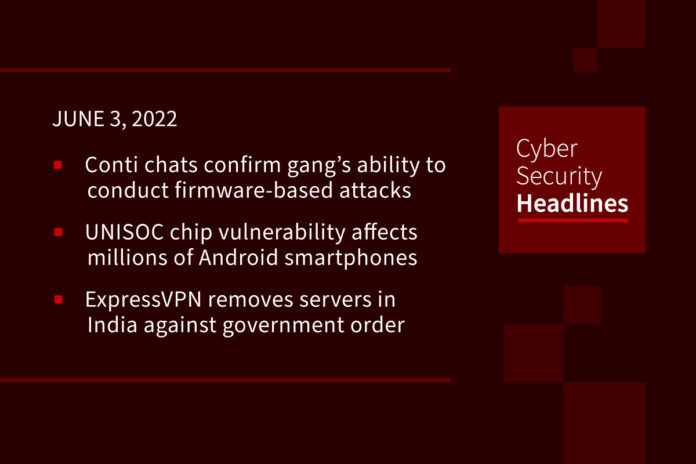
Leaked Conti chats confirm gang’s ability to conduct firmware-based attacks
The analysis of Conti group’s chats, which were leaked earlier this year, revealed that the ransomware gang has been working on firmware attack techniques which would give threat actors significant powers, since they are hard to detect, are highly destructive, and attackers can use them to achieve long-term strategic goals. Researchers from security firm Eclypsium discovered that the Conti ransomware gang was working on attacks targeting both UEFI/BIOS and the Intel Management Engine (ME) or Intel Converged Security Management Engine (CSME).
Critical UNISOC chip vulnerability affects millions of Android smartphones
A critical security flaw has been uncovered in UNISOC’s smartphone chipset that could be potentially weaponized to disrupt a smartphone’s radio communications through a malformed packet. “Left unpatched, a hacker or a military unit can leverage such a vulnerability to neutralize communications in a specific location,” Israeli cybersecurity company Check Point said in a report shared with The Hacker News. “The vulnerability is in the modem firmware, not in the Android OS itself.” UNISOC, a semiconductor company based in Shanghai, is the world’s fourth-largest mobile processor manufacturer after Mediatek, Qualcomm, and Apple, accounting for 10% of all SoC shipments in Q3 2021, according to Counterpoint Research.
ExpressVPN removes servers in India after refusing to comply with government order
Virtual Private Network (VPN) provider ExpressVPN on Thursday announced that it’s removing Indian-based VPN servers in response to a new cybersecurity directive issued by the Indian Computer Emergency Response Team (CERT-In). In a statement, the company said its users will still be able to connect to VPN servers that will give them Indian IP addresses and allow them to access the internet as if they were located in India. “Virtual India” servers will instead be physically located in Singapore and the U.K.” The development comes in response to controversial data retention requirements that are set to come into effect on June 27, 2022 in India, that mandate VPN service providers to store subscribers’ real names, contact details, and IP addresses assigned to them for at least five years.
Clipminer malware actors steal $1.7 million using clipboard hijacking
The malware known as Clipminer has earned cyberattackers $1.7 million in cryptocurrency mining and theft via clipboard hijacking so far – and it shows no signs of abating. Symantec’s Threat Hunter Team determined that Clipminer is likely spread through Trojanized downloads of cracked or pirated software. The malware can redirect cryptocurrency transactions made on the infected computer by replacing cryptocurrency wallet addresses copied to a clipboard with new addresses under the control of the hacker. Clipminer uses addresses matching the prefix of the targeted original address to disguise the manipulation.
Thanks to today’s episode sponsor, Feroot

Learn more at www.feroot.com.
Microsoft blocks Polonium hackers from using OneDrive in attacks
Microsoft said it has blocked a Lebanon-based hacking group it calls Polonium from using the OneDrive cloud storage platform for data exfiltration and command and control while targeting and compromising Israeli organizations. The company also suspended more than 20 malicious OneDrive applications used in Polonium’s attacks, notifying the targeted organizations and quarantining the threat actors’ tools via security intelligence updates. Though the attacks have mainly targeted Israel’s manufacturing, IT, and defense industry sectors since February 2022, Polonium operators have also likely coordinated their hacking attempts with multiple Iran-linked threat actors, according to Microsoft’s analysis.
Chinese LuoYu hackers deploy cyber-espionage malware via app updates
A Chinese-speaking hacking group known as LuoYu is infecting victims WinDealer information stealer malware deployed by switching legitimate app updates with malicious payloads in man-on-the-side attacks. To do that, the threat actors actively monitor their targets’ network traffic for app update requests linked to popular Asian apps such as QQ, WeChat, and WangWang and replace them with WinDealer installers.Once deployed, WinDealer helps the attackers search for and siphon large amounts of data from compromised Windows systems, install backdoors to maintain persistence, manipulate files, scan for other devices on the network, and run arbitrary commands.
U.S. cybersecurity officials issue notice on Karakurt extortion group
A trio of U.S. government agencies on Wednesday issued an advisory with technical details related to the Karakurt data extortion gang, warning that the group has created significant challenges for defense and mitigation.” Karakurt — also known as the Karakurt Team or Karakurt Lair — doesn’t destroy or encrypt victim files. Instead, the group steals data and threatens to publish it, with known ransom demands ranging between $25,000 and $13 million in bitcoin, according to the notice published jointly by the FBI, the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA), the Treasury Department and the Treasury Department-run Financial Crimes Enforcement Network. Karakurt is part of the Conti ransomware group, multiple independent cybersecurity researchers reported in April.
Your Y2Q Update: Researchers claim quantum device performs 9,000-year calculation in microseconds
Researchers in Canada have conducted a quantum computing experiment that they claim completes a calculation in just a fraction of a second that would take a conventional computer 9,000 years. Jonathan Lavoie, an experimental physicist at quantum computing company Xanadu, and his colleagues reported the results from a device designed to sample an unknown probability distribution of light passing through a network of optical fibers. Their findings were published in the magazine Nature, whose editors pointed out that the experiment was important because programmable photonic processors were closer to the form that a quantum commercial device might take than other previous proof-of-principle quantum computing experiments.(The Register)