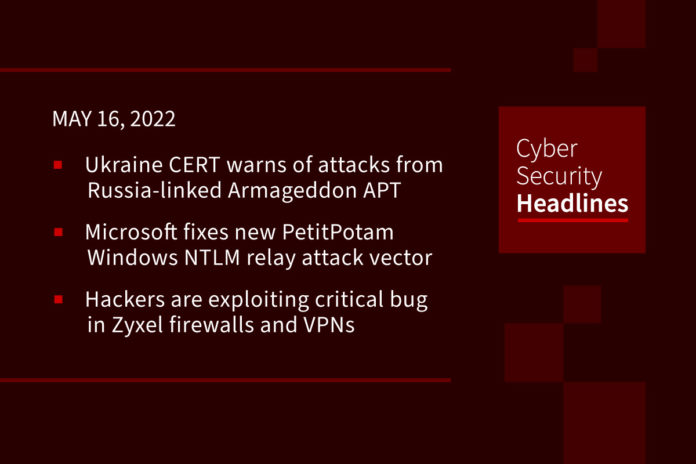
Ukraine CERT-UA warns of new attacks launched by Russia-linked Armageddon APT
Ukraine’s Computer Emergency Response Team (CERT-UA) reported a phishing campaign using messages with subject “On revenge in Kherson!” and containing the “Plan Kherson.htm” attachment. The HTM-file will decode and create an archive named “Herson.rar.” In the last stage of the attack chain, the GammaLoad.PS1_v2 malware is downloaded and executed on the victim’s computer. The government experts attributes the attack to the Russia-linked Armageddon APT (UAC-0010) (aka Gamaredon, Primitive Bear, Armageddon, Winterflounder, or Iron Tilden) which was involved in a long string of attacks against the local state organizations.
Microsoft fixes new PetitPotam Windows NTLM relay attack vector
A recent security update for a Windows NTLM Relay Attack has been confirmed to be a previously unfixed vector for the PetitPotam attack. During the May 2022 Patch Tuesday, Microsoft released a security update for an actively exploited NTLM Relay Attack labeled as a ‘Windows LSA Spoofing Vulnerability’ and tracked as CVE-2022-26925. An NTLM Relay Attack allows threat actors to force devices, even domain controllers, to authenticate against malicious servers they control. Once a device authenticates, the malicious server can impersonate the device and gain all of its privileges.
Hackers are exploiting critical bug in Zyxel firewalls and VPNs
Hackers have started to exploit a recently patched critical vulnerability, tracked as CVE-2022-30525, that affects Zyxel firewall and VPN devices for businesses. Successful exploitation allows a remote attacker to inject arbitrary commands remotely without authentication, which can enable setting up a reverse shell. The severity of the security issue and the damage it could lead to is serious enough for the NSA Cybersecurity Director Rob Joyce to warn users about exploitation and encourage them to update the device firmware version if it is vulnerable.
Sysrv-K, a new variant of the Sysrv botnet, includes new exploits
Microsoft’s Security Intelligence team has reported that a new variant of the Sysrv botnet, tracked as Sysrv-K, now includes exploits for vulnerabilities in the Spring Framework and WordPress. Threat actors use the botnet in a cryptomining campaign targeting Windows and Linux servers. The botnet also supports scanning capabilities for WordPress configuration files and their backups, the feature allows operators to access sensitive data, including database credentials.
Thanks to our episode sponsor, Torq

Incorrect. Proactive management of security incidents is just as important, like automatically scanning IaC configurations to detect vulnerabilities, automating collaboration between devs, IT ops and SecOps to prevent risks before they’re threats. To learn more about the realities of automation, head to torq.io.
D-Wave deploys first US-based Advantage quantum system
Quantum computing outfit D-Wave Systems has announced availability of an Advantage quantum computer accessible via the cloud but physically located in the US. D-Wave reported that the newly deployed system is the first of its Advantage line of quantum computers available via its Leap quantum cloud service. The new system is based at the University of Southern California, as part of the USC-Lockheed Martin Quantum Computing Center hosted at USC’s Information Sciences Institute, a factor that may encourage US organizations interested in evaluating quantum computing that are likely to want the assurance of accessing facilities based in the same country.
Intel memory bug poses risk for hundreds of products
According to an advisory issued by the company on Tuesday, the bug is firmware-based and rated as “high” risk. The vulnerability resides inside some of the Intel Optane SSD and Intel Optane Data Center (DC) products, the impact of which allows privilege escalation, denial of service (DoS), or information disclosure. Dell and HP were among the first to release patches and fixes for the bug.
Last week’s ransomware roundup
While ransomware attacks have slowed during Russia’s invasion of Ukraine and the subsequent sanctions, the malware threat continues to affect organizations worldwide. Costa Rica declared a national emergency after suffering a massive IT systems outage caused by a Conti Ransomware attack in April. The US offers $15 million reward for info on Conti ransomware gang. Secureworks has analyzed new REvil ransomware samples, confirming previous reports that the ransomware gang has returned. Lincoln College in Lincoln, Illinois, is to close after 157 years due in part to a ransomware attack, and in part to Covid-19. A week before Oregon’s primary election, the secretary of state’s office is moving to protect the integrity of its online system where campaign finance records are published after a web hosting provider was hit by a ransomware attack. Ransomware names and dropped files that appeared last week include .kekpop, TitanCrypt,.japan, BlueSky and TxLocker, and a new Xoris variant appending the .WanaCray2023+ and dropping a ransom note named HOW TO DECRYPT FILES.txt.