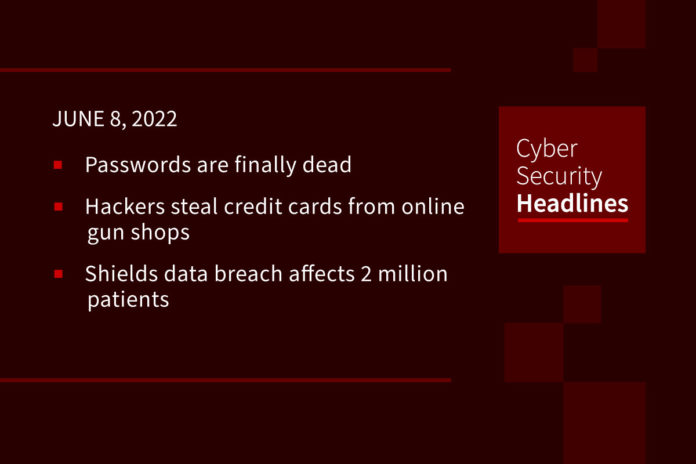
Passwords are finally dead – no, its for real this time
At its Worldwide Developer Conference on Monday, Apple announced its plan to launch passwordless login across Macs, iPhones, iPads, and Apple TVs later this year. Within iOS 16 and macOS Ventura, users will be able to log in to websites and apps using digital keys which are created using Touch ID or Face ID. These “passkeys” will sync across user devices using iCloud’s Keychain, rather than being stored on servers. In May, Apple, along with Microsoft and Google, declared their support for new FIDO standards upon which Apple’s passkeys were developed.
(Wired)
Hackers steal credit cards from online gun shops
Two American gun shops have disclosed data breaches resulting from card skimmer infections on their e-commerce sites. Rainier Arms, who pedals high-end tactical rifles, received customer reports of unauthorized payment card activity back in December 2021, but only just isolated the malicious card-stealing Java code on its site in mid-April. The skimmer was actively harvesting payments since June 2021 and Rainier has issued breach notices to more than 46,000 impacted customers. Additionally, firearms dealer Numrich discovered in March that they had suffered a similar breach affecting payment information entered on their site between January 23, 2022, and April 5, 2022. With increasing sensitivity around gun ownership and high dollar transactions, firearm dealer sites are expected to remain lucrative targets for cyber criminals.
Shields data breach affects 2 million patients
Massachusetts-based medical services provider, Shields Health Care Group (Shields), has suffered a data breach that exposed the data of approximately 2 million patients. Shield became aware of the cyberattack on March 28, 2022, and with the help of cybersecurity experts, determined that hackers had access to their systems from March 7 to March 21, 2022, potentially exposing patient data including, name, SSN, dates of birth, home address, and medical records. Shields says that, so far, it has seen no evidence that any stolen information has been misused or further disseminated. A complete list of the 56 impacted medical facilities is published on the Shields website.
Cybersecurity advisory warns of potent cyber extortion group
Several US federal agencies, including CISA, have issued an alert warning organizations of a data extortion group named Karakurt, which experts believe has ties to the infamous Conti gang. Karakurt has employed a variety of tactics, techniques and procedures (TTPs), to steal data from companies and subsequently demand ransoms as high as $13 million Bitcoin. Karakurt has been known to contact their victims’ employees, business partners, and clients with harassing phone calls and emails containing screenshots of the stolen data to pressure the victims to cooperate. Between September and November 2021, more than 40 organizations fell victim to Karakurt. CISA has published mitigation strategies at www.cisa.gov.
Thanks to today’s episode sponsor, PlexTrac

Check out PlexTrac.com/CISOSeries to learn why PlexTrac is the premier pentest reporting and management platform.
Black Basta ransomware now targets VMs
Uptycs Threat Research analysts have identified Black Basta as the latest ransomware gang to add support for VMware ESXi machines running on enterprise Linux servers. Black Basta’s ransomware uses the ChaCha20 algorithm to encrypt VMs on compromised ESXi servers and leverages multiple processors to speed up the encryption process. The ransomware creates ransom notes, which conveniently include a chat panel link and unique ID that victims can use to communicate with the attackers. Since first being observed in the wild back in April, Black Basta has received at least one ransom demand exceeding $2 million in exchange for use of its decryptor tool.
Apple Safety Check combats domestic abuse
Apple announced a new feature called Safety Check, designed to curb domestic abuse, which will debut in iOS 16. Apple says the new feature gives users the ability to review permissions granted to apps and other individuals and provides an emergency reset function that instantly cuts off iCloud access from other devices (including GPS tracking), resets privacy permissions, and limits FaceTime and messaging services to one device. The optimal time for victims of abuse to leverage emergency reset is when they are no longer in physical proximity of their abuser. If you or someone you know is experiencing domestic violence, you are encouraged to reach out to law enforcement or the National Domestic Violence Hotline at 1-800-799-7233.
(ZDNet)
Schneier predicts AI hacking will favor defense
In his keynote at RSA Conference 2022, Bruce Schneier contended that it’s only a matter of time before AI becomes a more dangerous hacking threat than its human counterparts due to AI’s speed, scale and scope. Schneier highlighted how AI thinks outside the box compared with humans because AI doesn’t consider values, norms, implications or context. Schneier noted that cybersecurity professionals need to begin preparing to defend against the AI threats now, suggesting financial systems as a starting point due to their being, “designed to be algorithmically hackable.” Finally, Schneier opined, “AI hacking can be deployed by the offense and the defense, in the end, it favors the defense.”
You should probably patch that
On Monday, Google published its Android Security Bulletin for June 2022 detailing patches for over 40 security vulnerabilities, including a critical remote code execution (RCE) bug in the system component affecting Android versions 10, 11, 12, and 12L. Several other critical vulnerabilities were also addressed by the bulletin.
Additionally, 0patch micropatching service has developed free and unofficial patches for all Windows platforms back to Windows 7 and Server 2008, which are vulnerable to yet another zero-day vulnerability, dubbed “DogWalk”, in the Microsoft Support Diagnostic Tool (MSDT). Though the bug was first discovered in January 2020, Microsoft denied it being a security issue claiming that Outook users were not at risk. Security researchers claim that a threat actor could still use the traversal bug to deliver malicious files via alternate email clients or in drive-by download attacks.