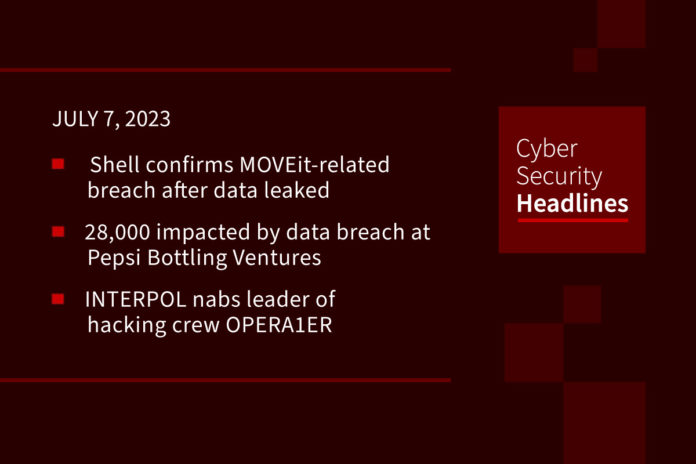
Shell confirms MOVEit-related breach after ransomware group leaks data
Energy company Shell has confirmed that employee-related information was compromised as a result of the recent MOVEit Transfer hack. A statement issued on Wednesday confirmed the MOVEit hack, clarifying that the MFT software “was used by a small number of Shell employees and customers.” Shell emphasized that “this was not a ransomware event” and that there is no evidence of any other IT systems being affected.
(SecurityWeek and Shell)
28,000 impacted by data breach at Pepsi Bottling Ventures
The breach at the independent bottling company was discovered on January 10, with actual theft occurring between December 23, 2022, and January 19, 2023. It resulted in the personal, financial, and health information of the company’s employees being accessed by an unauthorized party. Pepsi Bottling Ventures has not revealed how many individuals were affected. The stolen information, the company says, belongs to current and former employees and to contractors.
INTERPOL nabs the leader of hacking crew OPERA1ER’s
A suspected senior member of French hacking crew OPERA1ER has been arrested as part of operation Nervone, according to Interpol. “The group is believed to have stolen an estimated USD 11 million — potentially as much as 30 million — in more than 30 attacks across 15 countries in Africa, Asia, and Latin America,” the agency said. The arrest was made by authorities in Côte d’Ivoire early last month with assistance from the U.S. Secret Service’s Criminal Investigative Division and Booz Allen Hamilton DarkLabs.
(The Hacker News and Interpol)
Cisco warns of bug that lets attackers break traffic encryption
Cisco is warning customers yesterday of a high-severity vulnerability tracked as CVE-2023-20185, which impacts some data center switch models and allows attackers to tamper with encrypted traffic. According to Bleeping Computer, “the vulnerability only impacts Cisco Nexus 9332C, 9364C, and 9500 spine switches (the last ones equipped with a Cisco Nexus N9K-X9736C-FX Line Card) only if they are in ACI mode, are part of a Multi-Site topology, have the CloudSec encryption feature enabled, and are running firmware 14.0 and later releases. Successful exploitation allows unauthenticated attackers to read or modify intersite encrypted traffic exchanged between sites remotely.”
Thanks to this week’s episode sponsor, SlashNext

Microsoft investigates Outlook.com bug breaking email search and fixes bug behind Windows LSA protection warnings
A ongoing issue that prevents Outlook.com users from searching their emails and triggering 401 exception errors, is being investigated by Microsoft. According to some reports, the search function is no longer working on the web, while the mobile version doesn’t seem affected. Other customers and users are having issues when contacting Microsoft 365 personal support, becoming trapped in a loop of sign-in and Office 365 service choice prompts. Microsoft is also pushing a Defender Antivirus update (first issued in April and pulled in May) that fixes a known issue triggering Windows Security warnings that Local Security Authority (LSA) Protection is off.
(Bleeping Computer and Bleeping Computer)
Vulnerability in SolarView product can be exploited in attacks targeting organizations in the energy sector
Researchers from VulnCheck have reported a vulnerability in the solar power monitoring product Contec SolarView that can be exploited in attacks targeting the energy sector. Labelled as CVE-2022-29303 it is an unauthenticated and remote command injection vulnerability impacting the Contec SolarView Series, which, according to Contec, has been introduced at more than 30,000 power stations. According to Security Affairs, “since March 2023, researchers at Palo Alto Networks Unit 42 have observed a new variant of the Mirai botnet targeting multiple vulnerabilities in popular IoT devices, including the CVE-2022-29303. VulnCheck experts discovered, using Shodan, more than 615 internet-exposed SolarView installs, 425 of them running vulnerable versions.”
Silentbob campaign: cloud-native environments under attack
Cybersecurity researchers are investigating an attack infrastructure that may be part of a “potentially massive campaign” against cloud-native environments. Cloud security firm Aqua stated, “This infrastructure is in early stages of testing and deployment, and consists of an aggressive cloud worm, designed to deploy on exposed JupyterLab and Docker APIs to deploy Tsunami malware, cloud credentials hijack, resource hijack, and further infestation of the worm.” Silentbob is said to be linked to the infamous cryptojacking group tracked as TeamTNT, citing overlaps in tactics, techniques, and procedures (TTPs). Alternatively, it could be the work of an “advanced copycat.”
New StackRot Linux kernel flaw allows privilege escalation
A serious vulnerability affecting multiple Linux kernel versions could be triggered with “minimal capabilities.” This is according to security researcher Ruihan Li. Labelled as StackRot (CVE-2023-3269) it can be used to compromise the kernel and elevate privileges. A patch has been available for the affected stable kernels since July 1 and full details about the issue along with a complete exploit code are expected shortly. StackRot impacts a the kernel’s memory management subsystem on Linux versions 6.1 through 6.4.