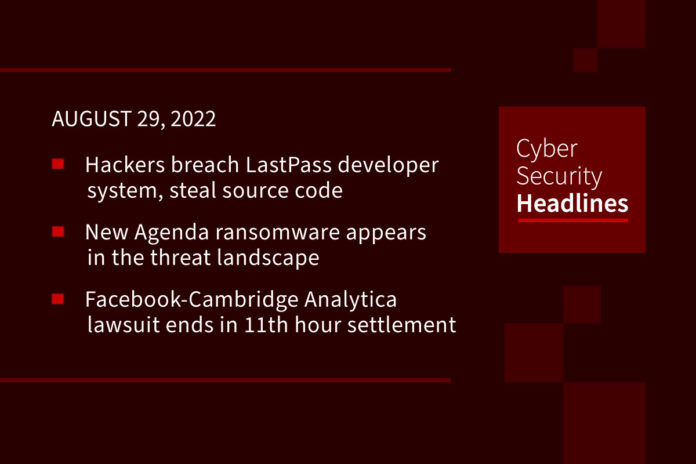
Hackers breach LastPass developer system to steal source code
Password management service LastPass has confirmed a security incident that resulted in the theft of certain source code and technical information. The security breach is said to have occurred two weeks ago, targeting its development environment. The company has stated that no customer data or encrypted passwords were accessed, although it provided no further details regarding the hack and what source code was stolen. “An unauthorized party gained access to portions of the LastPass development environment through a single compromised developer account and took portions of source code and some proprietary LastPass technical information,” LastPass CEO Karim Toubba said.
New Agenda ransomware appears in the threat landscape
Trend Micro researchers recently discovered a new piece of targeted ransomware tracked as Agenda, that was written in the Go programming language. The ransomware was employed in a targeted attack against one of its own customers. The investigation into the incident revealed that threat actor used a public-facing Citrix server as a point of entry, likely using a valid account to access this server and perform lateral movements inside the victim’s network. The new ransomware family hit enterprises in Asia and Africa. The name Agenda comes from dark web posts by a user named “Qilin,” who is likely linked to the ransomware distributors, and through ransom notes.
Facebook-Cambridge Analytica data breach lawsuit ends in 11th hour settlement
Facebook has agreed to settle a lawsuit seeking damages for allowing Cambridge Analytica access to the private data of tens of millions of users, four years after the Observer exposed the scandal that mired the tech giant in repeated controversy. A court filing reveals that Meta, Facebook’s parent company, has in principle settled for an undisclosed sum from a long-running lawsuit that claimed Facebook illegally shared user data with the UK analysis firm. This dramatic move has led some observers to speculate that it was done to prevent CEO Mark Zuckerberg and Meta’s outgoing chief operating officer, Sheryl Sandberg, from being made to testify during hours of questioning by plaintiffs’ lawyers next month.
Prepare now for quantum computers, says CISA
CISA published a paper last week, calling for leaders to start preparing for the migration to stronger secret guarding systems, exploring risk mitigation methods, and participating in developing new standards, in the face of the advance of quantum computing. Experts in the field widely accept that the currently experimental quantum computers will achieve superiority over conventional systems by the end of the decade and will quickly render them obsolete with subsequent capability leaps. “When quantum computers reach higher levels of computing power and speed, they will be capable of breaking public key cryptography, threatening the security of business transactions, secure communications, digital signatures, and customer information,” the agency said.
Thanks to today’s episode sponsor, Code42

Code42 Incydr is an Insider Risk Management SaaS that provides a comprehensive understanding of your data exposure and shows which activities require security intervention. Learn more at Code42.com/showme.
Google employees frustrated after back-to-office Covid outbreaks
Google employees are receiving regular notifications from management of Covid-19 infections, causing some to question the company’s return-to-office mandates. The employees, who spoke with CNBC on the condition of anonymity, said since they have been asked to return to offices, infections notifications pop up in their email inboxes regularly. The company began requiring most employees to return to physical offices at least three days a week in April. The outbreak in Los Angeles is currently the largest of any employer in the city, according to the city’s public health dashboard. Deadline.com first reported that the tech giant’s trendy Silicon Beach campus in Venice, Calif., recorded 145 infections, while 135 cases were recorded at the company’s large Playa Vista campus.
(CNBC)
There is no such money anywhere as there is in ransomware
The April ransomware attack on the Washington, D.C. Metropolitan Police Department, which the Babuk gang claimed as one of theirs, was, according to Brian Krebs, masterminded by one Mikhail Matveev, who also goes by the handle, Wazawaka. In a recent interview with The Record, he suggests that although ransomware as a business will likely die away in a few years, there is currently “no such money anywhere as there is in ransomware.” He claims it is even more lucrative than the dark web drug trade. The full interview is available at The Record.
California AG looks ahead to other data privacy violations after Sephora fine
California’s Attorney General Rob Bonta is already looking ahead to the next potential violations of the California Consumer Privacy Act (CCPA) after issuing the state’s first fine of $1.2 million to Paris-based makeup giant Sephora last week. While announcing the fine — which was part of a settlement with Sephora to resolve allegations the company violated the CCPA — Bonta said he also sent notices to “a number of businesses” due to alleged non-compliance when it comes to processing consumer opt-out requests. The violations center around the processing of consumer requests made through global privacy controls that allow people to opt out of all online sales in one click. Many businesses attempt to get around this by making users click on opt-out links each time they visit a website.
Last week in ransomware
Last week’s ransomware stories centered mostly around LockBit, who saw their Tor data leak sites taken down by a DDoS attack shortly after claiming responsibility for a ransomware attack on the cybersecurity giant. Researchers released reports this week on a Genshin Impact anti-cheat driver being abused to terminate antivirus processes during ransomware attacks, and a new extortion group called Donut Leaks appeared. Cyberscoop reported an overall rise in ransomware activity, with a good deal emanating from North Korea. Finally, last week’s ransomware attacks include Greek natural gas operator DESFA, a French hospital, and Bombardier Recreational Products.