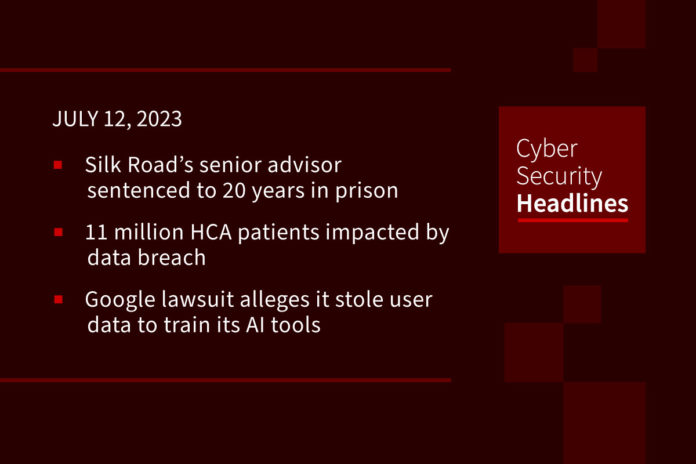
Silk Road’s senior advisor sentenced to 20 years in prison
On Tuesday, the US Justice Department announced that Roger Thomas Clark, a/k/a “Plural of Mongoose” and “Variety Jones,” was sentenced to 20 years in prison for his role as the top adviser to “Silk Road” online black market operators. Clark is accused of conspiring to sell $213 million worth of illegal drugs and other illicit goods and services (including murder for hire) to more than 100,000 buyers during the market’s operation from 2011 until 2013. Silk Road’s operator, Ross Ulbricht, a/k/a “Dread Pirate Roberts,” described Clark as a “real mentor” advising him about Silk Road’s security vulnerabilities, technical infrastructure, and how to govern site users and vendors.
(DoJ)
11 million HCA patients impacted by data breach
HCA Healthcare, operator of US and UK hospitals and healthcare services, announced that its network was compromised, leading to the theft of data belonging to more than 11 million of its patients. On July 5, reports emerged that stolen HCA data was being offered up for sale on the Dark Web. HCA confirmed that patient data including names, contact info, dates of birth, and appointment details, were stolen in the cyberattack, but added that credit card and medical info, and social security numbers were not affected. Threat actors threatened to leak the entire trove of HCA data if the company failed to meet its demands by this past Monday.
Google lawsuit alleges it stole user data to train its AI tools
On Tuesday, Google’s parent company, Alphabet, and its AI subsidiary, DeepMind, was hit with a lawsuit alleging the company scraped data from millions of users without their consent in order to develop its artificial intelligence products including Bard.The suit was filed by Clarkson Law Firm and alleges that Google violated copyright law due to, “secretly stealing everything ever created and shared on the internet by hundreds of millions of Americans.” While Google’s privacy policy explicitly states the company may use publicly accessible information to train its AI models, attorneys at Clarkson say that ‘publicly available’ does not mean the info is free to use for any purpose. The lawyers added that Google needs to provide people with an opt-out option. The suit is seeking a temporary freeze on commercial access to and commercial development of Google’s generative AI tools.
(CNN)
California resident charged with cyberattack on water treatment facility
A federal grand jury has indicted 53-year-old Rambler Gallo, for intentionally causing damage to a protected computer. Gallo was an employee of an unnamed private company that contracted with Californian water treatment facility, Discovery Bay. Gallo was responsible for maintaining Discovery Bay’s instrumentation and the computer systems used to control the electromechanical processes. Upon resigning from the company in January 2021, Gallo allegedly remotely accessed Discovery Bay’s network and uninstalled the main operational and monitoring system that protected the entire water treatment system, including water pressure, filtration, and chemical levels. Gallo faces a maximum statutory penalty of 10 years in prison and a fine of $250,000. The court could also tack on a term of supervised release, additional assessments, and restitution.
And now a word from our sponsor, Opal

Hackers exploit Windows policy loophole to forge driver signatures
Chinese-speaking threat actors have been observed exploiting a loophole in Microsoft Windows policy to forge signatures on kernel-mode drivers. While Microsoft restricts how kernel-mode drivers could be loaded into the operating system, there is an exception that allows drivers signed with certificates issued prior to July 29, 2015. This exception helps prevent compatibility issues with older applications, Threat actors exploited the exception by using open-source tools to alter the signing date of malicious drivers. This is a major threat due to kernel-mode drivers operating with the highest privilege level on Windows systems (Ring 0). Microsoft has revoked associated certificates and suspended the developer accounts abusing the loophole. Microsoft also emphasized that the threat actors first need to gain administrative privileges on compromised systems in order to use the drivers.
(Bleeping Computer and The Hacker News)
You should probably patch that (unless you can’t) – Patch Tuesday edition
Microsoft’s July security update contains fixes for a whopping 132 flaws, nine of which are rated Critical, and five which are being actively exploited in the wild. Two of the five zero-days are security bypass flaws requiring user interaction and affecting Microsoft Outlook (CVE-2023-35311) and Windows SmartScreen (CVE-2023-32049). Two of the other zero-days patched by Microsoft allow privilege escalation and take advantage of Windows Error Reporting (WER) service (CVE-2023-36874) and Windows MSHTM platform (CVE-2023-32046). The fifth actively exploited bug addressed is a Microsoft Outlook Security Feature Bypass Vulnerability. Microsoft also warned of a remote code execution (RCE) bug in Office and Windows HTML (CVE-2023-36884) being actively exploited by Russian threat actors via phishing campaigns. Microsoft has yet to release a fix for this bug, however, the company says Defender for Office users and those using appropriate Attack Surface Reduction Rules are protected from attachments that attempt to exploit this vulnerability. Microsoft’s July update also addresses four RCE vulnerabilities in SharePoint server (two rated “Important” – CVE-2023-33134 and CVE-2023-33159, and two “critical” – CVE-2023-33157 and CVE-2023-33160), which has recently become a popular attacker target.
Meanwhile, Adobe’s July Patch Tuesday fixes a dozen vulnerabilities in Adobe InDesign for Windows and macOS, including a critical code execution flaw and 11 bugs that cause memory leak issues. Adobe also fixed a trio of security defects in Adobe ColdFusion versions 2023, 2021 and 2018.
Siemens and Schneider Electric also got in on the bug fixing action on Tuesday, fixing a total of 50 vulnerabilities affecting their industrial control systems (ICS) products, including a critical issue in Siemens Simatic CN 4100 communication system, that can be exploited to gain admin access and take complete control of a device.
Meanwhile, VMware warned that an exploit is now available to exploit a critical security vulnerability in its Aria Operations for Logs analysis tool for cloud management (CVE-202-20864). The company issued a fix for the bug back in April.
And finally, on Monday, Apple pushed a “Rapid Security Response” update to fix a code execution flaw in Webkit browser on iOS, iPadOS, and macOS Ventura. Almost as soon as the patch went out, Apple pulled the software because it was reportedly causing problems loading certain websites. MacRumors says Apple will likely re-release the patches when the glitches have been addressed.
(Bleeping Computer and SecurityWeek [1][2][3] and Dark Reading and Krebs on Security)
British teens accused of masterminding hacks on Uber and Rock Star Games
Two UK teenagers were accused of being key members of the notorious Lapsus$ hacking group and involved in attacks on companies including Nvidia, Rockstar Games, and Uber. Arion Kurtaj, 18, and an unnamed 17-year-old male were charged with computer misuse, blackmail and fraud. Kurtaj allegedly posed as a contractor at Rockstar to steal code for the latest installment of the Grand Theft Auto, and leaked it on hacking forums while soliciting a ransom payment. Prosecutors said police connected the hacks to the teenagers through IP addresses linked to devices and online accounts that the teens used to boast about the hacks. The 17-year-old pleaded guilty to two hacking charges while Kurtaj was found medically unfit to stand trial and therefore a jury will only decide whether he is liable for the alleged crimes, rather than guilty of them.
Russian naval officer killed near home may have been tracked on fitness app
Stanislav Rzhitsky, a former Russian submarine captain was shot dead by an unidentified assailant while jogging in the Russian city of Krasnodar on Monday. An online Russian publication reported that Rzhitsky maintained a public account on a fitness app called Strava that showed him taking the same route on his morning runs and that information may have allowed the assassin to track him. The fitness-tracking app has repeatedly raised concerns among security experts including reportedly being used to identify secret military bases.