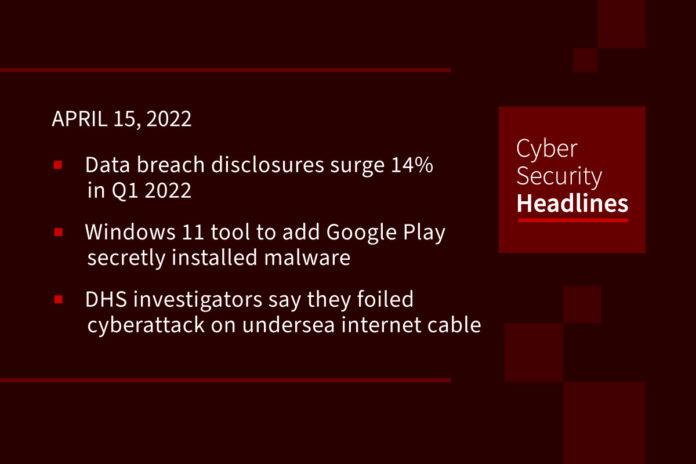
Data breach disclosures surge 14% in Q1 2022
The number of publicly reported data breaches in the US increased by double digits year-on-year in the first three months of 2022, according to the Identity Theft Resource Center (ITRC). The non-profit claimed that the increase represents the third successive year in which Q1 figures have exceeded those recorded 12 months previously. The vast majority (92%) of breaches recorded by the ITRC were traced back to cyber-attacks, with phishing and ransomware the top two causes overall. However, there remains a gap in reporting, as 154 data breach notices, or around 40%, did not include the root cause. This made “unknown” the largest attack vector in Q1 2022.
Windows 11 tool to add Google Play secretly installed malware
In October last year with the release of Windows 11, Microsoft announced that it would allow users to run native Android apps directly from within Windows. But when the Android for Windows 11 preview was released in February, many were disappointed they could not use it with Google Play and were stuck with apps from the Amazon App Store. Around that time, someone released a new tool called Windows Toolbox on GitHub with a host of features, including the ability to debloat Windows 11, activate Microsoft Office and Windows, and install Google Play Store for the Android subsystem. However, unbeknownst to everyone until this week, the Windows Toolbox was actually a Trojan that executed a series of obfuscated, malicious PowerShell scripts to install a trojan clicker and possibly other malware on devices.
DHS investigators say they foiled cyberattack on undersea internet cable in Hawaii
Federal agents in Honolulu last week “disrupted” an apparent cyberattack on an unnamed telecommunication company’s servers associated with an underwater cable responsible for internet, cable service and cell connections in Hawaii and the region, the agency said in a statement Tuesday. Although few details were given about the motive or target, international law enforcement partners in several countries were able to make an arrest.” There are hundreds of undersea cables that form part of the internet, John Sherman, author of an Atlantic Council report on undersea infrastructure writes, many cable operators use remote management systems for cable networks, many of which have poor security.
(Cyberscoop and The Atlantic Council)
Global advertising giant Omnicom suffers ‘suspicious’ IT incident
Omnicom, one of the world’s largest marketing and advertising agencies, took some of its IT systems offline over the past week due to suspicious activity. Several employees affected by the outage said that they were unable to access their virtual private network service, and some couldn’t access email. Omnicom is a U.S.-based global company that generates over $14 billion a year, making it the second-largest global advertising firm by some estimates. It represent 5,000 clients in more than 70 countries, including McDonald’s, Apple, Unilever and Johnson & Johnson. Omnicom Media Group was hit by a cyberattack last year that disrupted parts of its IT networks.
Thanks to our episode sponsor, Code42

Code42 believes that the Three Ts should define any IRM program: transparency, training, and technology. Shift your security culture from “watchdog” to “guide dog” and everyone wins. Learn more at Code42.com/showme.
Meet ZingoStealer: new, free malware from the Haskers Gang
A new type of information stealer has been added to the Haskers Gang malware portfolio. On Thursday, researchers from Cisco Talos said that the malware, dubbed ZingoStealer, is being offered for free to Haskers Gang Telegram group members. The Haskers Gang, which claims thousands of casual members, communicates via Telegram and Discord to share ‘community’ updates, tools, and its latest activities. The Telegram group has just under four thousand subscribers who share tips on cracks, crypters, bypassing security measures and hacking software. Telegram is also abused to manage the malicious executables and exfiltrated data packages. ZingoStealer can harvest account credentials, Chrome and Firefox browser data, and Discord tokens, as well as cryptocurrency wallet credentials held by browser extensions from services including BitApp, Coinbase, Binance, and Brave.
(ZDNet)
Elon Musk offers to buy Twitter for $43 billion
The offer, filed with the U.S. Securities and Exchange Commission shows that Musk is willing to pay $54.20 per share to buy 100% of the company. It would be an all-cash offer that values the social network at $43.4 billion. He said in an email to Bret Taylor, Twitter’s chairman of the board (and Salesforce co-chief executive), “I invested in Twitter as I believe in its potential to be the platform for free speech around the globe, and I believe free speech is a societal imperative for a functioning democracy. However, since making my investment I now realize the company will neither thrive nor serve this societal imperative in its current form. Twitter needs to be transformed as a private company.”
Microsoft details how China-linked crew’s malware hides scheduled Windows tasks
The China-linked Hafnium gang is using a strain of malware to maintain a persistent presence in compromised Windows systems by creating hidden tasks that maintain backdoor access even after reboots. Researchers within Microsoft’s Detection and Response Team (DART) and Threat Intelligence Center (MTIC) spotted the software, dubbed Tarrask, creating undesirable scheduled tasks via Windows Task Scheduler, which is typically used by IT administrators to automate such chores as updating programs, tidying up file systems, and starting certain applications. The malware is part of a larger multi-stage attack against organizations that exploits an authentication bypass in the snappily named ManageEngine ADSelfService Plus, Zoho’s password-management and single-sign-on offering for Active Directory environments.
Man who paid $2.9m for NFT of Jack Dorsey’s first tweet discovers resale is NSF
Crypto entrepreneur Sina Estavi made headlines in March 2021 when he paid $2.9m for an NFT of Twitter boss Jack Dorsey’s first tweet. But his efforts to resell it have run aground, with a top bid of just $6,800 as of Thursday. The initial purchase was at the time among the most expensive sales of a non-fungible token, or NFT. Estavi is no longer sure if he will sell the NFT. “It’s important to me who wants to buy it,” he says, continuing,” I will not sell this NFT to anyone because I do not think everyone deserves this NFT.”