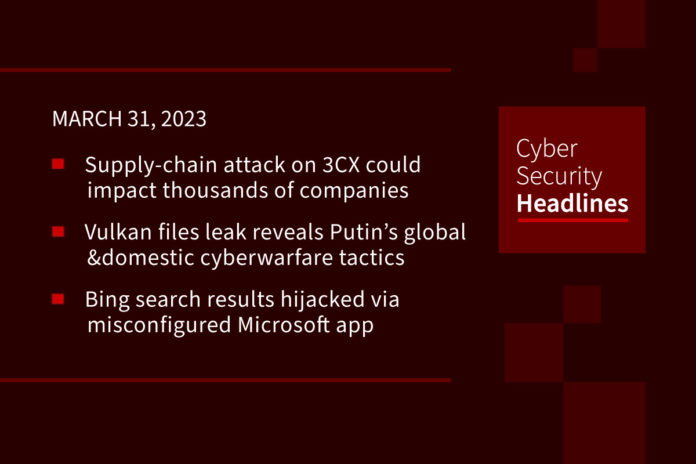
Supply-chain attack on business phone provider 3CX impacts some big names
A supply-chain attack on enterprise phone company 3CX may have exposed the networks of thousands of businesses. The company confirmed on Thursday that its desktop app had been bundled with malware. 3CX provides office phone systems to a number of well known companies and organizations. Chief information security officer Pierre Jourdan, described the intrusion as “the work of highly skilled hackers,” adding, “this appears to have been a targeted attack from an Advanced Persistent Threat, perhaps even state sponsored.”
Vulkan files leak reveals Putin’s cyberwarfare tactics
Thousands of pages of secret documents allegedly leaked by an anonymous whistleblower reveal how engineers at NTC Vulkan in Moscow have worked for Russian military and intelligence agencies to support hacking operations, train operatives before attacks on national infrastructure, and spread disinformation and control sections of the internet. The company is linked to the federal security service FSB, the GRU and SVR (Russia’s foreign intelligence organization). One document connects a Vulkan cyber-attack tool with the Sandworm hacking group and to NotPetya malware. Crystal-2V is a “training program for cyber-operatives in the methods required to bring down rail, air, and sea infrastructure.” The date from 2016 to 2021. Five western intelligence agencies confirmed the Vulkan files appear to be authentic.
Bing search results hijacked via misconfigured Microsoft app
BingBang is the name given by analysts at Wiz Research to describe a misconfigured Microsoft application that “allowed anyone to log in and modify Bing.com search results in real-time, as well as inject XSS attacks to potentially breach the accounts of Office 365 users.” The analysts reported the issue to Microsoft on January 31, and Microsoft confirmed a fix by March 28.
Over 70% of employees keep work passwords on personal devices
According to the latest mobile bring your own device (BYOD) security report from SlashNext, almost four out of every five employees “store sensitive work passwords on their personal phones, and 66% use their personal texting apps for work.” The report also suggests that “95% of security leaders are increasingly concerned about phishing attacks via private messaging apps.” SlashNext CEO Patrick Harr agrees that one reason for these numbers is that threat actors know “there are fewer security controls on personal mobile devices than on corporate ones.”
And now a word from our sponsor, Trend Micro

Clop hits Australia’s casino giant Crown Resorts
The casino company is the latest in a string of high profile organizations to have disclosed a data breach related to Fortra’s GoAnywhere MFT secure file transfer tool. The incident took place in January, but the company disclosed the data breach this week. A statement from Crown Resorts published on March 27, states in part, “we can confirm no customer data has been compromised and our business operations have not been impacted.”
US commits $25 million to Costa Rica to recover from Conti ransomware
The U.S. government is sending the money to the government of Costa Rica to help the country recover from a ransomware attack that occurred last year and that crippled several key agencies. In May 2022, Costa Rican president Rodrigo Chaves declared a state of emergency after the ransomware group “severely damaged the Ministry of Finance, the Ministry of Public Works and Transport and the Costa Rican Social Security Fund.” The gang posted messages calling for the overthrow of the government and demanded a $20 million ransom. The funding will be used to secure the country’s networks and defend its critical infrastructure.
17% of security leaders consider cybersecurity team fully-staffed
A recent study from Immersive Labs looked at security leaders’ perception of their own cyber resilience. The study shows that despite high overall confidence, leaders consider their teams to be insufficiently prepared for threats. 82% of respondents agree they could have mitigated “some to all of the damage of their most significant cyber incident in the last year if they were better prepared, and more than 80% don’t think, or are unsure, their teams have the capabilities to respond to future attacks.” Only 17% percent consider their cybersecurity team to be fully-staffed. Just under half of respondents “admit they aren’t able to measure cyber capabilities, further eroding confidence in the organization’s preparedness.”
Latitude Financial says data stolen by hackers belonged to way more than 330,000 customers – try 14 million
Latitude, a finance company that offers personal loans and finance for consumers shopping at a range of retail brands in Australia and New Zealand, announced on Monday that it had “detected suspicious activity on its networks earlier this month,” and gave a number of 330,000 customers potentially impacted. The breach now appears to include 7.9 million Australian and New Zealand driver license numbers, as well as 53,000 passport numbers provided by customers over the last 10 years, as well as a further 6.1 million PII records dating back to at least 2005.