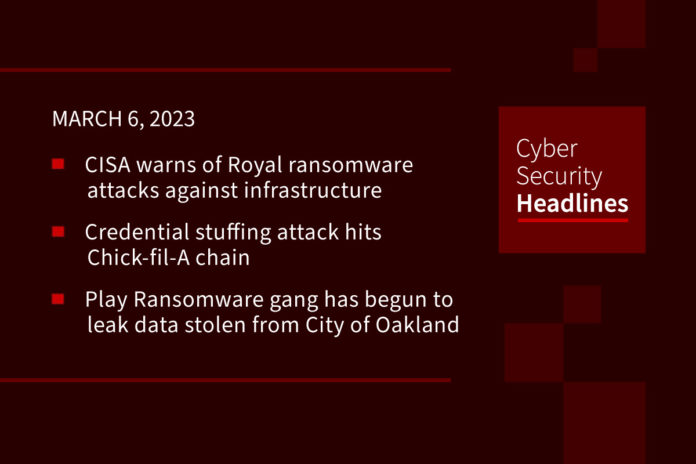
U.S. Government warns of Royal ransomware attacks against critical infrastructure
CISA issued an advisory on Thursday warning of an increased threat posed by Royal ransomware. This is the second warning the U.S. government has issued about Royal ransomware in recent months. In December, the U.S. Department of Health and Human Services (HHS) warned hospitals and organizations in the healthcare sector to stay on alert for Royal ransomware attacks. In this bulletin, CISA states, “Royal ransomware attacks have spread across numerous critical infrastructure sectors including, but not limited to, manufacturing, communications, healthcare and public healthcare (HPH), and education,” and it encourages network defenders to review theirs ransomware advisories and apply the included mitigations.
(CISA)
Credential Stuffing attack on Chick-fil-A
The fast-food restaurant chain Chick-fil-A had alerted over 71,000 users that their accounts had been compromised in a two-month-old credential stuffing campaign. The company described, in a statement, that “unauthorized parties launched an automated attack against our website and mobile application between December 18, 2022 and February 12, 2023 using email addresses and passwords obtained from a third-party source. Based on our investigation, we determined on February 12, 2023 that the unauthorized parties subsequently accessed information in your Chick-fil-A One account.”
Play ransomware gang leaks data stolen from City of Oakland
Following up on a story we have been covering for almost a month, the city of Oakland, California, which disclosed a ransomware attack and security breach that began on February 8, 2023, is now dealing with the breached data appearing on the dark web. The Play ransomware group has started leaking a 10 GB archive containing data such as employee information, passports, and IDs and “human rights violation information.” on its Tor leak site. For now, their message continues, in broken English, they are posting a partially published compressed 10 GB file. If there is no reaction, a full dump will be uploaded.
Microsoft OneNote files can be used to distribute malware
Microsoft OneNote has now become a tool for hackers to spread malware and enter corporate networks. The activity is largely a result of Microsoft disabling macros by default in Word and Excel Office documents, meaning threat actors began turning to other less commonly used file formats to distribute malware, such as ISO files and password-protected ZIP archives. Microsoft OneNote attachments use the ‘.one’ file extension and do not distribute malware through macros or vulnerabilities. Instead, threat actors create intricate templates that appear to be a protected document with a message to ‘double-click’ a design element to view the file.
Thanks to this week’s episode sponsor, Packetlabs

FTC to ban BetterHelp from sharing mental health data with advertisers
The Federal Trade Commission has taken steps to ban the online counseling service BetterHelp from sharing the sensitive mental health data with of its customers with advertising networks and marketers. According to Bleeping Computer, “a settlement between the FTC and BetterHelp also requires the company to pay $7.8 million as restitution to its users whose sensitive data has been shared with third parties such as Facebook and Snapchat.” The FTC states that BetterHelp “followed bad practices in handling the data of people who visited its website or used its apps, including those who have not signed up for its counseling services.”
TPM 2.0 flaws could impact billions of devices
The not-for-profit tech advisory organization Trusted Computing Group (TCG) is warning of vulnerabilities affecting the implementations of the Trusted Platform Module (TPM) 2.0 that could potentially lead to information disclosure or privilege escalation. The Trusted Platform Module (TPM) technology is a “hardware-based solution that provides secure cryptographic functions to the operating systems on modern computers, making them resistant to tampering.” The groups warns that an attacker who gains access to a TPM-command interface can “exploit the flaws sending maliciously-crafted commands to the module.” The issues are identified as CVE-2023-1017, an out-of-bounds write, and CVE-2023-1018, an out-of-bounds read. Researchers at Quarkslab point out that the vulnerabilities could potentially affect billions of devices, including IoT devices, servers, and embedded systems.
Critical flaw in Cisco IP phone series exposes users to command injection attack
On Wednesday, Cisco pushed out security updates to address a flaw impacting its IP Phone 6800, 7800, 7900, and 8800 Series products. Tracked as CVE-2023-20078, the flaw is rated 9.8 out of 10 and is a “command injection bug in the web-based management interface arising due to insufficient validation of user-supplied input.” This could lead to the injection of arbitrary commands that are executed with the highest privileges on the underlying operating system.
Last week in ransomware
This week was highlighted by a massive BlackBasta ransomware attack targeting DISH Network along with its subsidiaries, including SlingTV and Boost Mobile. As covered here on Cyber Security Headlines, the attack started on February 23rd, forcing the company to shut down portions of its IT systems, causing widespread outages among its services. Also, the U.S. Marshals service suffered a ransomware attack, including data theft. Attacks also happened at Canadian book store chain Indigo, British book store chain WH Smith, Tennessee State University, Southeastern Louisiana University, Pierce Transit, a bus company in Tacoma Washington, and Hatch Bank.