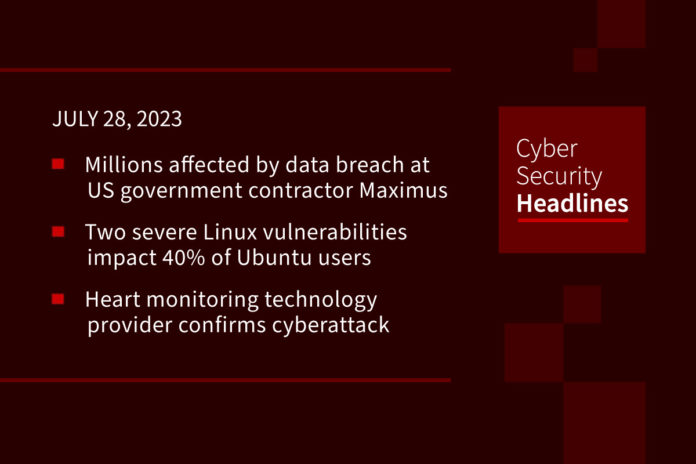
Millions affected by data breach at US government contractor Maximus
Maximus, a provider of services to the U.S. government has revealed that hackers stole the personal data of between 8 million and 11 million people during the recent MOVEit Transfer data-theft attacks. Maximus manages and administers US government-sponsored programs including federal and local healthcare programs and student loan servicing. The company also has a presence in the U.S., Canada, Australia, and the United Kingdom. Maximus has found no evidence that the hackers moved beyond the MOVEit environment, which had been immediately isolated from the rest of the network. The Clop ransomware gang has already added Maximus to its data leak site, part of a collection of 70 new MOVEit zero-day victims.
Two severe Linux vulnerabilities impact 40% of Ubuntu users
Cybersecurity researchers at Wiz have disclosed two high-severity security flaws in the Ubuntu kernel that could facilitate local privilege escalation attacks, and which have the potential to impact 40% of Ubuntu users. The vulnerabilities – tracked as CVE-2023-32629 and 2023-2640 and dubbed GameOver(lay) – exist in a module called OverlayFS and result from inadequate permissions checks, enabling a local attacker to gain elevated privileges. Wiz security researchers Sagi Tzadik and Shir Tamari said, “the impacted Ubuntu versions are prevalent in the cloud as they serve as the default operating systems for multiple [cloud service providers].”
Heart monitoring technology provider confirms cyberattack
The website for Canadian technology company CardioComm Solutions went down on Wednesday and remained down on Thursday, following confirmation that it was responding to a cyberattack on its systems. CardioComm provides heart monitoring and medical electrocardiograms products. CardioComm notes on a temporary webpage that all of its online services were down as it worked to resolve the issue, and provided a phone number for those in need. Representatives for the company did not respond to requests from The Record for comment about whether it was a ransomware attack, but did say, “there is no evidence that customers’ health information was compromised as a result of this attack since CardioComm’s software is designed to run on each client’s own server environments.”
China accuses U.S. of hacking earthquake monitoring equipment
According to The Record, “China’s state-controlled newspaper The Global Times reported on Wednesday that ‘hacker groups and lawbreakers with governmental backgrounds’ from the United States were suspected of compromising network equipment at an earthquake monitoring station in Wuhan.” The Global Times continued, by suggesting that “this Trojan horse program could illegally control and steal seismic intensity data collected by the front-end stations, posing a serious threat to national security.” The newspaper apparently cited unnamed security experts who suggested the data was relevant when constructing military defense facilities.
Thanks to this week’s episode sponsor, AppOmni

UK ambulance services in UK lost access to patient records after cyberattack
Two British ambulance services have found themselves unable to access electronic patient records after a cyberattack that hit their software provider Ortivus, which is software company based in Sweden specializing in providing solutions for the healthcare and medical industry. including technology for electronic patient record systems and related medical data management applications. The attack took place on the evening of July 18 and impacted UK customer systems within its hosted datacenter environment. Ortivus stated they have no evidence that threat actors stole customers’ data.
New malvertising campaign distributing trojanized IT Tools via Google and Bing search ads
A new malvertising campaign is using ads on Google Search and Bing to attract people looking for IT tools like AnyDesk, Cisco AnyConnect VPN, and WinSCP. Their goal is to trick victims into downloading trojanized installers. According to Sophos, this product, dubbed Nitrogen, is designed to deploy second-stage attack tools such as Cobalt Strike. “Throughout the infection chain, the threat actors use uncommon export forwarding and DLL preloading techniques to mask their malicious activity and hinder analysis,” the Sophos researchers stated.
Swiss visa appointments canceled in UK due to ‘IT incident’
As of yesterday, all appointments for people in the UK looking to obtain tourist and transit visas to Switzerland have been canceled. “TLSContact, Switzerland’s chosen outsourced provider of visa and consular services is blaming ‘an IT incident’ at its London, Manchester, and Edinburgh centers for the cancellations.” TLScontact provides visa processing and IT services to several governments with 150 visa application centers and a presence across 90 countries.
Australian Medical Association calls for stronger AI regulations after doctors use ChatGPT to write medical notes
Australia’s medical association has called for stronger rules and transparency around the use of artificial intelligence in the healthcare industry. This follows a warning sent to physicians in five hospitals in the city of Perth, urging them not to write medical notes or records using ChatGPT. “The ABC reported that in an email to staff, the service’s CEO Paul Forden said there was no assurance of patient confidentiality using such systems, and it must stop…and that AI protections should include ensuring that clinicians make the final decisions, and that there is informed consent by the patient for any treatment or diagnostic undertaken using AI.”