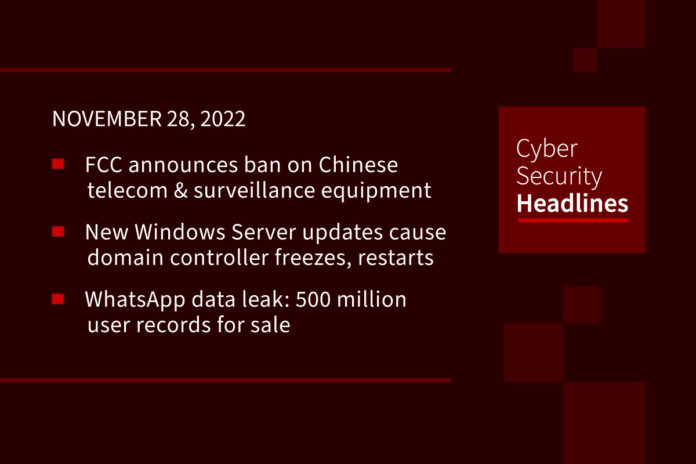
FCC announces ban on Chinese telecom and surveillance equipment
The total ban applies to Chinese companies Huawei, ZTE, Hytera, Hikvision, and Dahua and is due to what is being called an “unacceptable” national security threat. They are included as a directive in the Secure Equipment Act of 2021, which was signed by President Biden in November. Hytera, Hikvision, and Dahua must provide details about the safeguards they have implemented on the sale of their devices for government use and the surveillance of critical infrastructure facilities. The FCC explained that the above companies are subject to the exploitation, influence and control of the Chinese government, and the national security risks associated with such exploitation, influence, and control.
New Windows Server updates cause domain controller freezes, restarts
Microsoft is investigating LSASS memory leaks, caused by Windows Server updates released during the November Patch Tuesday, that might lead to freezes and restarts on some domain controllers. LSASS (short for Local Security Authority Subsystem Service) is responsible for enforcing security policies on Windows systems, and it handles access token creation, password changes, and user logins. If this service crashes, logged-in users immediately lose access to Windows accounts on the machine, and they’re shown a system restart error followed by a system reboot. Microsoft is working on a resolution and says it will provide an update with an upcoming release.
WhatsApp data leak: 500 million user records for sale
On November 16, an actor posted an ad on a well-known hacking community forum, claiming they were selling a 2022 database of 487 million WhatsApp user mobile numbers. The dataset allegedly contains WhatsApp user data from 84 countries. Threat actor claims there are over 32 million US user records included. The dataset also allegedly has tens of millions of numbers from customers in Egypt, Italy, Saudi Arabia, France, Turkey, Russia and the UK. The seller did not specify how they obtained the database, suggesting they “used their strategy” to collect the data. WhatsApp parent company, Meta has not commented on this story, but industry experts suggest that this collection of numbers could have been achieved from scraping, and not hacking.
Ransomware gang targets Belgian municipality, hits police instead
The Ragnar Locker ransomware gang has published stolen data from what they thought was the municipality of Zwijndrecht, but turned out to be stolen from Zwijndrecht police, a local police unit in Antwerp, Belgium. The leaked data reportedly exposed thousands of car license plates, fines, crime report files, personnel details, investigation reports, and more. This type of data can potentially expose people who reported crimes or abuse and could compromise ongoing law enforcement operations and investigations. Belgian media outlets call this data leak one of the biggest of this kind that has impacted a public service in the country, exposing all data kept by Zwijndrecht police from 2006 until September 2022.
Thanks to this week’s episode sponsor, Automox

Meta confirms U.S. military involvement in sprawling phony social media operation
People associated with the U.S. military were behind dozens of phony Facebook accounts, more than a dozen pages, a pair of groups and 26 Instagram accounts that pushed pro-U.S. messaging largely to audiences in the Middle East and Central Asia, while attempting to hide their real identities, Facebook’s parent company Meta said in a report published Tuesday. After researchers first exposed the decade-long operation in August, the Pentagon ordered “a sweeping audit of how it conducts clandestine information warfare,” The Washington Post reported in September. Citing unnamed U.S. officials, the paper reported that U.S. Central Command was among the entities under scrutiny as part of their potential role in the operation. A spokesperson for U.S. Central Command declined to comment Tuesday.
Dell, HP, and Lenovo devices found using outdated OpenSSL versions
An analysis of firmware images across devices from these manufacturers has revealed the presence of outdated versions of the OpenSSL cryptographic library, underscoring a supply chain risk. EFI Development Kit, functions as an interface between the operating system and the firmware embedded in the device’s hardware. Per firmware security company Binarly, the firmware image associated with Lenovo Thinkpad enterprise devices was found to use three different versions of OpenSSLsoem dating back to August 2014. “This clearly indicates the supply chain problem with third-party dependencies when it looks like these dependencies never received an update, even for critical security issues,” the company said.
Businesses hope to cut cyber turnover by encouraging volunteer work
Companies are encouraging their cyber employees to volunteer at nonprofits, a nudge that managers say can help businesses retain in-demand technical experts despite high turnover in security roles. The CyberPeace Institute, a Geneva-based group that helps nonprofits, humanitarian and healthcare organizations address cybersecurity, set up a program last year to enlist professionals from the corporate world to explain things like email phishing to nonprofits that might lack the budget to hire their own experts. Cyber volunteerism can also bolster the team as a whole, said Clair Rosso, chief executive of (ISC)2. Stepping away from day-to-day work and looking at a different organization as an outsider can give employees a fresh perspective on their own job, she said. “There’s a case that allowing employees to go and volunteer in other organizations is actually going to strengthen the security posture of your own organization,” she said.
Automakers are locking the aftermarket out of ECUs
As vehicles start to integrate more complex systems such as Advanced Driver Assist Systems and over-the-air updates, automakers are growing weary of what potential bad actors could gain access to by way of hacking. Whether those hacks come in an attempt to retrieve personal customer data, or to take control of certain aspects of these integrated vehicles, automakers want to leave no part of that equation unchecked. In order to prevent this from becoming a potential safety or legal issue, numerous car manufacturing companies have moved to heavily encrypt their vehicle’s software. This sort of total lockout presents an interesting challenge for tuners who rely on access to things like engine and transmission control modules to create their products.