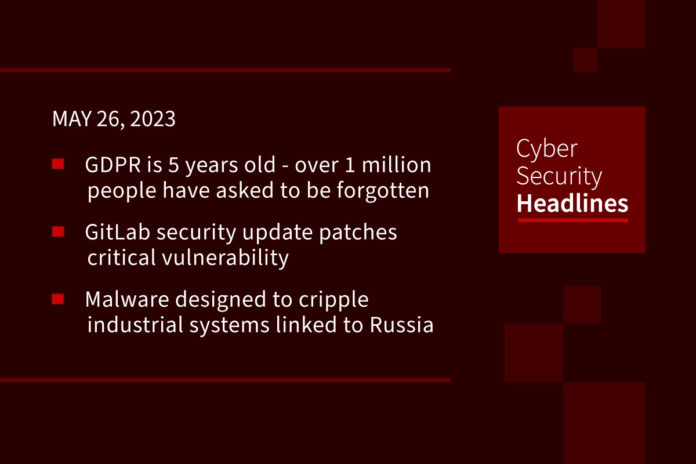
GDPR is 5 years old, and over 1 million people have asked to be forgotten
On the 5th birthday of GDPR, a new study from Surfshark shows that between 2015 to 2021, over 1 million “right to be forgotten” requests to delist certain search results were submitted to Google and Microsoft Bing, from 32 countries. Points from the study show France is in first place with over 255,000 requests; when the Covid-19 pandemic started, “right to be forgotten” cases rose nearly 30%; Estonia had the most requests per 10,000 people, more than 2.5 times higher than average, and 1 in 10 “right to be forgotten” web page delisting requests are crime-related.
GitLab security update patches critical vulnerability
GitLab has resolved a critical-severity vulnerability that impacted its Community Edition (CE) and its Enterprise Edition (EE). Tracked as CVE-2023-2825 the security defect has the maximum CVSS score of 10. According to GitLab, the issue started with GitLab CE/EE version 16.0.0 and was resolved on Tuesday with the release of version 16.0.1 of the platform. According to Security Week, the flaw was reported by a researcher named ‘pwnie’ via GitLab’s HackerOne-hosted bug bounty program.
Mysterious malware designed to cripple industrial systems linked to Russia
According to a report released Thursday from Mandiant, a new and rare type of malicious software dubbed “CosmicEnergy” has been designed to disrupt industrial systems in power plants. The Mandiant report links the software to a Russian telecom firm. Its discovery is somewhat unusual since it was uploaded to VirusTotal, which is a service owned by Google that scans URLs and files for malware. The upload, made in December 2021, came from a user with a Russian IP address and was found through threat hunting and not by following an attack on a critical infrastructure system. Cyberscoop suggests CosmicEnergy now joins “a highly specialized group of malware such as Stuxnet, Industroyer and Trisis that are purpose built for industrial systems.”
Chinese hackers that triggered US alarm hit defense targets
A group of Chinese hackers who recently triggered a multi-nation alert have been conducting a cyberespionage campaign against military and government targets in the United States, researchers said on Thursday. The group – dubbed “Volt Typhoon” by Microsoft – was the subject of an alert issued by cybersecurity and intelligence agencies in the United States, Britain, and their close allies. That warning said Volt Typhoon was developing capabilities “that could disrupt critical communications infrastructure between the United States and Asia region during future crises.” The group has targeted critical infrastructure organizations in the U.S. Pacific territory of Guam, Microsoft said.
(Reuters)
Thanks to this week’s episode sponsor, Sonrai Security

Zyxel Issues critical security patches for firewall and VPN products
According to The Hacker News, “Zyxel has released software updates to address two critical security flaws affecting select firewall and VPN products that could be abused by remote attackers to achieve code execution.” The flaws – CVE-2023-33009 and CVE-2023-33010 – are buffer overflow vulnerabilities with CVSS scores of 9.8. Credit for discovery and reporting of these flaws goes to security researchers from TRAPA Security and STAR Labs SG. This most recent advisory comes less than a month after Zyxel delivered fixes for a separate critical security flaw in its firewall devices.
North Korea-linked APT Lazarus Group targeting vulnerable Microsoft IIS servers
Researchers from AhnLab Security Emergency Response Center have reported that the Lazarus APT Group is “targeting vulnerable versions of Microsoft IIS servers in a recent wave of malware-based attacks.” The attackers are using a DLL side-loading (T1574.002) technique to deliver a malicious DLL (msvcr100.dll) that they place in the same folder path as a normal application (Wordconv.exe). The library is then executed via the Windows IIS web server process. The researchers note a similarity between this DLL technique and another previously used by the Lazarus actors.
Ransomware gang pulls Philadelphia Inquirer listing after victim questions documents
The Cuba ransomware group removed its listing of The Philadelphia Inquirer on its darknet extortion site on Wednesday after the paper questioned the authenticity of documents that were offered for download. Cuba claimed to have posted a collection of files stolen from the Inquirer, including “financial documents, correspondence with bank employees, account movements, balance sheets, tax documents, compensation, source code,” but the publisher said that the company had seen no evidence that the information was actually related to the newspaper.
Dark Frost botnet launches DDoS Attacks on gaming industry
Dark Frost is a new botnet called that has been modeled after Gafgyt, QBot, Mirai, and other malware strains, and has expanded to encompass hundreds of compromised devices,” Akamai security researcher Allen West said in a new technical analysis. According to The Hacker News, its targets include “gaming companies, game server hosting providers, online streamers, and even other gaming community members with whom the threat actor has interacted directly.”