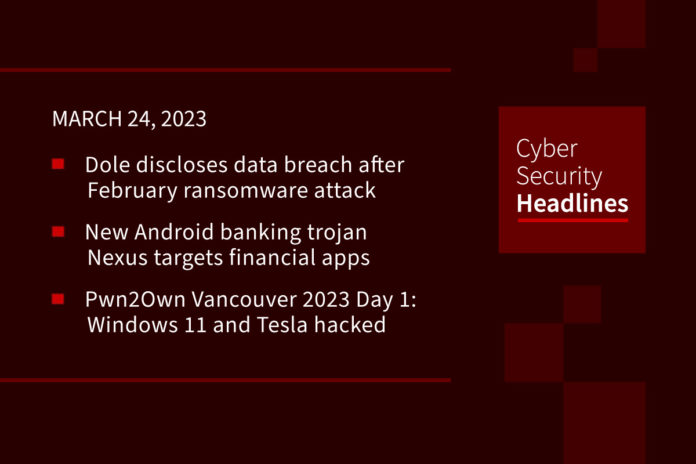
Dole discloses data breach after February ransomware attack
Last month, the food multinational Dole Food Company announced that it has suffered a ransomware attack that impacted its operations. It has now confirmed that threat actors behind the attack had access to the information of an undisclosed number of employees. Despite the company denying a huge impact on its operations, it was forced to shut down production plants and shipments for a short period.
New Android banking trojan targets financial apps
Already adopted by threat actors to target 450 financial applications, “Nexus provides all the main features to perform ATO attacks (Account Takeover) against banking portals and cryptocurrency services, such as credentials stealing and SMS interception,” said cybersecurity firm Cleafy in a recent report. It appears to be in its early stages of development, and is advertised as a subscription service a monthly fee of $3,000. Details of the malware were first documented by Cyble earlier this month, and the majority of the Nexus infections thus far have been reported in Turkey.
Pwn2Own Vancouver 2023 Day 1: Windows 11 and Tesla hacked
Security researchers have kicked off Pwn2Own Vancouver 2023 by revealing zero-day exploits and exploit chains for Tesla Model 3, Windows 11, and macOS zero-day exploits and exploit chains. A Tesla Model 3 is also one of the prized up for grabs in the contest. Adobe Reader, Microsoft’s SharePoint team collaboration platform, and Oracle VirtualBox were also taken down. Once zero-day vulnerabilities have been disclosed in the event, vendors have 90 days to create and release security fixes before Trend Micro’s Zero Day Initiative publicly discloses them.
Bogus ChatGPT extension steals Facebook cookies
A ChatGPT extension in the Chrome store that steals Facebook session cookies has been removed by Google, but more than 9,000 users have already installed it. The extension is named Chat GPT For Google, which is very similar in name and code to the real ChatGPT For Google extension. The fake extension is based on the same open source project that the real ChatGPT For Google uses. The bad actors merely had to add a few extra lines of code. They then distributed their malware through sponsored Google Search results for “Chat GPT 4.
Thanks to this week’s episode sponsor, Conveyor

Then you might want to check out Conveyor: the end-to-end trust platform helping infosec teams reduce incoming questionnaires and fly through the ones they do have to complete.
Give customers access to a self-serve trust portal to download docs and FAQs. For any remaining questionnaires that do come in, use our GPT-Questionnaire response tool or white-glove questionnaire completion service to knock them completely off your to-do list.
Learn more at www.conveyor.com.
Researchers discover advancements in China’s cyberespionage operations
Some recently discovered “digital intrusions” are reflecting an increased sophistication among China-linked hackers for evading detection inside a victim’s network. This ios according to researchers at Sentinel Labs and the German IT services company QGroup, based on studies of numerous intrusions into unnamed Middle Eastern telecoms. According to Cyberscoop, the researchers stated, “those attacks indicated that a years-long Chinese-aligned cyberespionage operation has been actively updating its abilities using a series of modifications to a widely used credential theft software package.”
UK government sets out vision for NHS cybersecurity
This new strategy is designed to boost resilience in the health and social care sector by 2030 with the goal of helping the sector’s organizations improve cyber-risk management, data protection and incident response and recovery. Details will be forthcoming in the summer but according to it announcement these will operate under five sectors:
• Identify where disruption will cause the greatest harm to patients, such as disruption to critical services
• Unite the sector to take advantage of scale, tap national resources and expertise, and accelerate response
• Ensure leaders are engaged, employees know the cyber basics and more security specialists are recruited
• Embed security into emerging technology to better protect it from cyber-threats
• Support every health and care organization to minimize the impact of incidents and recovery time
Hackers inject credit card stealers into payment processing modules
This credit card stealing campaign differs from others by hiding the malicious code inside the ‘Authorize.net’ payment gateway module for WooCommerce, thus evading detection by security scans. Previous attacks on commerce sites such as Magenta or WooCommerce incorporated malicious JavaScript inserted into the HTML of the store or customer checkout pages. Since online merchants now work with security software companies who the HTML of public-facing eCommerce sites, it has become more difficult for threat actors to hide. So, to evade detection, as Bleeping Computer reports, “the threat actors are now injecting malicious scripts directly into the site’s payment gateway modules used to process credit card payments on checkout. As these extensions are usually only called after a user submits their credit card details and checks out at the store, it may be harder to detect by cybersecurity solutions.”
North Korean APT group ‘Kimsuky’ targeting experts with new spearphishing campaign
Government agencies from Germany and South Korean are warning about a new spearphishing campaign from North Korean that targets experts on the peninsula. According to The Record, “the campaign gains access to victims’ Google accounts through the infection of Android phones through a malicious app on Google Play and the use of a malicious Chromium web browser extension.” In advisory released last week, the government agencies warned, “the hacking attack is mainly targeting experts on the Korean Peninsula and North Korea, but since the technology exploited in this attack can be used universally, it can be used by foreign affairs and security think tanks around the world as well as unspecified people.”