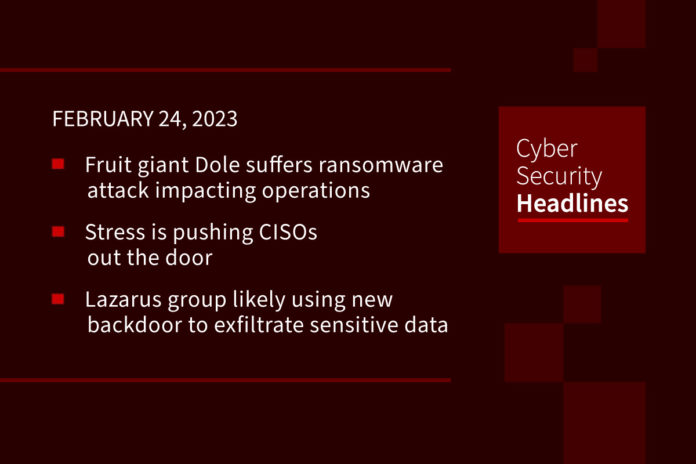
Fruit giant Dole suffers ransomware attack impacting operations
One of the world’s largest producers and distributors of fruit and vegetables, the Dole Food Company, has confirmed a ransomware attack, but says the scope of its impact is still unknown. It does say, however that “”the impact is limited.” However, a document posted to Facebook by a Texan grocery store suggests that the attack has forced Dole to shut down its production plants at least for a day in North America, and that it has temporarily halted its shipments to grocery stores.
Stress pushing CISOs out the door
A new report from Gartner states that nearly half of CISOs will change jobs by 2025 due to stress caused by the risk of being breached while trying to retain staff. The firm found that “the stressors of the cybersecurity world make the job of a cybersecurity professional unsustainable.” The knowledge of two possible outcomes in their jobs, get hacked or don’t, has lead to a profound psychological impact, “directly affecting decision quality and performance of cybersecurity leaders and their teams,” the report states. Notably, “a leader recovering from the stress of a data breach could last less than five years on the job,” which the report identifies as the the average tenure of a cybersecurity leader.
Lazarus group likely using new backdoor to exfiltrate sensitive data
This new backdoor is associated with a malware downloader named Wslink. ESET has named the payload as WinorDLL64 , a fully-featured implant that can exfiltrate, overwrite, and delete files, execute PowerShell commands; and obtain comprehensive information about the underlying machine. Wslink was first documented by ESET in October 2021, describing it as a “simple yet remarkable malware loader” that’s capable of executing received modules in memory.
Phishing sites and apps use ChatGPT as lure
Several new Windows and Android phishing campaigns are using ChatGPT to trick users into downloading malware and handing over their credit card details. Cybersecurity firm Cyble says that several phishing sites are being spread by a fake social media pages spoofed in the name of ChatGPT developer OpenAI. “The page seems to be trying to build credibility by including a mix of content, such as videos and other unrelated posts,” it said. A closer look revealed that some posts on the page contain links that lead users to typosquatted phishing pages that impersonate ChatGPT. These phishing pages trick users into downloading malicious files onto their machines.
Thanks to this week’s episode sponsor, Barricade Cyber Solutions

NSA shares guidance on how to secure your home network
As reported by Bleeping Computer, “the guide, published by the Defense Department’s intelligence agency on Wednesday, includes a long list of recommendations to help remote workers secure their home networks and defend their devices from attacks, urging teleworkers to ensure their devices and software are up to date, to back up their data regularly, and to disconnect equipment they’re not using if it doesn’t require an active Internet connection at all times.” The agency states, “at a minimum, you should schedule weekly reboots of your routing device, smartphones, and computers. Regular reboots help to remove implants and ensure security.” It also recommends “using a non-privileged user account on your computer, enabling automatic updates whenever possible, and covering webcams and disabling microphones when not using them to block eavesdropping attempts via compromised devices or malware.”
New Stealc malware-as-a-service targets web browsers, crypto wallets, email clients
According to a report published by threat intelligence company Sekoia.io, Stealc is a “ready-to-use stealer” that targets sensitive data from at least 23 web browsers, including Google Chrome, Vivaldi, and Mozilla Firefox, as ell as popular desktop cryptocurrency wallets, like Binance and Coinomi. Stealc also goes after web browser-based wallets, email clients and messenger software. Sekoia says, “We expect that the Stealc infostealer will become widespread in the near term, as multiple threat actors add the malware to their arsenal while it is poorly monitored.”
Python developers warned of trojanized PyPI packages mimicking popular libraries
“Imposter packages” mimicking popular libraries available on the Python Package Index (PyPI) repository are the subject of a warning from cybersecurity researchers this week. Fortyone malicious PyPI packages have been found posing as typosquatted variants of legitimate modules such as HTTP, AIOHTTP, requests, urllib, and urllib3. Fortinet, which also highlighted similar fake HTTP packages on PyPI earlier this week, noted “their ability to launch a trojan downloader that, in turn, contains a DLL file (Rdudkye.dll) packing a variety of functions.”
Hidden vulnerabilities in popular open source containers
Software security company Rezilion yesterday released a white paper uncovering the presence of hundreds of docker container images containing vulnerabilities that are not detected by most standard vulnerability scanners and SCA tools. According to the company, their research reveals that common practices in the build process of nearly every container image unknowingly introduces blindspots that leave the door open open for attackers to try and exploit them because defenders are simply unaware of their existence. The paper, entitled, Hiding in Plain Sight: Hidden Vulnerabilities in Popular Open Source Containers
(Rezilion)