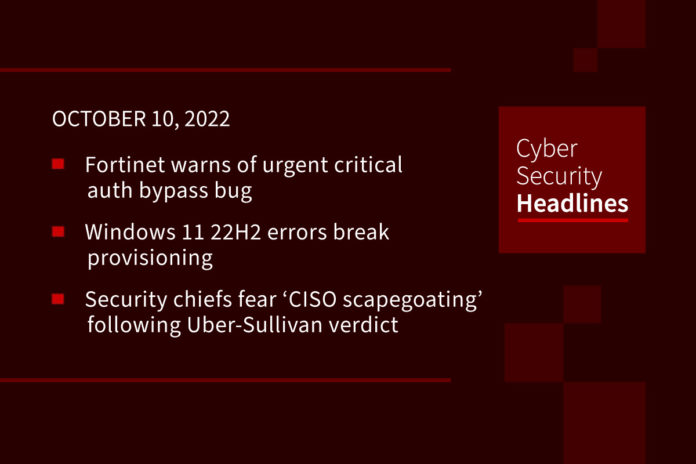
Fortinet warns admins to patch critical auth bypass bug immediately
Fortinet has warned administrators to update FortiGate firewalls and FortiProxy web proxies to the latest versions which address a critical severity vulnerability. The security flaw (tracked as CVE-2022-40684) is an authentication bypass on the administrative interface that could allow remote threat actors to log into unpatched devices. “This is a critical vulnerability and should be dealt with the utmost urgency,” the company adds. According to a Shodan search, more than 100,000 FortiGate firewalls are reachable from the Internet, although it’s unknown if their management interfaces are also exposed.
Windows 11 22H2 errors break provisioning
Microsoft says the Windows 11 2022 Update is breaking provisioning, leaving Windows 11 enterprise endpoints partially configured and failing to finish installing. According to Microsoft, this known issue most likely affects provisioning packages (.PPKG files used to configure new endpoints on enterprise or school networks without imaging) during the initial setup phase. “Windows might only be partially configured, and the Out Of Box Experience might not finish or might restart unexpectedly.” Microsoft added that this issue would not impact IT administrators provisioning Windows devices on their network. The list of unaffected devices also includes Windows systems used in home or small office networks.
Security chiefs fear ‘CISO scapegoating’ following Uber-Sullivan verdict
CISOs are split on whether Wednesday’s conviction of Uber’s former security chief Joe Sullivan will have more wide-ranging consequences for people in their position. According to The Record, some fear the case will prompt more CISO whistleblowers in the future, while others feel that security chiefs should be prepared to be held responsible for incidents that they are involved in. A federal jury convicted Sullivan of two charges related to his attempted cover-up of a 2016 security incident at Uber, where hackers stole the personal details of 57 million customers and the personal information of 600,000 Uber drivers.
Lloyd’s of London investigates alleged cyber attack
After detecting unusual network activity this week, Lloyd’s has reset its IT infrastructure and shut down external connections. The incident comes after the entire insurance industry was alerted of potential cyber attacks as a result of the ongoing conflict between Russia and Ukraine. Companies in the insurance market have condemned Russia’s invasion of Ukraine and supported sanctions against Moscow, including imposing bans on insuring ships carrying Russian oil. In August, Lloyd’s of London told to its insurance syndicates that it will no cover losses caused by cyber-attacks conducted by nation-state actors and resulting from malicious activities related the ongoing conflict.
Thanks to this week’s episode sponsor, Noname Security

Facebook detects 400 Android and iOS apps stealing users log-in credentials
Meta Platforms on Friday disclosed that it had identified over 400 malicious apps on Android and iOS that it said targeted online users with the goal of stealing their Facebook login information. “These apps were listed on the Google Play Store and Apple’s App Store and disguised as photo editors, games, VPN services, business apps, and other utilities to trick people into downloading them.”Besides concealing its malicious nature as a set of seemingly harmless apps, the operators of the scheme also published fake reviews that were designed to offset the negative reviews left by users who may have previously downloaded the apps.
Papa John’s sued for ‘wiretap’ spying on website mouse clicks, keystrokes
The pizza chain is being sued for allegedly breaking the US Wiretap Act by snooping on the way a customer browses the Papa John’s website. The suit alleges the use of session replay software which records everything a user does on the site, beyond what fetching pages and placing an order would submit. Session replay tools have been a privacy concern due to their indiscriminate capturing of data, sometimes poor security, and failures to get user consent to track and store user data which is then open to analysis.
World’s largest crypto exchange hacked with possible losses of $500m
Binance, the world’s largest cryptocurrency exchange, may have lost half a billion dollars after a hack of its network. The company temporarily suspended transactions and transfer of funds after detecting an exploit between two blockchains, a method of digital theft that has been used recently in at least one other major hack. According to Binance CEO, Changpeng Zhao, speaking via a tweet, “The issue is contained now. Your funds are safe. We apologize for the inconvenience and will provide further updates accordingly.”
Last week in ransomware
Last week saw the sentencing of a Netwalker ransomware affiliate, Sebastien Vachon-Desjardins, to 20-years in prison plus forfeiture of $21.5 million for an attack on a Tampa business and other companies worldwide. We also had reports released last week that linked the Cheerscrypt ransomware to a Chinese hacking group and showed how the BlackByte ransomware operation uses ‘Bring Your Own Vulnerable Driver’ (BYOVD) attacks to terminate security software. Motherboard also released a report based on FOIA requests, showing how US schools have responded to ransomware attacks on their networks. Finally, the Vice Society began leaking data belonging to students, parents, and employees of the Los Angeles Unified school district, and Ferrari denies RansomEXX attacked them.