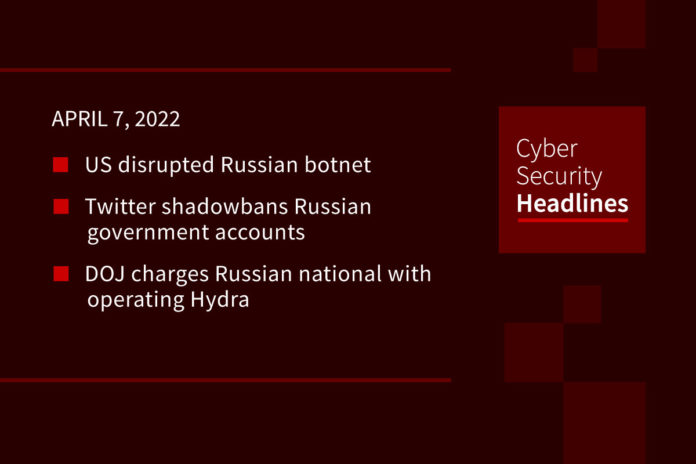
US disrupted Russian botnet
Attorney General Merrick Garland announced that government officials disrupted a botnet built by the Sandworm hacking group linked to Russia’s GRU intelligence agency. Sandworm had previously been blamed for attacks against Ukraine’s electric grid in 2015 and the NotPetya attacks in 2017. This botnet used “Cyclops Blink” code to target WatchGuard Technologies’ Firebox firewall hardware and was also able to infect some Asus network hardware. Garland said the government believed it was taken down before it could be weaponized to perform any malicious activity.
Twitter shadowbans Russian government accounts
The social network announced that it will “drastically” reduce the chances of people seeing posts from accounts belonging to the Russian government as part of further measures to limit Russia’s ability to leverage the platform. This means these accounts won’t be suggested to follow or appear in Search or Explore pages. In an effort not to spread content that risks violating the Geneva Conventions, Twitter will also “require the removal of Tweets posted by government or state-affiliated media accounts” that contain media showing prisoners of war from Russia’s invasion of Ukraine. Twitter’s head of site integrity, Yeol Roth, said there are exceptions to this policy for media that is “compelling public interest or newsworthy POW content.” Twitter will also remove any content showing PoWs with “abusive intent” across all accounts.
DOJ charges Russian national with operating Hydra
We reported yesterday that German police seized the server of the Hydra dark web market. Now the US Justice Department filed charges against a 30-year old Russian national named Dmitry Olegovich Pavlov, alleging a range of crimes connected to operating Hydra. Pavlov ran a company called Promservice Limited, which offered hosting and administrative services for Hydra. The DOJ claims he collected commissions on sales of illicit goods on Hydra worth millions of dollars. The US Treasury also issued sanctions against Hydra and the Estonia-based crypto exchange Garantex this week, in the hopes that it will prevent individuals associated with Hydra from cashing out remaining funds.
Axie Infinity hackers move some funds
We’ve been covering the story of the hack of Axie Infinity’s Ronin Network bridge, which saw the game lose roughly $600 million worth of crypto assets. Since this occurred on the Ethereum blockchain, the address where the funds went is known. Stealing the funds is one thing, but laundering them is an entirely separate challenge. Funds are starting to trickle out to other exchanges, with analysts observing about $20 million worth of assets moved to exchanges in the Bahamas and Seychelles last week, and this week roughly $12 million of assets flowed into a cryptocurrency mixer to obscure sources.
(WSJ)
Thanks to our episode sponsor, Code42

Google bans data harvesting apps
Security researchers at AppCensus notified Google about an SDK found in Android apps from the company Measurement Systems, which has corporate and web registration ties to a Virginia defense contractor that does intelligence-intercept work for national security agencies. The code was found inside several Muslim prayer apps that had been downloaded over 10 million times, as well as QR code readers, and other popular consumer apps. The researchers found the code allowed Measurement Systems to surreptitiously collect data from users, describing it as the most privacy-invasive SDK they had seen in a mobile app. The researchers also sent a copy of their findings to the FTC. Google says it removed apps containing Measurement Systems software from the Google Play Store on March 25th, although some were reinstated after they removed the SDK. The SDK stopped collecting data shortly after the researchers went public, but could be reactivated on devices with an already installed app.
(WSJ)
Threat actors spoof WhatsApp voice message notifications
Security researchers at Armorblox outlined this new phishing campaign, targeting Office 365 and Google Workspace accounts. This sends spoofed WhatsApp voice message emails sent from a legitimate domain belonging to the Center for Road Saftey, an entity in Moscow. The campaign is estimated to have hit 27,660 inboxes. Phishing emails include a link to play back the “new private voicemail” in WhatsApp. Once clicked, users are sent to the legitimate Center for Road Safety domain, but it appears the attackers are exploiting a deprecated or old version of this parent domain. Once there, the page asks the user to verify they are not a robot, with an “allow” pop-up leading to the installation of a malicious payload.
AMD bug overclocks your CPU
AMD confirmed that a bug in its GPU drivers changes the settings of Ryzen CPUs in BIOS without permission. Some users reported seeing auto-overclocked CPUs. AMD typically warns that overclocking CPUs voids its warranty. The company said it will share more information on the bug soon, but didn’t provide any mitigation advice or estimated fix date. The bug seems tied to a Radeon Adrenalin driver from March 17. The driver suite added an auto-overclock feature in September 2021, but users are supported to opt-in.
Windows 11 adds new security features
As part of a number of updates to the OS, Microsoft added Microsoft Defender SmartScreen, designed to detect if you’re entering Microsoft account info into malicious apps or phishing sites in Edge. It’s unclear if this only applies to apps from the Microsoft Store or any installed on a machine. Another new feature is Smart App Control which uses AI and code signing to ensure only trusted apps run on a PC. The company also now allows customers to sign into Azure Active Directory and Microsoft accounts with passwordless sign-ons. No word on when these features roll out.
(Engadget)