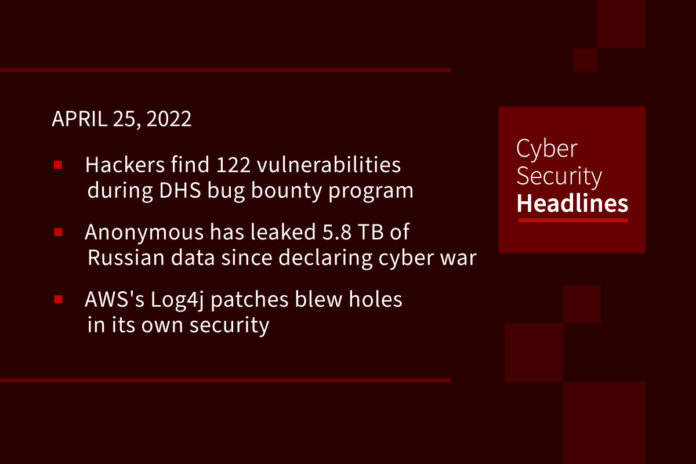
Hackers find 122 vulnerabilities, 27 deemed critical, during first round of DHS bug bounty program
These vulnerabilities were found by more than 450 security researchers who were working through the Department of Homeland Security’s “Hack the DHS” bug bounty program, which started in December 2021. The researchers, who were vetted by the agency before participating, were eligible to receive between $500 and $5,000 for verified vulnerabilities, depending on the severity. The DHS has not disclosed the vulnerabilities that were found, nor did it share any information about fixes for the bugs. Under original plans for the DHS program, the agency would verify the flaws within 48 hours of being notified, and fix them within 15 days — or, for more complex bugs, develop a plan to address them.
Anonymous has leaked 5.8 TB of Russian data since declaring cyber war
The group has released hundreds of thousands of emails from high profile Russian organizations in the energy sector, property management and financial management, some of which have numerous high profile western companies as clients. The Twitter account AnonymousTV states there is more to come.
AWS’s Log4j patches blew holes in its own security
Amazon Web Services has updated its Log4j security patches after it was discovered the original fixes made customer deployments vulnerable to container escape and privilege escalation. The vulnerabilities introduced by Amazon’s Log4j hotpatch – CVE-2021-3100, CVE-2021-3101, CVE-2022-0070, CVE-2022-0071 – are all high-severity bugs rated 8.8 out of 10 on the CVSS. “We recommend that customers who run Java applications in containers, and use either the hotpatch or Hotdog, update to the latest versions of the software immediately,” the cloud giant said in a security bulletin on Tuesday.
Atlassian addresses a critical Jira authentication bypass flaw
The vulnerability in its Jira Seraph software is tracked as CVE-2022-0540 (CVSS score 9.9), and can be exploited by an unauthenticated attacker to bypass authentication. A threat actor could trigger the vulnerability by sending a specially crafted HTTP request to vulnerable software. The issue affects a range of Atlassian Jira Server and Data Center versions before 8.13.18, and between 8.14 and 8.20.6 and versions between 8.21 and 8.22.0. Full details are available in the security advisory published on the Atlassian site.
Thanks to our episode sponsor, Feroot

Cyberattack causes chaos in Costa Rica government systems
Nearly a week into a ransomware attack that has crippled Costa Rican government computer systems, the country has refused to pay a ransom as it struggles to implement workarounds. The Russian-speaking Conti gang has claimed responsibility for the attack, but the Costa Rican government has not confirmed its origin. The attack has affected the country’s Finance and Labor Ministries, among others, shutting down services such as paying public employees and delivering government pension payments, and forcing the government to grant extensions for tax payments. Conti has not published a specific ransom amount, but Costa Rica President Carlos Alvarado said, “The Costa Rican state will not pay anything to these cybercriminals.”
US govt grants academics $12M to develop cyberattack defense tools for energy sector
The funding is coming from the US Department of Energy (DOE) and is earmarked to go to six university teams to develop defense and mitigation tools to protect US energy delivery systems from cyberattacks. The goal is to focus on detecting, blocking, and mitigating attempts to compromise critical controls within the US power grid. The universities involved are: Florida International University, Iowa State, New York University, Texas A&M Engineering Experiment Station, University of Illinois at Chicago, and the Virginia Polytechnic Institute and State University.
Emotet reestablishes itself at the top of the malware world
Just about a month ago we reported on a Cisco blog announcing the return of Emotet. Check Point researchers now list it as the most widely deployed malware, menacing or infecting as much as 10 percent of organizations around the globe in March, apparently double that of February. Now Kaspersky Labs says a rapidly accelerating and complex spam email campaign is enticing marks with fraudulent messages designed to trick one into unpacking and installing Emotet or Qbot malware that can steal information, collect data on a compromised corporate network, and move laterally through the network and install ransomware or other trojans on networked devices.
Beanstalk DeFi project robbed of $182 million in flash loan attack
On April 19, Beanstalk, a credit-based stablecoin protocol project based on Ethereum, said the platform was subject to a flash loan attack two days previously. This happened after an unknown threat actor secured the project voting rights necessary to transfer reserve funds away from the project’s liquidity pools. Flash loan functions in DeFi projects allow users to borrow large amounts of virtual funds for a short period of time. In Beanstalk Farm’s case, voting powers were based on the amount of tokens held. Researchers at Omniscia say that after the attacker secured a flash loan — and, therefore, extensive voting rights normally used to accept or decline changes in the protocol’s code — an emergency governance mechanism was abused to ‘vote’ for a malicious proposal and allow themselves to send funds to a wallet they controlled.(ZDNet)