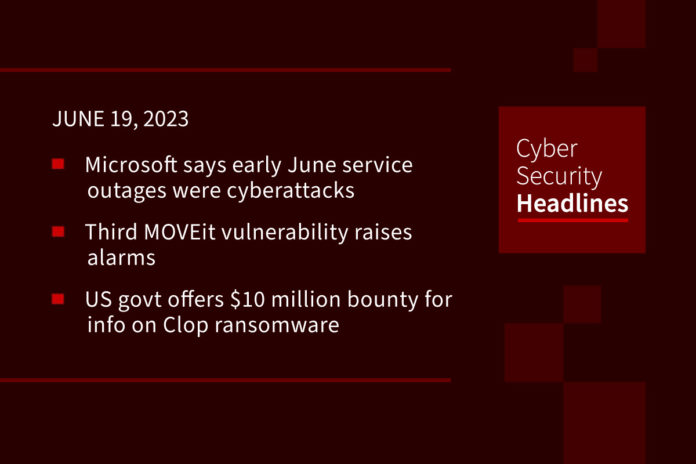
Microsoft says early June service outages were cyberattacks
Microsoft said on Friday that it was indeed cyberattacks that that caused outages and affected certain of its services in June. The company adds that it saw no evidence of any customer data being accessed or compromised. It has opened an investigation and has begun tracking a threat actor it refers to as Storm-1359, but has not confirmed whether this group is the party responsible for the attack.
(Reuters)
Third MOVEit vulnerability raises alarms as US Agriculture Department says it may be impacted
This third vulnerability is causing alarm among U.S. officials and cybersecurity researchers after several government agencies have confirmed they were affected by a hack exploiting the first bug. Progress Software told Recorded Future News that an “independent source disclosed the new vulnerability.” Tracked as CVE-2023-35708, this bug could potentially give threat actors escalated privileges and access to a victim’s environment. Although Progress has not seen indications that this new vulnerability has been exploited, and although it has developed a patch, representatives state it is “extremely important” that all MOVEit customers take immediate action to address the issue.
US govt offers $10 million bounty for info on Clop ransomware
The Rewards for Justice program, sponsored by the U.S. State Department has announced an up-to $10 million bounty for information linking the Clop ransomware attacks to a foreign government. Posting on Twitter, it offered the rewards for information on threat actors and attacks impacting the national security of the USA. The Rewards for Justice program was “initially launched to gather information on terrorists targeting U.S. interests,” the program has since expanded to include information on cybercriminals.
SMS delivery reports can be used to infer recipient’s location
Freaky Leaky SMS, is the name of a new side-channel attack devised by a team of university researchers. It leverages the timing of SMS delivery reports to triangulate a recipient’s location. As defined by Bleeping Computer, “SMS delivery reports are handled by the SMSC (short message service center) of the mobile network to inform when a message has been delivered, accepted, failed, is undeliverable, has expired, or has been rejected.” Freaky Leaky SMS uses a machine learning algorithm to analyze timing data in SMS responses and currently boasts accuracy of up to 96% for locations across different countries and up to 86% for two locations in the same country.

GravityRAT Android trojan steals WhatsApp backups and deletes files
This is an updated version of an Android remote access trojan and disguises itself as messaging apps BingeChat and Chatico. It has been in operation since June 2022. ESET researcher Lukáš Štefanko said, in an ESET report published last week, “notable in the newly discovered campaign, GravityRAT can exfiltrate WhatsApp backups and receive commands to delete files.” According to The Hacker News, “GravityRAT is the name given to a cross-platform malware that’s capable of targeting Windows, Android, and macOS devices.” ESET is tracking the activity under the name SpaceCobra.
(The Hacker News and WeLiveSecurity)
New Linux backdoor utilizing DNS-over-HTTPS tunneling for covert command-and-control
Threat actor ChamelGang is expanding its skillset by using a previously undocumented implant to backdoor Linux systems. Malware named ChamelDoH is a C++ based tool for communicating via DNS-over-HTTPS (DoH) tunneling. ChamelGang was first discovered by the Russian cybersecurity firm Positive Technologies who desrcibed its attacks on fuel, energy, and aviation production industries in Russia, the U.S., India, Nepal, Taiwan, and Japan. Attack chains deplyed by ChamelGang have taken advantage of vulnerabilities in Microsoft Exchange servers and Red Hat JBoss Enterprise Application to carry out data theft attacks via a passive backdoor called DoorMe.
Intel to invest $25 billion in Israel factory in record deal, Netanyahu says
Intel Corp. will spend $25 billion on a new factory in Israel, according to Prime Minister Benjamin Netanyahu speaking on Sunday. He calls this the largest-ever international investment in the country. The factory, located in the central town Kiryat Gat, is due to open in 2027 and will operate through 2035. Intel has grown to become Israel’s largest privately held employer and exporter, having existed there for almost fifty years.
(Reuters)
Last week in ransomware
Last week largely belonged to the MOVEit Transfer extortion attacks. On Wednesday, the Clop gang started listing the names of 37 breached organizations, warning that data would be leaked in seven days if a ransom was not negotiated. “Many organizations decided to disclose the breaches rather than negotiating, warning impacted people that their data was exposed.” We also learned more about ransomware attacks this week, with the Medusa operation extorting Argentina’s National Securities Commission (CNV) and Rhysida ransomware leaking data stolen from the Chilean Army, and numerous branches of the Swiss government claimed by the NoName hacking group.