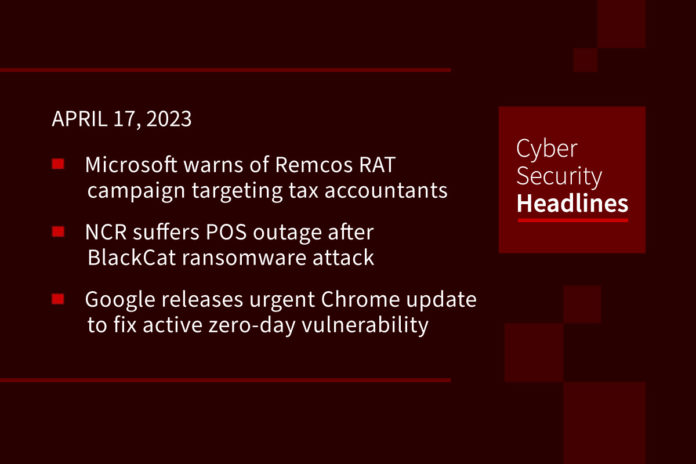
Microsoft warns of Remcos RAT campaign targeting tax accountants
Just ahead of U.S. Tax Day, Microsoft is warning of a new Remcos RAT campaign targeting US accounting firms as well as those who perform tax return preparation. The phishing attacks began in February and aim at tax preparation organizations, CPA and accounting firms, and professional service firms dealing in bookkeeping and tax. Crooks use files that look like tax documentation sent by a client. The message contains a link that directs them to a legitimate file hosting site containing malicious Windows shortcut (.LNK) files.
POS outage hits NCR after BlackCat ransomware attack
The Aloha POS platform is used in the hospitality industry and has been down since Wednesday. NCR disclosed on Saturday that the outage was caused by a ransomware attack on data centers used to power their Aloha POS platform.
Urgent Chrome update released to counter zero-day vulnerability
Google released the out-of-band updates on Friday. Tracked as CVE-2023-2033, the high-severity vulnerability has been described as “a type confusion issue in the V8 JavaScript engine.” The company acknowledged that “an exploit for CVE-2023-2033 exists in the wild,” but did not mention additional technical specifics or indicators of compromise (IoCs) that would prevent further exploitation by threat actors.
Lazarus shows new skills in DeathNote campaign
The Lazarus Group – a successful and notorious cybercrime group serving North Korean interests is showing new tactics and skills within its long-running campaign called DeathNote. While known for its focus on the cryptocurrency sector, observers have noted recent attacks on automotive, academic, and defense sectors in Eastern Europe and other parts of the world, in what’s perceived as a “significant” pivot, using job descriptions related to defense contractors and diplomatic services as its primary decoy. The DeathNote cluster is also tracked under the monikers Operation Dream Job or NukeSped.
Thanks to this week’s episode sponsor, Pentera

Pentera’s customers find that leveraging the Pentera automated security validation platform as part of their exposure management strategy increases their ability to identify security gaps, improves the efficiency of remediation processes, and maximizes their security readiness.
To learn more, visit Pentera.io
Microsoft shares fix for Outlook issue blocking access to emails
In a support document published on Thursday, Microsoft stated that after updating to Outlook Version 2303, users may be unable to view or access Microsoft 365 group calendars and email messages in Outlook Desktop. The buggy Outlook version was released to the Current Channel on March 28. Microsoft says the Outlook Team is working on a solution to address this known issue and shared a temporary workaround until a fix rolls out for those experiencing problems while trying to access emails.
German arms manufacturer Rheinmetall confirms cyberattack
The attack hit the company’s business unit, which supplies industrial customers, especially in the automotive sector. Its defense division was unaffected. It has been noted that Russian hacktivist group Killnet posted a message on their Telegram channel last month urging followers to launch a DDoS attack against Rheinmetall, which coincided with talks of constructing a new tank factory in Ukraine. According to The Record, “the war in Ukraine has turned Rheinmetall into one of Europe’s most important weapons suppliers, which makes it an attractive target for nation-state hackers.”
Siemens Metaverse exposes sensitive data
The Siemens Metaverse – a platform that aims to create digital ‘twins’ of its factories and offices, and built in partnership with Nvidia – has been found to be leaking sensitive information, which if picked up by threat actors, could have had devastating consequences for the company and other corporations using its services. According to Security Affairs, on March 1, the Cybernews research team discovered “an environment file hosted on a metaverse.siemens.com domain that contained ComfyApp credentials and endpoints. It also discovered Siemens leaking four sets of WordPress users, and three sets of backend and authentication endpoint URLs on different endpoints of the affected systems.” The most worrying discovery, Cybernews reported, was “that of exposed office management platform ComfyApp user credentials.” Siemens, on the other hand, said it considered the issue to be non-critical and added that it had been mitigated.
Last week in ransomware
Last week saw Yum! Brands – owner of KFC and Pizza Hut – sending data breach notifications for a ransomware attack in January and UK outsourcing organization remaining silent on details surrounding a Black Basta ransomware attack that occurred earlier this month. In other news, DarkAngels ransomware launched a data leak site, Vice Society now uses a custom PowerShell script for data exfiltration, a new Kadavro Vector Ransomware entered the environment, and LockBit claimed to have breached DarkTrace. A Windows zero-day was exploited in Nokoyawa ransomware attacks, Rochester Public Schools in Minnesota closed operations due to an attack, Clop releases 16,000 student documents in Tasmania , and the police department in Camden County, New Jersey confirmed that it was hit with a ransomware attack in March.