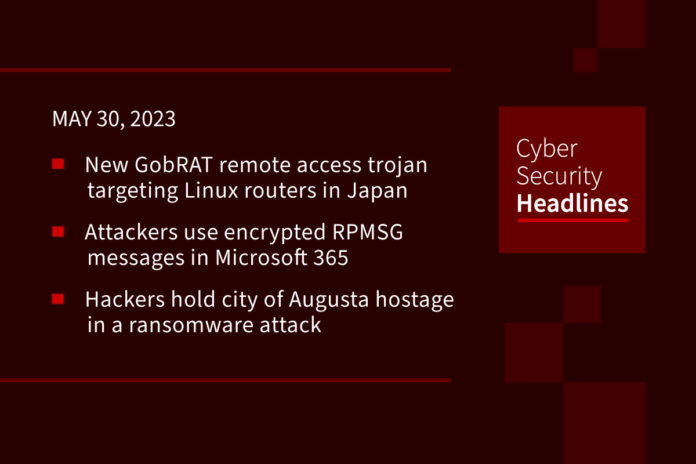
New GobRAT remote access trojan targeting Linux routers in Japan
This is a new Golang remote access trojan (RAT) called GobRAT. “Initially, the attacker targets a router whose WEBUI is open to the public, executes scripts possibly by using vulnerabilities, and finally infects the GobRAT,” the JPCERT Coordination Center (JPCERT/CC) said in a report published yesterday. Once the internet-exposed router is compromised, a loader script deploys that acts as a conduit for GobRAT, which, when launched, masquerades as the Apache daemon process to evade detection. The loader is also able to disable firewalls, while GobRAT communicates with a remote server via the Transport Layer Security (TLS) protocol to receive as many as 22 different encrypted commands for execution.
Attackers use encrypted RPMSG messages in Microsoft 365 targeted phishing attacks
Researchers at Trustwave are warning of threat actors who are using encrypted RPMSG attachments sent via compromised Microsoft 365 accounts in a phishing campaign aimed at stealing Microsoft credentials. RPMSG files deliver emails with Rights-Managed Email Object Protocol enabled. According to Security Affairs, “This protocol controls e-mail access and usage permissions. Instead of a plain text, e-mails via RPMSG files are sent with content encrypted and stored as encrypted file attachment.” The recipients then read the encrypted messages after being authenticated with their Microsoft account or obtaining a one-time passcode. With this attack, the message attempts to trick recipients into clicking the “Read the message” button to decrypt the protected message after which, the recipients are redirected to an Office 365 webpage to sign into their Microsoft account. Once authenticated, the victims are redirected to a page displaying the attackers’ phishing email.
Hackers hold city of Augusta hostage in a ransomware attack
A ransomware attack on the city of Augusta, Georgia is apparently the work of the BlackByte group, who has claimed responsibility. The group has posted 10GB of sample data and states they have a much more available, including payroll information, contact details, PII, physical addresses, budget allocation data, and more, although this has not been independently verified. The group accuses the city of being “sleepy” in its response, and is posting the sample files, to help it “wake up.” Augusta’s mayor has refuted the claims about the ransom demand.
MCNA Dental data breach impacts 8.9 million people after ransomware attack
Managed Care of North America (MCNA) Dental, one of the largest government-sponsored (Medicaid and CHIP) dental care and oral health insurance providers in the U.S., has announced a data breach notification on its website. Almost 9 million patients may have had their personal data compromised. MCNA said on Friday that it became aware of “unauthorized access to its computer systems” on March 6th, and further investigation showed that that the hackers first obtained access to its network on February 26th. On March 7, the LockBit ransomware gang announced responsibility for the attack, publishing samples of stolen data.
Thanks to this week’s episode sponsor, Barricade Cyber Solutions

Brazilian hackers target Portuguese financial institutions
A hacking organization from Brazil has targeted customers of more than 30 Portuguese financial institutions this year, according to a report released Thursday by SentinelLabs. The campaign, dubbed Operation Magalenha, initially used cloud service providers like DigitalOcean and Dropbox, but as these firms tightened rules on how their services are used, it moved web hosting provider TimeWeb, based in Russia. The group uses a pair of backdoors “deployed simultaneously to give the attacker control over infected machines.” This technique has been named “PeepingTitle,” since the backdoors allow the attackers to keep an eye on window interaction, as well as taking screenshots, terminating processes and deploying additional malware such as data exfiltration tools.
Barracuda Networks issue added to CISA vulnerability list
On Friday, a bug that had been recently patched recently in Barracuda Networks’ email security hardware, was added to the federal catalog of exploited vulnerabilities. The company had pushed out two separate patches to its Email Security Gateway (ESG) appliance to fix a flaw “in a module which initially screens the attachments of incoming emails.” CISA warned that the bug, now tracked as tracked as CVE-2023-2868 and vulnerabilities like it, are frequent attack vectors for malicious cyber actors and pose significant risks. No other Barracuda Networks products were affected, the company said.
Lender OneMain fined $4.25 million for cybersecurity lapses
OneMain Financial Group specializes in issuing loans to people with “non-prime” credit histories. It must now pay a $4.25 million penalty for cybersecurity lapses that were found during a government investigation. According to The Record, The Department of Financial Services (DFS) investigation found that OneMain Financial “allowed local administrative users to share accounts and permitted those accounts to use the default password that users got when they were onboarded.” The DFS also noted it used a “non-formalized project administration framework developed in-house that failed to address certain key software development life cycle phases, it did not assess third-party vendors properly, despite having a risk policy in place, and further failed to appropriately adjust several vendors’ risk scores even after the occurrence of multiple cybersecurity events. OneMain has responded by saying it has “long since addressed” problems found in the investigation, which examined its policies from 2017 to early 2020.
Last week in ransomware
As mentioned earlier in this episode, Augusta, Georgia has joined Dallas on the list of cities being subject to cyberattack. BlackBasta waged an attack on German arms manufacturer Rheinmetall and ABB confirmed that data was stolen during an attack earlier this month. Reports released by security firms and researchers include the ALPHV/BlackCat ransomware gang is now using the malicious POORTRY Windows kernel driver, Iranian hackers have created a new Moneybird ransomware to attack Israeli organizations, a new Buhti ransomware operation is using the leaked LockBit and Babuk encryptors, and ransomware affiliate Bassterlord released a “slightly” edited but highly sought-after version of his ransomware manual version 2.0 that was being sold for $10,000 on hacker forums.