updates after a zero-day vulnerability was found that could allow an attacker to extract sensitive information such as passwords and API keys. The flaw, tagged as CVE-2022-24348, with a CVSS score of 7.7, affects all versions and has been addressed in versions 2.3.0, 2.2.4, and 2.1.9. Cloud security firm Apiiro has been credited with discovering and reporting the bug on January 30, 2022. Argo CD is officially used by 191 organizations, including Alibaba Group, BMW Group, Deloitte, Gojek, IBM, Intuit, LexisNexis, Red Hat, Skyscanner, Swisscom, and Ticketmaster.
BlackCat ransomware linked to BlackMatter, DarkSide gangs
The Black Cat ransomware gang, also known as ALPHV, has confirmed they are former members of the notorious BlackMatter/DarkSide ransomware operation. BlackCat is a new feature-rich ransomware operation launched in November 2021 and developed in the Rust programming language, which is unusual for ransomware infections. The ransomware executable is highly customizable, with different encryption methods and options allowing for attacks on a wide range of corporate environments. While the ransomware gang calls themselves ALPHV, security researcher MalwareHunterTeam named the ransomware BlackCat after the image of a black cat used on every victim’s Tor payment page.
Thanks to our episode sponsor, Datadog

In this Datadog Security Monitoring product brief, you’ll learn how to:
Solve cloud complexity challenges with threat detection tools, detect and analyze security threats anywhere in your stack, and deploy turnkey detection rules mapped to the MITRE ATT&CK framework. Download the brief today to learn more at datadoghq.com/ciso/
FBI shares Lockbit ransomware technical details, defense tips
The Federal Bureau of Investigation (FBI) has released technical details and indicators of compromise associated with LockBit ransomware attacks in a new flash alert published this Friday. It also provided information to help organizations block this adversary’s attempts to breach their networks and asked victims to urgently report such incidents to their local FBI Cyber Squad. The LockBit ransomware gang has been very active since September 2019 when it launched as a ransomware-as-a-service (RaaS), and the gang is now also trying to remove the intermediaries by recruiting insiders to provide them with access to corporate networks via Virtual Private Network (VPN) and Remote Desktop Protocol (RDP).
FBI’s warning about Iranian firm highlights common cyberattack tactics
The FBI has released a warning outlining the tactics, techniques, and protocols of Iran-based Emennet Pasargad, reportedly a cybersecurity and intelligence firm servicing Iranian government agencies, to help recipients inform and defend themselves against the group’s malicious activities. The FBI’s Private Industry Notification, issued last week, lists the most common and recent CVEs (common vulnerabilities and exposures) Emennet has been found to exploit. They also describe their techniques, such as exploiting open-source tools like web pages running PHP code or pages with externally accessible MySQL databases. The notification also pointed out how Emennet ran an interference campaign during the US 2020 election, obtaining confidential voter information from state election websites, sending intimidating emails to voters, crafting and distributing misinformation videos about voting vulnerabilities, and hacking into media companies’ computer networks.
Elementor WordPress plugin has a gaping security hole
Owners of WordPress sites that use the Elementor website creation toolkit are being warned of a security hole that combines data leakage and remote code execution, if they are incorporating a plugin called Essential Addons for Elementor, a popular tool for adding visual features such as timelines, image galleries, ecommerce forms and price lists. This is due to a file inclusion vulnerability in the product which makes it possible for attackers to trick the plugin into accessing and including a server-side file using a filename supplied in the incoming web request. Users should upgrade to version 5.0.6 or later.
German court rules websites embedding Google fonts violates GDPR
A regional court in the German city of Munich has ordered a website operator to pay €100 in damages for transferring a user’s personal data — i.e., IP address — to Google via the search giant’s Fonts library without the individual’s consent. The unauthorized disclosure of the plaintiff’s IP address by the unnamed website to Google constitutes a contravention of the user’s privacy rights, the court said, adding the website operator could theoretically combine the gathered information with other third-party data to identify the “persons behind the IP address.” GDPR considers IP addresses, advertising IDs, and cookies to be personal identifiable information (PII), making it mandatory for businesses to seek users’ explicit permission before processing such information.