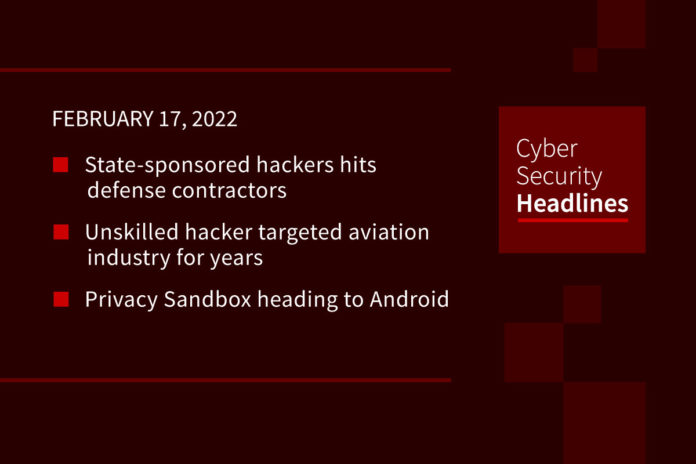
State-sponsored hackers hits defense contractors
A new alert issued by CISA, the FBI and NSA claims that state-sponsored hackers linked to Russia targeted cleared defense contractors and subcontractors over the course of several years. Compromised contractors supported the US Army, Air Force, DoD and intelligence agencies, with the actors acquiring export-controlled technology and sensitive unclassified information. The alert says the exfiltrated information “provides significant insight into U.S. weapons platforms development and deployment timelines, vehicle specifications, and plans for communications infrastructure and information technology.” The agencies expect these same actors to continue targeting defense contracts into the foreseeable future.
Unskilled hacker targeted aviation industry for years
According to a new report by Proofpoint, a threat actor dubbed TA2541 has been active since 2017, believed to be operating out of Nigeria and targeting aviation, aerospace, transportation, manufacturing, and defense industries. For most of this time, the threat actor’s tactics involve sending malicious Microsoft Word documents to deliver off-the-shelf remote access trojans, with campaigns sending out hundreds of thousands of emails, mainly in English. Recently it transitioned to using cloud hosted payloads in emails. The threat actor seems focused on collecting information, although its unclear what is its ultimate goal. TA2541 doesn’t customize emails for different organizations and roles, and isn’t particularly stealthy, yet still has been operating for over five years.
Privacy Sandbox heading to Android
Google’s Privacy Sandbox initiative is a set of principles aiming to reduce the amount of personal information exposed to third-party advertisers. You probably know most about it in relation to Google’s ambition to replace third-party cookies. This has met with a lot of pushback from publishers and regulators, with Google forced to withdraw its original Federated Learning of Cohorts implementation proposal. The search giant now announced it plans to bring a beta developer preview of Privacy Sandbox to Android by the end of 2022. Google wants developer feedback on the system, which is still in active development. The initial announcement didn’t include a lot of technical details, just an overview of its goals. Google will support its existing ad platform for at least the next two years.
(CNet)
Crypto coalition creates anti-money laundering standard
We’ve covered crypto-based money laundering on this show several times. While suspected money laundering in cryptocurrency is a smaller percentage of transactions compared to fiat currency, crypto exchanges have lacked the same visibility tools to really prevent it. Now a coalition of large crypto firms, including Coinbase, Robinhood and BlockFi, began rolling out Travel Rule Universal Solution Technology, or TRUST as an anti-money laundering standard. This provides a way for virtual asset service providers to gather and send names, account numbers and location information on senders and recipients using end-to-end encrypted channels. Traditional financial institutions have long had these types of systems in place.
Thanks to our episode sponsor, PlexTrac

Check out PlexTrac.com/CISOSeries to learn why PlexTrac is the perfect platform for CISOs!
Twitter’s Safety Mode gets a wider rollout
Twitter started testing its Safety Mode with a group of 750 testers in September. The company now launched a beta for the program, available to about 50% of users in its English-speaking markets. Once enabled, Safety Mode automatically blocks accounts replying with harmful language or repeated messages for seven days. The beta also gets some new features for Safety Mode, Twitter will now actively monitor responses and suggest when to enable the feature, in the event a tweet goes viral and a user potentially doesn’t know its available. It’s unclear when Safety Mode will get a rollout to other languages or a global release on the platform.
Red Cross hit by APT
The International Committee of the Red Cross published an update on the cyberattack that hit the organization. The Red Cross disclosed the attack on January 18th, but this update now dates the initial intrusions to November 9th, saying it was a “highly-sophisticated” attack, likely from a state-sponsored actor. The attack used code designed specifically to target servers within Red Cross infrastructure, leading to compromised data on over 500,000 “highly vulnerable” people. A report from Palo Alto Networks linked the methods used in the Red Cross attack to a Chinese state-sponsored group, known as APT27, but the Red Cross did not name any specific group.
Proctoring service sets up cheating honeypots
The Markup covered an online proctoring tool called Honorlock, which used AI to monitor remote students for any cheating during tests. This involves everything from using facial recognition for verifying identity to searching for leaked questions online. Computer science student Kurt Wilson discovered the service also tracks students through seed sites, effectively fake cheating websites that act as a honeypot for students. By analyzing common code and test questions, Wilson found a dozen seed sites set up by HonorLock over a year, with five still active. Clicking on answers to questions on these sites shares details on typing and mouse movements with Honorlock, which is combined with IP addresses to produce evidence of students looking up information on other devices. It’s unknown how many students have been caught using these honeypots.
Pixelating text still leaks information
Security researcher Dan Petro with the security firm Bishop Fox developed a tool to perform dictionary attacks against text obfuscated by pixelation. Pixelation replaces text with pixels representing average values, something that Petro believed could still carry significant information. The tool is called Unredacter, published on Github as an open source project. The tool is intentionally manual, although Petro says there’s no reason it couldn’t be processed automatically within the app for an enterprising developer.