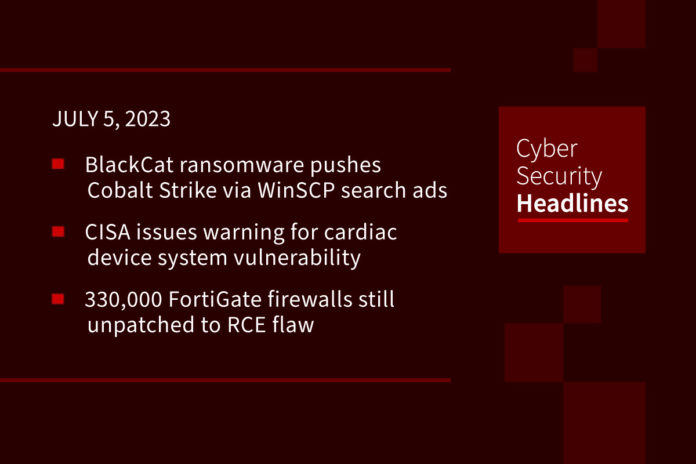
BlackCat ransomware pushes Cobalt Strike via WinSCP search ads
Analysts at Trend Micro are warning of a previously unknown ransomware infection vector delivered as a malvertizing campaign. This is being run by the BlackCat ransomware group, also known as ALPHV, and lures victims toward fake pages that mimic the official website of the WinSCP file-transfer application for Windows, to deliver malware-ridden installers. “WinSCP (Windows Secure Copy) is a free and open-source application with file transfer capabilities that sees 400,000 weekly downloads on SourceForge alone.” The BlackCat campaign drops a modified python310.dll that contains a Cobalt Strike beacon that connects to a command-and-control server address.
CISA issues warning for cardiac device system vulnerability
The warning identifies a device from medical technology company Medtronic. Tracked as CVE-2023-31222 it carries a “critical” CVSS score of 9.8 and affects the company’s Paceart Optima software that runs on a healthcare organization’s Windows server and stores and retrieves cardiac device data from programmers and remote monitoring systems from all major cardiac device manufacturers to aid in standard workflows. Medtronic said in an advisory that if exploited, the vulnerability allows hackers to delete, steal, or modify data from a cardiac device. Hackers can also use the device’s issues to penetrate into a healthcare organization’s network.x`
330,000 FortiGate firewalls still unpatched to CVE-2023-27997 RCE flaw
Following up on a story we brought you last month, Cybersecurity firm Bishop Fox, in a report published last week, said that “out of nearly 490,000 Fortinet SSL-VPN interfaces exposed on the internet, about 69 percent remain unpatched.” Labeled as CVE-2023-27997 with a CVSS score of 9.8), the flaw, also called XORtigate, is a critical vulnerability impacting Fortinet FortiOS and FortiProxy SSL-VPN appliances that could allow a remote attacker to execute arbitrary code or commands via specifically crafted requests.”
(The Hacker News and Bishop Fox)
DDoSia attack tool evolves with encryption, targeting multiple sectors
The DDoSia attack tool just gets worse, with a new version that leverages a new mechanism that retrieves a list of targets that can be bombarded with junk HTTP requests. The updated variant is written in Golang, and “implements an additional security mechanism to conceal the list of targets, which is transmitted from the [command-and-control] to the users,” according to cybersecurity company Sekoia in a technical write-up. According to The Hacker News, “DDoSia is attributed to a pro-Russian hacker group called NoName(057)16. Launched in 2022 and a successor of the Bobik botnet, the attack tool is designed for staging distributed denial-of-service (DDoS) attacks against targets primarily located in Europe as well as Australia, Canada, and Japan.”
Thanks to this week’s episode sponsor, SlashNext

Threads, Instagram’s Twitter competitor, is expected July 6
Threads, the name of Instagram’s rumored Twitter competitor, became available on the iOS App Store in the U.S .this week, and is expected to launch tomorrow, July 6. A strategic advantage that Threads has over other Twitter competitors is that it will directly port over a member’s Instagram followers and lists, removing the need to build a community from scratch. Few details about its functionality have been released, although according to an article published by online finance magazine Money Control in March of this year, its platform may be decentralized and compatible with Mastodon.
(TechCrunch and MoneyControl)
Thirty-three US hospitals hit by ransomware this year
According to Brett Callow, threat analyst for the New Zealand-based anti-malware specialist Emsisoft, at least 19 US healthcare organizations have been breached by ransomware gangs so far this year. Callow stated that, according to Emsisoft data, those 19 providers operate 33 hospitals and at least 16 of the 19 had data exfiltrated. The Emsisoft report is careful to underscore the potential magnifying effect of an HCO or an HCO partner being compromised, describing an attack on CommonSpirit Health last year which operates more than 140 hospitals, as well as the recent Black Cat/ALPHV group which recently added Barts Health NHS Trust to its leak site. Barts oversees three major hospitals in London.
Microsoft denies major customer-breach
Microsoft has replied to claims from Anonymous Sudan that the group had managed to breach the company and obtain account access for 30 million customers. According to InfoSecurity Magazine, the group had allegedly announced a successful hack, offering to sell the haul for $50,000, and attaching what it claimed to be a “small sample” of compromised details as proof of its word. Microsoft stated that “at this time, our analysis of the data shows that this is not a legitimate claim and an aggregation of data. We have seen no evidence that our customer data has been accessed or compromised.”
Chinese hackers target European embassies with HTML smuggling technique
Researchers from CheckPoint said Monday that this espionage campaign “represents a larger trend within the Chinese ecosystem, pointing to a shift to targeting European entities, with a focus on their foreign policy.” The hackers used a new delivery method to deploy a modular PlugX malware implant, effectively smuggling it inside HTML documents, something which CheckPoint warned had “until recently helped the campaign fly under the radar.” Samples of lures posted to the VirusTotal malware repository had filenames that “strongly suggest that the intended victims were diplomats and government entities,” according to CheckPoint.