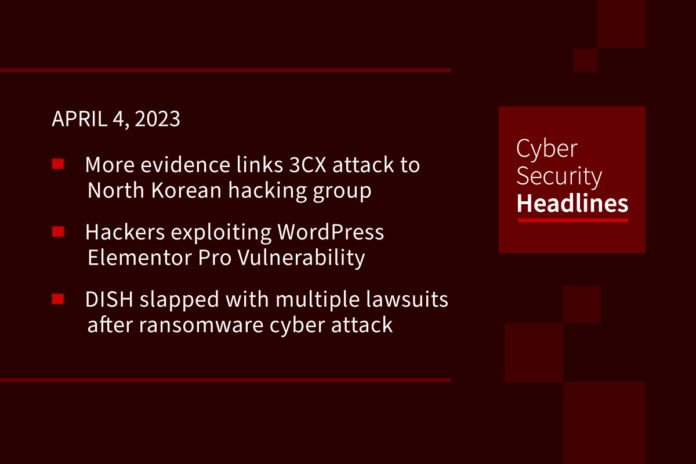
More evidence ties 3CX supply-chain attack to North Korean hacking group
There is more evidence that shows the supply-chain attack on phone technology company 3CX used code that “exactly matches” that seen in attacks by the Lazarus Group. Sophos provided the additional evidence on Friday, saying that the shellcode loader that was used has only previously been seen in incidents attributed to the Lazarus Group. They continued, “it’s clear the perpetrators were able to compromise the installation in a way that users unknowingly downloaded not only the original application but also additional malicious code.” The hackers modified the apps so they executed malicious commands “in the background, downloading malware that allowed them to steal sensitive information from the web browsers on users’ computers.”
Hackers exploit WordPress Elementor Pro Vulnerability
An unknown threat actor group continues to exploit a recently patched security vulnerability in the Elementor Pro website builder plugin for WordPress. The vulnerability, a case of broken access control, affects versions 3.11.6 and earlier and was mitigated by the release of version 3.11.7 on March 22. Elementor Pro is estimated to be used on over 12 million sites and the vulnerability wold allow an authenticated attacker to complete a takeover of a WordPress site that has WooCommerce enabled.
DISH faces lawsuits after ransomware cyber attack
Multiple class action lawsuits have been launched following a ransomware incident that was the cause of a multi-day network outage. The suits claim that “DISH overstated its operational efficiency while having a deficient cybersecurity and IT infrastructure. The legal actions aim to recover losses faced by DISH investors who were adversely affected by what has been dubbed a “securities fraud.”
LockBit announces leak of data stolen from South Korean National Tax Service
In late March, the LockBit ransomware gang claimed responsibility for an attack on the South Korean National Tax Service, placing the government agency on its Tor leak site and threatening the release of stolen data by April 1st, if their ransom demands were not met. The National Tax Service (NTS) assesses and collects internal taxes and functions as an external arm of the Ministry of Finance. At the time of this recording the group has yet to publish the stolen data, however, if the hack was real, the stolen data poses a severe risk to the privacy and security of South Korean citizens.
Thanks to this week’s episode sponsor, Normalyze
AlienFox malware targets API keys and secrets from AWS, Google, and Microsoft Cloud Services
AlienFox is “a new “comprehensive toolset” distributed on Telegram, and allowing threat actors to access and collect credentials and other data from API keys and popular cloud service providers. SentinelOne calls this “an unreported trend towards attacking more minimal cloud services, unsuitable for crypto mining, in order to enable and expand subsequent campaigns.” The malware is described by SentinelOne as “highly modular and constantly evolving to accommodate new features and performance improvements.”
Lewis & Clark College cyberattack claimed by Vice Society
The cybercrime group is now posting samples of passports an PII documents that include Social Security numbers, insurance files, W-9 forms, contracts and more. The school sent out several urgent messages on social media and on its website notifying students and employees that several of its systems were down. According to The Record, “the outages lasted until March 7. The Portland, Oregon, liberal arts college did not respond to requests for comment about whether a ransom was demanded or will be paid.”
QNAP fixes Sudo privilege escalation bug in NAS devices
Taiwanese vendor QNAP is urging customers to update their NAS devices to protect against a high-severity Sudo privilege escalation vulnerability tracked as CVE-2023-22809. According to Security Affairs, “the vulnerability was discovered by security firm Synacktiv, it is a sudoers policy bypass in Sudo version 1.9.12p1 when using sudoedit. An attacker can trigger the vulnerability to achieve privilege escalation by editing unauthorized files after appending arbitrary entries to the list of files to process.”
University student uses AI chatbot to get parking fine revoked
Millie Houlton said she received the parking infraction notice her local city council and was tempted to pay rather than having to spend time compiling a defense. Instead she asked ChatGPT to “please help me write a letter to the council, they gave me a parking ticket” and she sent that instead, after which the authority withdrew the fine notice. Houlton claimed the fine was wrongly issued for street parking given that she owns a permit. She added “the chatbot’s response was “great” and it explained the situation perfectly.”
(BBC News)