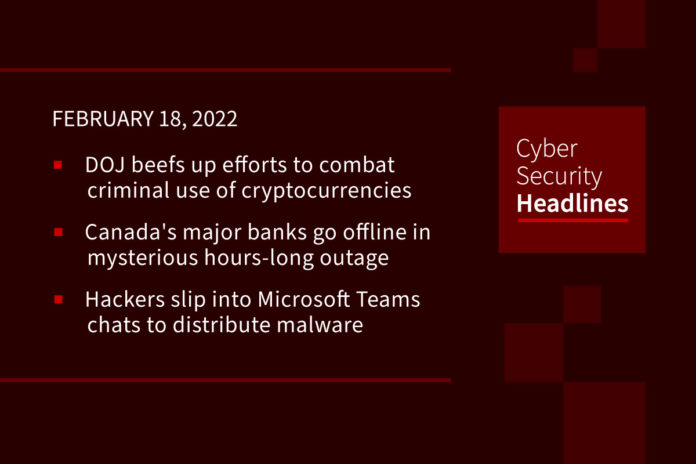
DOJ beefs up efforts to combat criminal use of cryptocurrencies
Speaking at the Munich Cyber Security Conference, Deputy Attorney General Lisa Monaco said that the National Cryptocurrency Enforcement Team (NCET) — unveiled in October as part of an overall U.S. government focus on combatting ransomware operators — is getting its first director: Eun Young Choi. Choi is a seasoned federal cybersecurity prosecutor who most recently led the prosecution of Andrei Tyurin. Seeking to “bust the business model” of the bad guys, the team is now up to a dozen prosecutors, some of whom are involved in the recent case of the Bitfinex couple who were arrested in NYC in a bitcoin laundering scam. The Department of Justice said it had seized more than $3.6 billion in cryptocurrency as part of the case, its largest recovery to date.
Canada’s major banks go offline in mysterious hours-long outage
Canada’s five major banks went offline yesterday impeding access to e-transfers, online and mobile banking services for many. Reports of users having trouble getting to their online banking peaked between 5 p.m. and 6 p.m. Eastern time on Wednesday, although observers have reported seeing problems on Thursday as well. The cause is still under investigation.
Hackers slip into Microsoft Teams chats to distribute malware
Researchers at Avanan, state in a report released yesterday, that hackers have started to drop malicious executable files in conversations on Microsoft Teams communication platform. The attacks started in January, the company says in a report today, and the threat actor inserts in a chat an executable file called “User Centric” to trick the user into running it. Once executed, the malware writes data into the system registry installs DLLs and establishes persistence on the Windows machine. The method used to gain access to Teams accounts remains unclear but some possibilities include stealing credentials for email or Microsoft 365 via phishing or compromising a partner organization.
Researchers block “largest ever” bot attack
Security researchers claim to have stopped the largest bot attack they’ve ever seen, leveraging 400,000 compromised IP addresses to scrape web data. Imperva said the large-scale botnet generated 400 million requests from the IP addresses over four days, comprising around 10 requests per IP per hour on average. Its mitigation service spotted the 30-fold surge in traffic volume to the impacted site and mitigated the attack. The victim in this case was a job listings site with a presence in six countries. The attack was designed to harvest job seekers’ profiles from the site.
Thanks to our episode sponsor, PlexTrac

Check out PlexTrac.com/CISOSeries to learn why PlexTrac is the perfect platform for CISOs!
Cisco bug can let hackers crash Cisco Secure Email gateways
Cisco has addressed a high severity vulnerability that could allow remote attackers to crash Cisco Secure Email appliances using maliciously crafted email messages. The security flaw (tracked as CVE-2022-20653) was found in DNS-based Authentication of Named Entities (DANE), a Cisco AsyncOS Software component used by Cisco Secure Email to check emails for spam, phishing, malware, and other threats. “An attacker could exploit this vulnerability by sending specially formatted email messages that are processed by an affected device,” Cisco explained. The company’s Product Security Incident Response Team (PSIRT) said that it found no evidence of malicious exploitation in the wild before the security advisory was published on Wednesday.
Trickbot abuses top brands in attacks against customers
On February 16, Check Point Research published a new study on Trickbot, noting that the malware is now being used in targeted attacks against customers of 60 “high profile” organizations, many of whom are located in the United States. The companies themselves are not the victims of the malware. Instead, TrickBot operators are leveraging the brands’ reputations and names in numerous attacks. According to the study, the brands being abused by TrickBot include the Bank of America, Wells Fargo, Microsoft, Amazon, PayPal, American Express, Robinhood, Blockchain.com, and the Navy Federal Credit Union, among others.
(ZDNet)
FBI sees increase in use of virtual meeting platforms for BEC scams
No longer restricted to email, the FBI has stated, in a security alert published yesterday, that the recent shift to online working caused by the ongoing COVID-19 pandemic has also had an impact on how some recent BEC attacks are also taking place. Three scenarios they identify are: 1.) compromising the email of a CEO or CFO, and requesting employees to participate in a virtual meeting platform where the criminal will insert a still picture of the CEO with no audio, or “deep fake” audio, and then proceed to instruct employees to initiate transfers of funds via the virtual meeting platform chat or in a follow-up email.2.) Compromising employee emails to insert themselves in workplace meetings via virtual meeting platforms to collect information on a business’s day-to-day operations; And 3.) Compromising the email of a CEO, and sending spoofed emails to employees instructing them to initiate transfers of funds, as the CEO claims to be occupied in a virtual meeting and unable to initiate a transfer of funds via their own computer
Power company’s rather shocking payout
A series of storms in November 2021 in northern and north-eastern parts of the UK brought down powerlines in some areas, leaving many homes without electricity for several days. British power companies, are privatized, are required to pay out compensation to customers who did not receive the service promised in their contract. This was interesting news to Northern Powergrid customer Gareth Hughes, who received a compensation check in the amount of two trillion, three hundred and twenty four billion, two hundred and fifty two million, eighty thousand and one hundred and ten pounds. Given that the amount to be paid out was slightly larger than the annual GDP of the entire UK, Mr. Hughes decided not to slide the check into his bank’s ATM. Although this is some regard a comical story, industry watchers question the efficacy of error detection codes, suggesting that such oversights could lead to much larger problems, especially for infrastructure organizations.