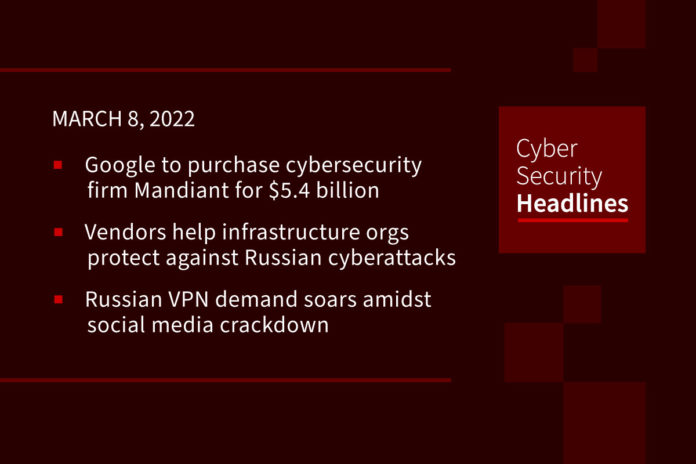
Google to purchase cybersecurity firm Mandiant for $5.4 billion
Google has entered into an agreement to acquire Mandiant in a whopping, all-cash deal worth $5.4 billion. Mandiant will join Google Cloud to help deliver an end-to-end security operations suite and advisory services to help customers address critical security challenges. Mandiant’s CEO, Kevin Mandia, said that the acquisition by Google “underscores Google Cloud’s commitment to advancing its security offerings to better protect and advise customers across their on-premise and cloud environments.”
(ZDNet)
Security vendors help infrastructure orgs protect against Russian cyberattacks
CrowdStrike, Cloudflare, and Ping Identity have entered into a collaborative effort, dubbed the Critical Infrastructure Project, under which the firms will provide at least four months of their services for free to organizations in water, power utilities, and healthcare sectors to help protect against cyberattacks. Services include technologies such as Cloudflare’s cloud gateway, DNS filtering, and web application firewall; CrowdStrike’s Falcon endpoint protection and Falcon X threat monitoring; and Ping Identity’s PingOne and DaVinci identity orchestration service. A spokeswoman for CrowdStrike said, “The immediate impetus for the program is the heightened risk of cyberattacks tied to the Russian invasion of Ukraine.”
Russian VPN demand soars amidst social media crackdown
After passing a law criminalizing so-called “false information” about Russia’s invasion of Ukraine, Russian authorities have cracked down on social media, blocking Facebook and imposing restrictions on Twitter. Other social media companies, including TikTok, have blocked Russian use of their services. In response, many Russians are utilizing VPN services to access blocked social media networks and news sites. According to privacy monitoring service, Top10VPN, demand for VPNs in Russia was 668% higher on March 3 than it was the week prior to the invasion.
(NPR)
Access:7 vulnerabilities impact medical and IoT devices
A set of seven vulnerabilities tracked as Access:7, three of which are rated critical, have been found in Parametric Technology Corporation’s (PTC) Axeda agent which provides telemetry data and remote services for network-connected IoT devices. Axeda agents are used in over 2,000 unique devices, many of which are utilized within healthcare, making them prime targets for supply-chain attacks. The impact of the Access:7 bugs range from denial-of-service (DoS) to remote code execution and information disclosure. Researchers at Forescout have provided a list of vulnerable devices and alerted affected customers to apply available vendor patches.
There are many misconceptions about security automation, so Torq is debunking a security automation myth each day this week.

Debunked. While enterprises with thousands of endpoints and sprawling teams certainly need automation, businesses of all sizes face challenges related to other forms of scale when it comes to security. For instance, there are about 1 billion known types of malware in existence, and they imperil businesses of all sizes equally. To learn more about the realities of automation, head to torq.io.
DDoS attacks use new record-breaking amplification vector
A new DDoS method, called “reflection,” is being used in attacks that provide a record-breaking amplification ratio of almost 4.3 billion to 1. Reflection attacks start with a small packet which gets reflected inside a closed network, amplifying its size to near maximum capacity, before channeling the traffic to the target. Threat actors were observed using the new DDoS technique on victims across numerous industries in mid-February by abusing a vulnerable Mitel driver found in devices using the TP-240 VoIP interface. Customers using vulnerable devices should follow Mitel’s remediation instructions, enforcing firewall rules to block malicious initiator packets or disable the abused command.
Linux distros patch ‘Dirty Pipe’ kernel bug
A Linux local privilege escalation flaw, dubbed Dirty Pipe, has been disclosed along with proof-of-concept exploit code. The flaw, tagged as CVE-2022-0847, can be exploited by a normal logged-in user or a rogue program to gain root-level privileges. The issue was introduced in kernel version 5.8 and fixed in versions 5.10.102, 5.15.25, and 5.16.11. The issue stems from a blunder in the kernel’s pipe handling code, which allows a user program to overwrite the contents of the page cache and, ultimately, the file system. Linux kernel patches have been released while fixes are still pending for Android on vulnerable Google Pixel 6 and Samsung Galaxy S22 devices.
2022 password report bad news for Cincinnati Reds fans (and pretty much everyone else)
The 2022 Weak Password Report from Specops takes a look at both the human side and the tech side of why passwords are the weakest link in an organization’s network. The report analyzed 800 million breached passwords and highlighted that 93% of the passwords used in brute force attacks include 8 or more characters and 68% of passwords used in attacks include at least two character types. More than half of organizations do not use password management tools while nearly half of organizations do not have user verification in place for calls to the IT service desk. Interestingly, the Cincinnati Reds top the list of most popular baseball teams found in compromised password lists. The report recommends that organizations block weak and compromised passwords, enforce password length requirements, verify user identities at the service desk and audit their environment for password-related vulnerabilities.
(Specops)
Microsoft and Google issue March 2022 patches
Microsoft’s March 2022 Patch Tuesday fixes 71 security bugs, only two of which are rated critical. However, the patches do address 3 zero-day vulns including a Remote Desktop Client Remote Code Execution Vulnerability, Windows Fax and Scan Service Elevation of Privilege Vulnerability, and .NET and Visual Studio Remote Code Execution Vulnerability. The good news is that none of these vulnerabilities are being actively exploited.
In parallel with Microsoft’s fixes, this week Google has released patches for 39 vulnerabilities in Android. The most serious vulnerability is CVE-2021-39708, a remotely exploitable elevation of privilege issue identified in the System component.