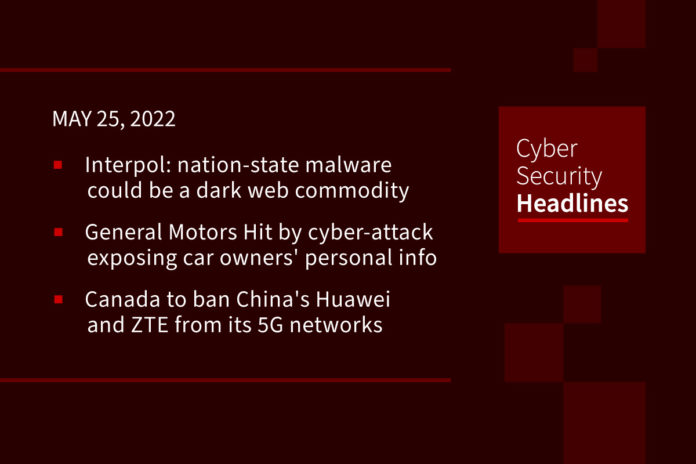
Interpol warns nation-state malware could become a commodity on dark web soon
Interpol Secretary General Jurgen Stock declared that the ongoing conflict between Russia and Ukraine, the malware developed by both nation-state actors and non-state actors represents a serious risk for critical infrastructure and organizations worldwide. Threat actors could perform reverse engineering of military-made malicious code and use their own versions in attacks in the wild. The scenario also opens the doors to false flag operations, nation-state actors could have access to cyber weapons used in the conflict and use them in attacks in the wild making the attribution impossible.
General Motors Hit by cyber-attack exposing car owners’ personal info
The company announced that it was hit by a credential stuffing attack last month that exposed customer information and allowed hackers to redeem rewards points for gift cards. Malicious login activity was detected between April 11-29 2022. The company also stated their belief that unauthorized parties gained access to customer login credentials that were previously compromised on other non-GM sites and then reused those credentials on the customer’s GM account. The data stolen included names address, photos, OnStar membership data, car mileage and service history and WiFi hotspot settings including passwords.
Canada to ban China’s Huawei and ZTE from its 5G networks
The restrictions were announced by the country’s industry minister on Thursday, who said it would improve Canada’s mobile internet services and “protect the safety and security of Canadians”. In making this move, Canada now joins the UK, US, Australia and New Zealand, which, together make up an intelligence-sharing arrangement named “Five Eyes,” a group that evolved during the Cold War as a mechanism for monitoring the Soviet Union and sharing classified information. But Huawei Canada said it was “disappointed” by the decision, which it said was “political”.
(BBC)
Ransomware attacks increasing at “alarming” rate
Ransomware breaches have increased by 13% – more than the last five years combined – according to the Verizon Business 2022 Data Breach Investigations Report (2022 DBIR). In addition to the increase in ransomware breaches, it also found that 82% of cyber breaches involved the human element, including social attacks, errors and misuse. It also found that 62% of incidents in the system intrusion pattern involved threat actors compromising partners. The report also illustrated how one supply chain incident can cause a wide range of consequences: “Compromising the right partner is a force multiplier for threat actors. Unlike a financially motivated actor, nation-state threat actors may skip the breach altogether, and opt to simply keep the access to leverage at a later time.”
Thanks to today’s episode sponsor, Optiv

– An introduction to Zero Trust
– An overview of Optiv’s Zero Trust principles
– How to visualize your Zero Trust journey and place it in the proper context
Catch Jerry’s Zero Trust crash course or learn more by going to www.optiv.com/zerotrust.
Trend Micro fixes bug Chinese hackers exploited for espionage
Trend Micro says it patched a DLL hijacking flaw in Trend Micro Security used by the Chinese threat group ‘Moshen Dragon to side-load malicious DLLs and deploy malware. As Sentinel Labs revealed in an early-May report, the attackers exploited the fact that security products run with high privileges on Windows to plant and load their own maliciously crafted DLL into memory, allowing them to elevate privileges and execute code. After analyzing the report and its product line, the company discovered that only the Trend Micro Security consumer-focused product was affected, with no other commercial or business products impacted.
Screencastify Chrome extension flaws allow webcam hijacks
The popular Screencastify Chrome extension has fixed a vulnerability that allowed malicious sites to hijack users’ webcams and steal recorded videos. However, security flaws still exist that could be exploited by unscrupulous insiders. The vendor acknowledged the cross-site scripting (XSS) vulnerability and promptly fixed it after security researcher Wladimir Palant reported it responsibly on February 14, 2022. Screencastify is a screen recorder, video editor, and media sharing browser extension with over 10,000,000 installs on the Chrome web store.
CISA adds 41 vulnerabilities to list of bugs used in cyberattacks
The added vulnerabilities come from a wide range of years, with the oldest disclosed in 2016 and the most recent being a Cisco IOS XR vulnerability fixed last Friday which allows attackers to write arbitrary files in the containerized filesystem, retrieve Redis database information, or write to the Redis in-memory database. Other flaws of interest are two Android Linux Kernel flaws tracked as CVE-2021-1048 and CVE-2021-0920 as well as flaws concerning Cisco, Microsoft, Apple, Google, Mozilla, Windows, Facebook, Adobe, and Webkit GTK.
There are still malware-laden PDFs in emails exploiting bugs from 2017
HP’s cybersecurity peope have uncovered an old-school email campaign that ticks all the boxes: messages with a PDF attached that embeds a Word document that upon opening infects the victim’s Windows PC with malware by exploiting a four-year-old code-execution vulnerability in Microsoft Office. Lacing a PDF with a malicious Word document has not been used much in the past decade, according to the HP Wolf Security researchers. Criminals have preferred Office file formats, such as Word and Excel, to deliver malicious code rather than PDFs, as users are more used to getting and opening .docx and .xlsx files. Malware hidden in PDF formats is apparently not as useful for social engineering attacks.