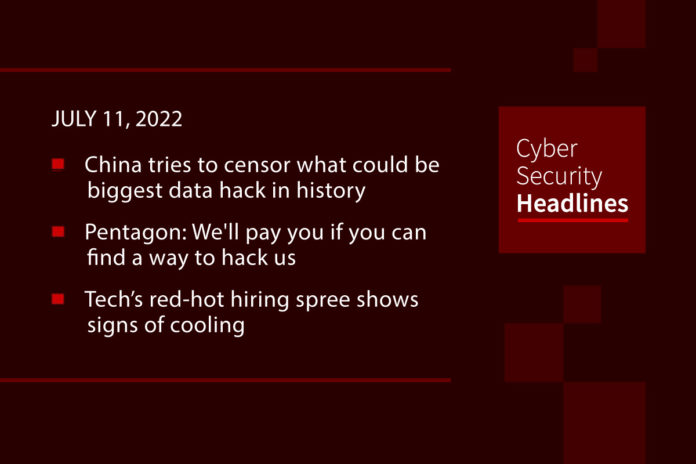
China tries to censor what could be biggest data hack in history
Chinese censors are working overtime to clamp down on news that the data they’ve siphoned from their citizens over the years is apparently out there and is for sale. This is a follow-up to the story we covered last week, in which a hacker only identified as “ChinaDan” announced they had acquired data on 1 billion Chinese citizens. The Financial Times has written that Weibo, essentially China’s version of Twitter, and WeChat were already censoring any mention of hashtags containing “data leak” or “database breach.” Censors blocked existing posts and even reportedly asked at least one poster with a big follower-base to come in for questioning.
(Gizmodo)
Pentagon: We’ll pay you if you can find a way to hack us
The US Department of Defense has created a broad but short bug bounty program for reports of vulnerabilities in public-facing systems and applications. The Hack US program kicked off on Independence Day and is scheduled to run through today, July 11, with reward totals reflected by the severity of the flaws. The DoD has allocated up to $110,000 for the exploit hunt. Vulnerability spots can bring in $500 or more for high-severity flaws, and critical holes are worth at least $1,000 with as much as $5,000 set aside for particular awards, such as $3,000 for the best finding for *.army.mil. The initiative is being run with bug bounty platform maker HackerOne, which teamed up with the DoD to operate a 12-month pilot program that ended in April. Hack US adds monetary rewards to the calculation.
Tech’s red-hot hiring spree shows signs of cooling
The tech industry’s ultrarapid hiring during the pandemic is showing signs of cooling off, and a number of top executives are preparing for it to get worse. With fear of a recession looming, executives from high-profile tech companies have announced plans to slow hiring or cut jobs, and are in some cases warning employees to brace themselves for tougher times. Although the overall labor market remains tight, with strong demand for workers in some sectors and positions, warnings from some tech leaders heightened fears of a tough stretch ahead for a sector whose influence and power touch virtually every aspect of society. Twitter, Tesla, Snap, Netflix, Amazon, Meta, Coinbase and RobinHood are some of the high profile names who have made cuts or announcements of cuts recently.
Maastricht University wound up earning money from its ransom payment
The Dutch university was hit with Clop ransomware in December 2019, which had been deployed through phishing emails. The university decided to pay the 30 bitcoin ransom which was equal to roughly €200,000 at the time, in order to avoid delaying exams and losing all its research, educational, and staff data. However, since the Netherlands Public Prosecution Service later traced and seized a wallet containing the ransom, still held as bitcoin, their value had grown to approximately €500,000.” The University Executive Board said it wants to use the money to create a fund that would allow the university to help students in need.
Thanks to today’s episode sponsor, Edgescan

Rogers CEO apologizes for massive service outage, blames maintenance update
A massive network outage at Rogers Communications that shut down mobile and internet services across much of Canada on Friday was not a cyberattack, but was instead what Rogers president and CEO Tony Staffieri described as “a network system failure following a maintenance update in our core network, which caused some of our routers to malfunction.” With many businesses, government agencies and parts of the 911 emergency service rendered powerless during the 15-hour outage, experts are calling this a “learning opportunity for threat actors such as Russian state-sponsored hackers, who can now see how vulnerable Canadian industry, financial institutions and health-care systems are to an attack on a telecom provider.”
(CBC)
Medical debt collection firm says ransomware attack exposed info on 650+ healthcare orgs
In a statement issued late last week, Professional Finance Company said that during the February attack the Quantum ransomware group used the Bumblebee malware loader to gain access to databases that held names, addresses, accounts receivable balances, information regarding payments made to accounts, dates of birth, Social Security numbers, and health insurance data and medical treatment information. Its role as a debt collection firm means healthcare organizations provide the company with information on patients or customers who have not paid, making them an ideal target for hackers. PFC said it notified the 657 companies in May.
Last week in ransomware
Earlier last week, the AstraLocker ransomware group decided to shut down and release its decryptors after receiving attention from researchers. These decryptors allowed Emsisoft to release their own decryptor. Two new enterprise-targeting ransomware operations appeared last week, one called RedAlert, the other 0mega, both of which perform double-extortion attacks. CheckMate is a new ransomware targeting QNAP devices but not stealing any data. And in addition to the just-mentioned Quantum attack on PFC, the US government is warning about the Maui ransomware that is targeting healthcare.
Pentester says he broke into datacenter via hidden route running behind toilets
Noted security consultant Andrew Tierney, who works as a consultant for security services outfit Pen Test Partners revealed on Twitter how he managed to gain unauthorized access to a datacenter when he discovered that the toilet facilities for an unnamed client’s general office space and the secure area where the IT infrastructure is housed, had a shared access space for servicing both sets of facilities. Flushed with his success, Tierney noted that he had just managed to defeat the datacenter’s security protection which involved mantrap entry gates where personnel had to “surrender all digital devices” upon entry. Even worse, the toilet layout was visible for all to see on public planning documents, meaning that anyone could have figured out how to bypass security. He single handedly gave new meaning to the term, IP access.