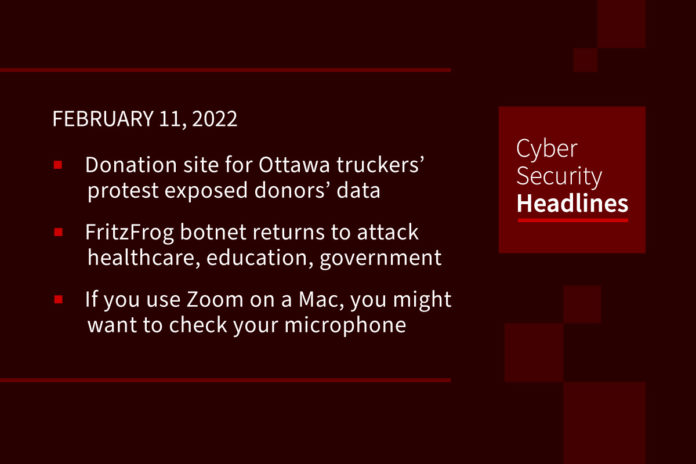
Donation site for Ottawa truckers’ “Freedom Convoy” protest exposed donors’ data
The donation site used by truckers in Ottawa who are currently protesting against national vaccine mandates has fixed a security lapse that exposed passports and driver licenses of donors. The Boston, Massachusetts-based donation service GiveSendGo became the primary donation service for the so-called “Freedom Convoy” last week after GoFundMe froze millions of dollars in donations, citing police reports of violence and harassment in the city that violated its terms of use. TechCrunch was tipped off to the data lapse after a person working in the security space found an exposed Amazon-hosted S3 bucket containing over 50 gigabytes of files, including passports and driver licenses that were collected during the donation process.
FritzFrog botnet returns to attack healthcare, education, government sectors
FritzFrog is a peer-to-peer botnet discovered in January 2020. Over a period of eight months, the botnet managed to strike at least 500 government and enterprise SSH servers. Written in Golang, it is decentralized in nature and will attempt to brute-force servers, cloud instances, and other devices — including routers — that have exposed entry points on the internet. In total, 24,000 attacks have been detected to date. And 1,500 hosts have been infected, the majority of which are located in China. The botnet is used to mine for cryptocurrency, and healthcare, education, and government sectors are all on the target list. The malware is also being prepared to hone in on websites running the WordPress content management system (CMS).
(ZDNet)
If you use Zoom on a Mac, you might want to check your microphone settings
Mac users running the Zoom meetings app are reporting that it’s keeping their computer’s microphone on when they aren’t using it. The issue appears to affect the native app running on the current macOS release, Monterey, in which Apple has implemented a visual cue to alert users that an application or device is accessing their microphone or camera — via an orange or green dot in the Menu Bar, respectively. Users began complaining about the issue after Monterey was released late last year, and on December 27, Zoom Inc put out an update that was meant to address the bug, stating that version 5.9.1 (3506) “resolved an issue regarding the microphone light indicator being triggered when not in a meeting.” However, it clearly hasn’t fixed the issue for everyone.
An increase in regsvr32.exe in Microsoft Office documents
This according to threat research company Uptycs. Regsvr32 is a Microsoft-signed command line utility in Windows which allows users to register and unregister DLLs. This makes it easier for other programs to make use of the functionalities of the DLLs. Threat actors can use regsvr32 for loading COM scriptlets to execute DLLs. This method does not make changes to the Registry as the COM object is not actually registered but executed, and is a technique often referred to as Squiblydoo, which allows threat actors to bypass application whitelisting during the execution phase of the attack kill chain. The full report that includes Indicators of Compromise (IOCs) is available at the uptycs.com website.

In this Datadog Security Monitoring product brief, you’ll learn how to:
Solve cloud complexity challenges with threat detection tools, detect and analyze security threats anywhere in your stack, and deploy turnkey detection rules mapped to the MITRE ATT&CK framework. Download the brief today to learn more at datadoghq.com/ciso/
Spain dismantles SIM swapping group who emptied bank accounts
Spanish National Police have arrested eight suspects allegedly part of a crime ring that drained bank accounts though email, SMS, and social media DMs that all spoofed victims’ banks. The suspects obtained sensitive personal information needed to impersonate the victims and deceive phone store employees into issuing new SIM cards with the same number. Finally, they used the victims’ phone numbers to obtain the one-time passwords that protect e-banking accounts, accessed them, and promptly drained up all the available funds by transferring them to accounts under their control.
WordPress plugin PHP Everywhere can be exploited to execute arbitrary code
Wordfence experts found three critical remote code execution vulnerabilities in the PHP Everywhere WordPress plugin, all the issues have received a CVSS score of 9.9. This is a plugin that allows WordPress admins to insert PHP code in pages, posts, the sidebar, or any Gutenberg block, to display dynamic content based on evaluated PHP expressions. It is used on over 30,000 websites. Experts have pointed out that the patched version 3.0.0 only supports PHP snippets via the Block editor, this means that users who are still relying on the Classic Editor have to uninstall the plugin and chose another solution for using custom PHP code.
Industry reports highlight the most recent and successful cybercrime activities
According to ESET’s Q3 Threat Report, covering September to December 2021, 2021 was defined by the continual discoveries of zero-day vulnerabilities powerful enough to wreak havoc on enterprise systems. The discovery of zero-day flaws in Exchange Server and Microsoft’s emergency patches to resolve the on-premise issues continued to haunt IT administrators well into the year. Brute-force and automated password guessing, such as through dictionary-based attacks, were the most frequent attack vectors detected according to ESET telemetry. Attacks against remote desktop protocol (RDP) increased by 274% during the four-month period.
Also the 2022 Ransomware Threat Report from Syhunt identifies ransomware as today’s most common type of malicious software, with over 150 TB of Data Stolen by Ransomware Groups from over 2800 victim organizations. The Syhunt report also breaks these numbers down by criminal gang with REvil topping the charts with 44.1TB and 282 victim organizations, followed by conti and ragnar_locker. It identified the domain extensions most attacked, which, unsurprisingly are .com, .org, .net, .edu and .gov, with the USA, the UK, France, and Canada being the most attacked countries worldwide. ESET’s report is available at welivesecurity.com, and Syhunt at syhunt.com