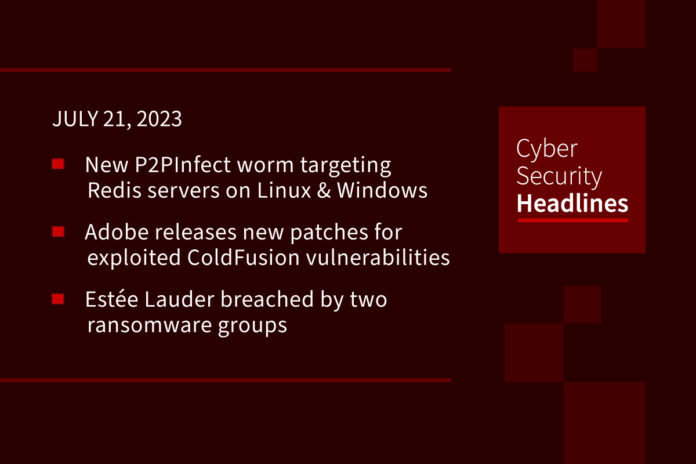
New P2PInfect worm targeting Redis servers on Linux and Windows systems
A new cloud targeting, peer-to-peer (P2P) worm called P2PInfect is targeting vulnerable Redis instances for follow-on exploitation. According to Palo Alto Networks Unit 42 researchers William Gamazo and Nathaniel Quist, “P2PInfect exploits Redis servers running on both Linux and Windows Operating Systems making it more scalable and potent than other worms.” They added, “the worm is also written in Rust, a highly scalable and cloud-friendly programming language.” It’s estimated that as many as 934 unique Redis systems may be vulnerable to the threat, which first became known on July 11, 2023.
ColdFusion confusion: Adobe releases new patches for exploited vulnerabilities
Following up on yesterday’s story about Adobe’s incomplete ColdFusion patches, the company has announced another ColdFusion update to patch three new CVEs. One of these latest, CVE-2023-38205, is the bypass for CVE-2023-29298, which had been exploited and chained with what appeared to be CVE-2023-38203 The software giant warned in its advisory that 38205 has been “exploited in the wild in limited attacks.” One of the problems with this patch issue appears to be some genuine confusion as a result of the similarities in the CVE labels.
Estée Lauder breached by two ransomware groups
Information belonging to the world-renowned cosmetics company was posted to the leak sites of Alphv/BlackCat and Clop, according to security researchers on Twitter. Headquartered in New York, Estée Lauder’s brands include Jo Malone, Tommy Hilfiger, DKNY, and Aveda. It has warned that the incident would cause disruption to its business. The company has not publicly connected this hack to MOVEit Transfer.
Old Roblox data leak resurfaces, 4000 users’ personal information exposed
Troy Hunt, founder of the website ‘Have I Been Pwned,’ tweeted on July 18 about a potential leak impacting attendees of the 2017-2020 Roblox Developers Conferences. Roblox_RTC reported on the leak the following day. The leaked list contained 4000 unique email addresses, alongside standard PII. “A source close to Troy Hunt states that the leak was recently re-published on a public hacking forum, and that high-profile users have started receiving malicious calls, texts and emails due to the leak.”
Thanks to this week’s episode sponsor, OpenVPN

Ofcom says it won’t pay MOVEit ransom
The U.K. government’s communications regulator Ofcom, one of now 400 organizations known to be impacted by the MOVEit incident, states that it “has not made any payment, as per advice from the National Cyber Security Centre.” Though it is believed that personal data of 412 employees was downloaded during the attack, they reiterate that “no payroll data was breached.” said the spokesperson. While Clop had listed both Ofcom and ComReg, the general communications regulator for Ireland, both organizations have since been removed from the leak site. The reason behind the removal is not known, but Clop “claims it deletes government-related data that it steals.”
China-linked hackers target mobile devices with WyrmSpy and DragonEgg spyware
The Chinese hacking group APT41 has been using these two newly-identified spyware strains to infect Android devices. The security firm Lookout says it has found links between the group and two Android spyware strains that it calls WyrmSpy and DragonEgg. “Lookout said the sophisticated spyware could be used to collect camera photos, device location, SMS messages, audio recordings and contacts.” The Record stated, “WyrmSpy pretends to be a default operating system app used for displaying notifications to the user, while DragonEgg disguises itself as a third-party keyboard and messaging app like Telegram.”
Tech support scammers trick victims into old-school offline money transfer
According to Graham Cluley, writing in Tripwire’s Fortra magazine, a new twist on the tech support scam that often involves mistaken deposits of cash into a victim’s bank account with a request for it to be returned, now sees these fraudsters increasingly telling their victims to send actual cash, concealed in a newspaper or a magazine, via a shipping company, in place of gift cards, money transfer apps or even cryptocurrencies. Cluley suggests this switch to analog payments might be related to action taken by the FTC against payments firm Nexway, which has been accused of knowingly processing fraudulent credit card payments on behalf of tech support scammers. Cluley adds that although most cybersecurity pros would not fall for such a scam, a recent study from Microsoft shows that GenZers and Millennials are just as prone to losing money to scammers as are their elders.
(Tripwire)
Famed hacker Kevin Mitnick dead at 59
Kevin Mitnick, a hacker who served time in prison for computer and communications-related crimes, has died after a battle with pancreatic cancer, at the age of 59. According to Security Week, “at the time of his death, Mitnick was working as security evangelist and ‘Chief Hacking Officer’ at KnowBe4, a security awareness training company based in Florida. Mitnick gained global fame in the mid 1990s when he was arrested by the FBI on computer hacking and wire fraud charges. He was sentenced to prison time after a plea deal and would later write books and pursue celebrity as the so-called ‘world’s most famous hacker ever.’”