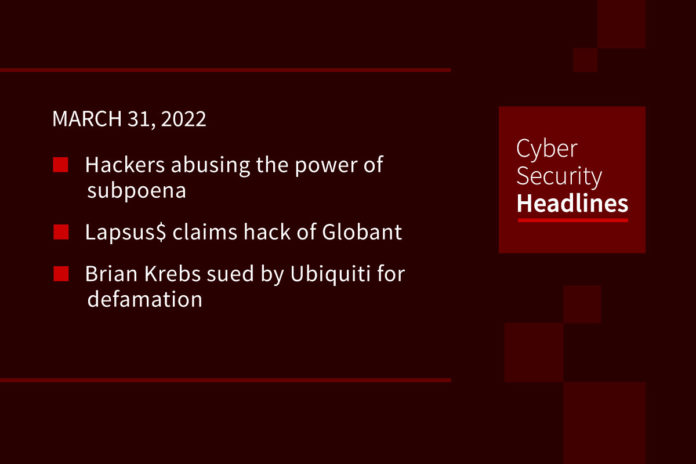
Hackers abusing the power of subpoena
In the US, when a government or law enforcement agency wants to obtain information on a social media account or IP address tied to a cell phone, they submit a court-ordered warrant or subpoena, with most major platforms having pipelines to process the request. In cases of imminent harm, an authority can submit an Emergency Data Request, which does not require court-approved documents. Brian Krebs reports that there is no way for platforms to determine if these requests are legitimate, with hackers using illicit access to police email systems to request information on people. These tactics were offered for sale by the hacking group Recursion Team on forums back in 2021. Some of Recursion’s members are believed to be active in Lapsus$. Bloomberg’s source say Apple, Meta, and possibly Snap provided customer data to hackers posing as law enforcement.
(Krebs on Security, Bloomberg)
Lapsus$ claims hack of Globant
The extortion group posted on its Telegram channel, claiming to have stolen 70GB of data from the international software firm Globant. Screenshots of the folders show names of several global businesses, including Facebook, Apple, DHL, C-Span, the bank BNP Paribas. The data linked to Apple appears to be developmental material for Globant’s BeHealthy app, a health behavior tracker for employees. Despite the alleged arrest of Lapsus$’ leader by London police last week, the group said it was “back from vacation” on Telegram.
Brian Krebs sued by Ubiquiti for defamation
The company filed the lawsuit in the Eastern District of Virginia, alleging that Krebs falsely accused the company of “covering up” a cyberattack. Ubiquiti claims it promptly notified customers of the attack, followed by a public disclosure with an SEC filing. Krebs reported that Ubiquiti downplayed the severity of a security backdoor that allowed for access to source code and credentials for Ubiquiti devices. This lawsuit involves the source of Krebs’ story, a Ubiquiti employee named Nickolas Sharp, who allegedly contacted Krebs framing the story as the action of an external actor. The lawsuit alleges Krebs later knew Sharp was the source of the hack, but maintained a story about an external actor to drive traffic to his site. Krebs did not reply to the allegations yet on advice of counsel.
(SC Magazine, Corey Quinn)
UK regulator extends deadline for crypto registration
The UK’s Financial Conduct Authority will extend its April 1st deadline for its approval of crypto operations in the country for firms that can prove they need more time. Twelve firms remain on a temporary register of firms that applied for permission to operate while applications were considered. The FCA already approved 33 firms for permanent registration. Initially hundreds of firms applied for temporary permission to operate while applications were ongoing, but many spun down operations in the UK due to the country’s strict anti-money laundering rules.
Thanks to our episode sponsor, Varonis
Scammers abuse Facebook’s Media Partner Portal
Motherboard shared that some scammers are using this portal in an attempt to verify accounts on Facebook and Instagram, as well as claim inactive username. This portal is meant to provide a streamlined way for media outlets to resolve issues with Facebook accounts, including helping with doxxing and harassment, or challenge content removals. Motherboard reports Upwork and other freelance hiring sites contain multiple listings looking for people with access to the Media Partner Portal to verify accounts. People looking to verify pages use them to verify profiles for Play to Earn cryptocurrency games, as well as pages related to entertainment, sports, and startups.
(Vice)
Verizon explains spam text messages from yourself
Verizon confirmed that it’s investigating an increasing number of spam messages appearing to be sent from a user’s own phone number. Verizon characterized these as coming from “bad actors” with no ties to the company and said its engaged with US law enforcement to stop the source of the activity, as well as working to block them on their network. While some users reported these spam texts send users to Russian state media networks, Verizon said “we have no indication that this fraudulent activity is originating in Russia.” While Verizon seems to be the only US carrier network receiving an increased volume of these self-spam texts, it does not believe its network is compromised.
Axie Infinity says it will reimburse losses
We reported yesterday on a hacker stealing over $600 million in Ethereum from the Ronin network bridge of the game Axie Infinity. Now the game’s developer Sky Mavis said it’s “fully committed to reimbursing our players as soon as possible,” although clarified that it’s “still working on a solution” to make that happen. The company does not suspect insider involvement in the attack. Of the 173,600 Ether stolen, 56,000 belonged to the Axie Infinity treasury, the rest belonging to players and speculators. Possible solutions involve selling Axie-related tokens in bulk at a discount, or selling company equity to raise cash.
Google reports on Ukraine war-related hacking
According to the Google Threat Analysis Group, government-backed actors across China, North Korea, Iran, and Russia have used themes around the war in Ukraine in malicious phishing and malware attacks. This includes browser-in-the-browser attacks from the Belarusian-back group Ghostwriter, the Chinese-backed Curious George group targeting military organizations in Ukraine, Russia, and Mongolia, and a Russia-backed group targeting a NATO Centre of Excellence and Eastern European militaries. Google also continued to observe multiple ransomware brokers continuing to operate with business as usual practices.