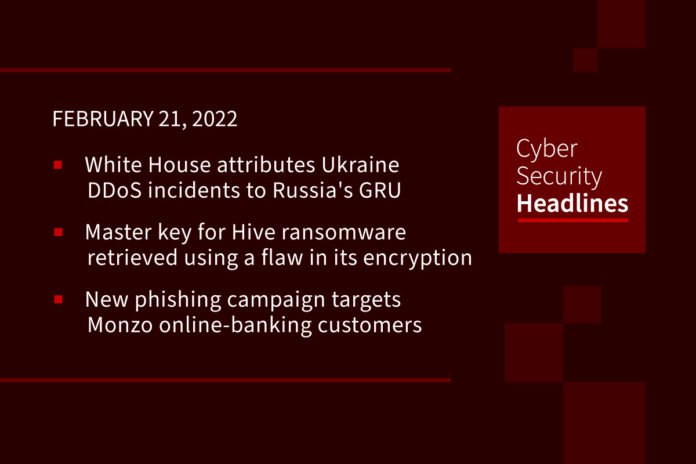
White House attributes Ukraine DDoS incidents to Russia’s GRU
Following up on a story we brought you last week, Anne Neuberger, deputy national security adviser for cyber and emerging technology has stated that Russia was behind recent DDoS disruptions of Ukrainian government and banking websites last week. Neuberger said the U.S. has “technical information” that shows digital infrastructure belonging Russia’s main intelligence directorate, the GRU, “transmitting high volumes of communication to Ukraine-based IP addresses and domains.” The DDoS incidents were of “limited impact” she said, “because Ukrainian cyberdefenders rapidly brought back the state-owned banks and the Ministry of Defense networks.” The U.S. has provided support to Ukraine as part of the incident response, Neuberger said.
Master key for Hive ransomware retrieved using a flaw in its encryption algorithm
Researchers have detailed what they call the “first successful attempt” at decrypting data infected with Hive ransomware without relying on the private key used to lock access to the content, by using a cryptographic vulnerability identified through analysis,” this according to a group of academics from South Korea’s Kookmin University. Hive leverages a variety of initial compromise methods, including vulnerable RDP servers, compromised VPN credentials, as well as phishing emails with malicious attachments, and uses double extortion. It currently the eighth spot among the top 10 ransomware strains by revenue in 2021.
New phishing campaign targets Monzo online-banking customers
Monzo is a 100% online banking platform in the UK with over four million customers and among the first to challenge the traditional financial managing system. In a new report, security researcher William Thomas explains that the phishing process begins with the arrival of a faked SMS text showing Monzo as the sender’s name, asking the recipient to tap the provided link to reactivate their session or verify their account. The users are taken to a phishing site that displays a fake email login form and then requests information about their Monzo account, including full name, phone number, and the Monzo PIN. Monzo states that it never uses SMS to communicate with customers.
Threat actors stole at least $1.7M worth of NFTs from tens of OpenSea users
The world’s largest NFT exchange, OpenSea on Sunday confirmed that dozens of its users have been hit by a phishing attack and had lost valuable NFTs worth $1.7 million. Analysis of the attacker’s wallet, done through blockchain analysis, revealed it contained $1.7 million of ETH (Ethereum) which had been obtained by selling some of the stolen NFTs. OpenSea Co-Founder and CEO, Devin Finzer pointed out that the company doesn’t believe the hack is connected to the OpenSea website.
Thanks to our episode sponsor, Tines
Conti takes over TrickBot and plans to replace it with BazarBackdoor
TrickBot is a popular Windows banking Trojan that has been around since 2016. Its authors have continuously upgraded it by implementing new features, including powerful password-stealing capabilities. Although originally partnered with Ryuk ransomware Ryuk was replaced by Conti Ransomware gang. The increasing popularity of TrickBot made it easier to detect it with antimalware solutions, and for this reason the gang has begun employing the BazarBackdoor for initial access to networks.
Dangerous privilege escalation bugs found in Linux package manager Snap
Researchers found an easy-to-exploit vulnerability in Snap, a universal application packaging and distribution system developed for Ubuntu but available on multiple Linux distributions. The flaw allows a low-privileged user to execute malicious code as root, the highest administrative account on Linux. The vulnerability, tracked as CVE-2021-44731, is part of a series of flaws that researchers from security firm Qualys found in various Linux components while investigating the security of Snap. This latest one, along with a separate issue tracked as CVE-2021-44730, are in snap-confine, the tool responsible for setting up Snap application sandboxes.
Popular e-cigarette store was compromised to steal credit cards
BleepingComputer has confirmed Element Vape, a prominent online seller of e-cigarettes and vaping kits was serving a credit card skimmer on its live site, likely after getting hacked. With its presence across the U.S. and Canada, Element Vape sells e-cigarettes, vaping devices, e-liquids, and CBD products in both retail outlets and on their online store. This Magecart attack saw customer data exfiltrated and sent to a Telegram address. The attack was resolved the same day of disclosure via this report, but customers are advised to remain alert of any suspicious credit card transactions.
Jammer used to stop kids going online, wipes out a town’s internet by mistake
A parent in Toulouse, France, frustrated by his kids’ addiction to social media used a multi-band jammer to stop the kids from going online through their phones after midnight. This action also locked out the internet access to a neighboring town. Local authorities were able to triangulate the source of the jamming, based on its extremely regular schedule – on at midnight, off at 3:00 a.m. Unfortunately for the Dad in question, using a jammer is not legal in France, and he now faces a maximum fine of €30,000 and even a jail term of up to six months.
(ZDNet)