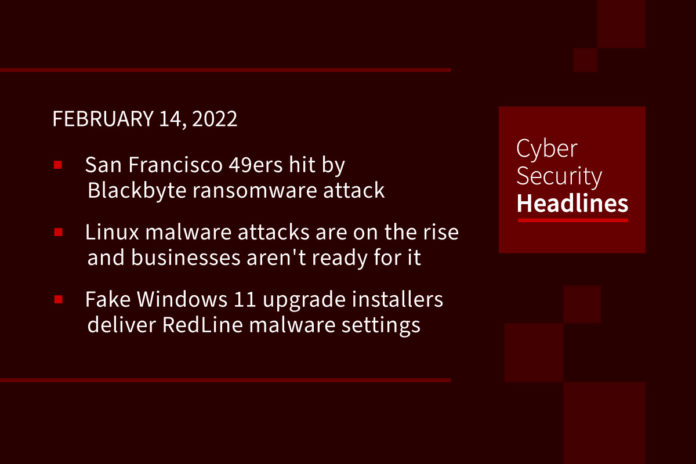
San Francisco 49ers hit by Blackbyte ransomware attack
The 49ers confirmed the attack in a statement to BleepingComputer and said it caused a temporary disruption to portions of their IT network. While the team organization did not confirm whether hackers had successfully deployed the ransomware, they said they are still in the process of recovering systems, indicating that devices were likely encrypted. The leaked data is a 292MB archive of files that the threat actors say are stolen 2020 invoices from the 49ers’ network.
Linux malware attacks are on the rise, and businesses aren’t ready for it
Following up on a strategy we brought you mid-January, Cyber criminals are increasingly targeting Linux servers and cloud infrastructure to launch ransomware campaigns, cryptojacking attacks and other illicit activity – and many organizations are leaving themselves open to attacks. Analysis from cybersecurity researchers at VMware warns that malware targeting Linux-based systems is increasing in volume and complexity, while there’s also a lack of focus on managing and detecting threats against them. This comes after an increase in the use of enterprises relying on cloud-based services because of the rise of hybrid working, with Linux the most common operating system in these environments.
(ZDNet)
Fake Windows 11 upgrade installers deliver RedLine malware
Threat actors have started distributing fake Windows 11 upgrade installers to users of Windows 10, tricking them into downloading and executing RedLine stealer malware. These attacks coincides Microsoft’s announcement of a broad deployment phase for Windows 11, which has given attackers plenty of time to prepare for this move. RedLine is currently the most widely deployed password, browser cookies, credit card, and cryptocurrency wallet info grabber. According to researchers at HP, the actors used the seemingly legitimate “windows-upgraded.com” domain to distribute the malware.
Rising popularity of VR headsets sparks 31% rise in insurance claims
The trend of crashing into furniture while in the metaverse provoked a 31% jump in home contents claims involving VR headsets last year, insurer Aviva said, marking a 68% overall increase since 2016. Aviva’s UK office said the average VR-related claim for accidental damage in 2021 was about £650, often from broken TVs smashed by overenthusiastic gamers.
Thanks to our episode sponsor, PlexTrac

Check out PlexTrac.com/CISOSeries to learn why PlexTrac is the perfect platform for CISOs!
Google paid record $8.7 million to bug hunters in 2021
Google’s Android, Chrome, and Play platforms continue to be vulnerability-rich environments for bad actors. This is why last year Google paid a record $8.7 million in rewards to 696 third-party bug hunters from 62 countries who discovered and reported thousands of vulnerabilities in the company’s technologies. That amount represented a near 30% increase from the $6.7 million Google paid in 2020. Some of the increase had to do with higher payouts for certain kinds of bug discoveries. But a lot also had to do with the relatively high number of flaws that researchers are continuing to unearth in some of Google’s core technologies.
Bug keeps Mazda radios locked in to NPR
Owners of 2014-17 year Mazdas, in the Washington state’s Puget Sound area, were surprised to discover their cars’ infotainment systems were permanently locked in to the local NPR network. The cause was discovered to be missing file extensions in album images sent with its digital-radio broadcast. This also stopped the cars’ users from using Bluetooth. The fix requires the replacement of the $1,500 connectivity master unit, reports say.But Mazda said customers could apply for a free “goodwill” replacement.
(BBC News)
Amazon steps in to close exposed FlexBooker bucket after second data breach
Digital scheduling platform FlexBooker has been accused of exposing the sensitive data of millions of customers, according to security researchers at vpnMentor. The researchers said the Ohio-based tech company was using an AWS S3 bucket to store data but did not implement any security measures, leaving the contents totally exposed and easily accessible to anyone with a web browser. The 19 million exposed files included full names, email addresses, phone numbers and appointment details. vpnMentor said they had contacted the company and Amazon about the issue. Flexbooker merely sent back an automatic reply about an earlier the leak, so vpnMentor turned to Amazon. In January, Australian security expert Troy Hunt, who runs the Have I Been Pwned site that tracks breached information, said the first trove of stolen data included password hashes and partial credit card information for some accounts. Hunt added that the data “was found being actively traded on a popular hacking forum.”
((ZDNet)
How phishers are slinking their links into LinkedIn
Spammers and phishers are taking advantage of a marketing feature on LinkedIn which lets them create a LinkedIn.com link that bounces a user’s browser to other websites, such as phishing pages that mimic top online brands. At issue is a “redirect” feature available to businesses that chose to market through LinkedIn.com. These links, called “Slinks,” currently have a standard format within the URL such as https://www.linkedin.com/slink? followed by a short alphanumeric variable. On his blog, Brian Krebs points out just how easy it is for LinkedIn members to click on a link sent by a fellow member via a message, in which the slink word will be overlooked.