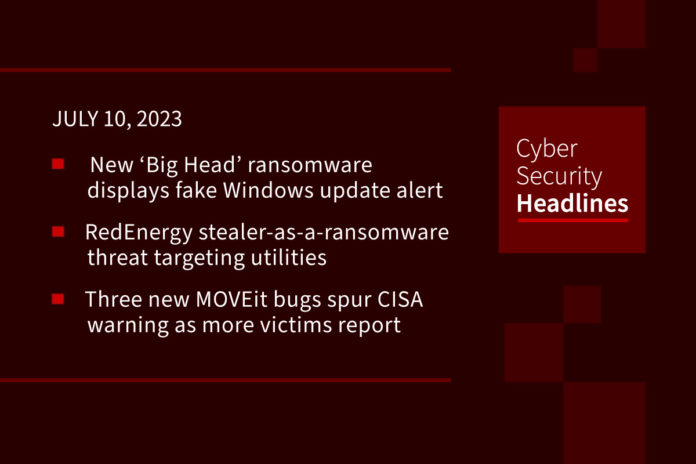
New ‘Big Head’ ransomware displays fake Windows update alert
This recently emerged ransomware strain may be spreading through malvertising that promotes fake Windows updates and Microsoft Word installers. Two samples of the malware were initially analyzed by Fortinet, and on Friday, Trend Micro published a technical report on Big Head that claiming that both those variants and a third they sampled originate from a single operator who is likely experimenting with different approaches to optimize their attacks. Big Head ransomware is a .NET binary that installs three AES-encrypted files on the target system: one is used to propagate the malware, another is for Telegram bot communication, and the third encrypts files and can also show the user a fake Windows update.
RedEnergy stealer-as-a-ransomware threat targeting energy and telecom sectors
RedEnergy is a stealer-as-a-ransomware and is targeting energy utilities, oil, gas, telecom, and machinery sectors in Brazil and the Philippines. Researchers at Zscaler stated, the .NET malware “possesses the ability to steal information from various browsers, enabling the exfiltration of sensitive data, while also incorporating different modules for carrying out ransomware activities.” The objective, they noted, is to couple data theft with encryption with the goal of inflicting maximum damage to the victims. It uses reputable LinkedIn pages to target its victims, redirecting users to a bogus landing page that prompts them to then update their web browsers by clicking on the appropriate icon (Google Chrome, Microsoft Edge, Mozilla Firefox, or Opera), which results in the download a malicious executable.
(The Hacker News and Zscaler blog)
Three new MOVEit bugs spur CISA warning as more victims report breaches
On Friday the Federal Government warned that three new vulnerabilities have been discovered in the MOVEit file transfer software. Progress Software released a new package of patches to resolve the three bugs, labeled CVE-2023-36932, CVE-2023-36933 and CVE-2023-36934. These latest issues are the fourth, fifth and sixth problems found in the software since May. Brett Callow, a threat analyst for Emsisoft who has been tracking the situation, said the number of reported victims has now reached at least 230.
More than 42,000 affected by ransomware attack on pro bono California law firm
A February ransomware attack on the offices of The Law Foundation of Silicon Valley has resulted in the leak of significant PII including Social Security numbers, medical records, immigration numbers, digital signatures and much more. In March, the AlphV/Black Cat ransomware group took credit for the attack. The firm helps out around 10,000 people per year with free legal services.
Thanks to this week’s episode sponsor, Opal

Charming Kitten hackers use new ‘NokNok’ malware for macOS
A new campaign being attributed to the APT group Charming Kitten is using a new malware called NokNok, which targets macOS systems. The campaign, which started in May, uses LNK files to deploy payloads rather than Word documents. Google associates the threat actor to the Iranian state, more specifically, the Islamic Revolutionary Guard Corps (IRGC).
Following BreachForum’s takedown, its replacement emerges
Less than a month after the high-profile takedown in June 23 of the notorious cybercrime bazaar BreachForums, a new version is already active, and Oleg Dyorov, head of the cybercrime investigation team within Group-IB’s threat intelligence unit, says “it is expected that more cybercriminals, old-timers and new ones, will join the new forum, which is more likely to lead to various high-profile leaks, publications and sales of various databases.” The FBI arrested Conor Fitzpatrick, the alleged administrator of the original BreachForums, in March at his family home in New York, months before seizing the site’s infrastructure. As soon as Fitzpatrick was in custody, a flurry of forums, new and old, jostled for position, leading to rival operators hacking into competitors’ forums and leaking user databases.
39% of businesses faced a cloud environment data breach last year
Thales has released a new cloud security report that reveals that 39% of businesses experienced a data breach in their cloud environment last year, which is an increase on the 35% reported in 2022. Human error was reported as the leading cause of cloud data breaches by over half surveyed. Three quarters of businesses said that almost half of their data stored in the cloud is classified as sensitive, and 38% ranked SaaS applications as the leading target for hackers, closely followed by cloud-based storage at 36%.
Nickelodeon probes claims of massive data leak as SpongeBob fans rejoice
Nickelodeon says it is investigating claims that “decades old” material was stolen and leaked online. There are reports of up to 500GB of snatched animation files being made available. According to The Register, “a spokesperson from Nickelodeon has confirmed they are aware of the social media posts that allege the theft, and are investigating…and that the alleged leaked content appears related to production files and not employee or user data.” The material, if genuine, would include never-released TV shows and scripts belonging to the animation department.