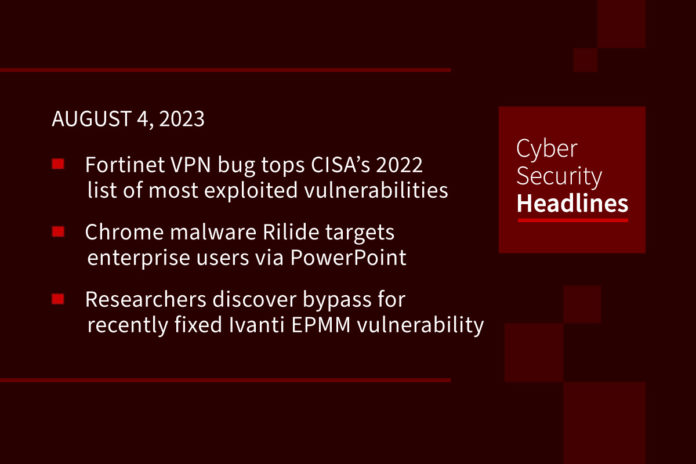
Fortinet VPN bug tops CISA’s list of most exploited vulnerabilities in 2022
The most exploited vulnerability of last year was actually disclosed back in 2018 – Fortinet’s SSL VPNs and is tracked as CVE-2018-13379. Next on the list is the chain of vulnerabilities affecting Microsoft Exchange servers, popularly known as ProxyShell. This is followed by the Atlassian bug, the issues affecting VMware products, F5’s BIG-IP products, Log4Shell, the Zoho vulnerability, and Microsoft’s Support Diagnostic Tool in Windows.
Chrome malware Rilide targets enterprise users via PowerPoint guides
The new version of Rilide, a malicious browser extension for browsers such as including Chrome, Edge, Brave, and Opera, can overcome restrictions introduced by Google’s new extension specifications, by adding code obfuscation to evade detection. In this campaign, Trustwave Spiderlabs discovered a number of creative campaigns including a PowerPoint presentation that pretends to be a security warning, guiding users into installing the extension. This presentation includes slides that “warn that threat actors are impersonating GlobalProtect to distribute malware and provides steps that the user should follow the steps in the guide to install the correct software.”
Researchers discover bypass for recently fixed Ivanti EPMM vulnerability
Following up on a story we brought you yesterday regarding the Zero-Day that hit the Norwegian government, in Ivanti Endpoint Manager Mobile ID’d as CVE-2023-35078, Rapid7 cybersecurity researchers have discovered a bypass for that recently patched actively exploited vulnerability. This new one CVE-2023-35082 (CVSS score: 10.0), “can be exploited by unauthenticated attackers to access the API in older unsupported versions of MobileIron Core (11.2 and below).” Ivanti addressed the vulnerability with the release of the MobileIron Core 11.3 version. The CVE-2023-35082 flaw is the third issue addressed by Ivanti impacting its EPMM product, but there is currently no evidence of active exploitation.
Salesforce email service zero-day exploited in phishing campaign
According to security company Guardio, threat actors are exploiting a Salesforce zero-day vulnerability and abusing Meta features in a phishing campaign that uses victims’ real names, appear to come from Meta Platforms, and were sent from an @salesforce.com address. The email led users to a legitimate Facebook domain, apps.facebook.com, where they were “informed about violating Facebook’s terms of service. When users clicked on a button to resolve the issue, they were taken to a phishing page that instructed them to provide their information.” Guardio’s analysis states that the attackers had “targeted the Email Gateway component in the Salesforce CRM, specifically an ‘Email-To-Case’ feature designed to convert customer inbound emails into actionable tickets in Salesforce.”
Thanks to this week’s episode sponsor, Opal

OWASP publishes Top 10 for LLM (Large Language Model) applications
This list identifies the top 10 most critical vulnerabilities impacting LLM applications, and aims to highlight the security issues involved when deploying Large Language Models (LLMs). The Top Ten is the result of the work of nearly 500 AI researchers, developers, industry leaders, and academics. The top three on this list are Prompt Injection – the use of inputs that cause unintended actions by the LLM, Insecure Output Handling, in which LLM output is accepted without scrutiny, exposing backend systems, and Training Data Poisoning, which occurs when LLM training data is tampered with. The full list is available at OWASP, and a link is available in the show notes to this episode.
(Security Affairs and OWASP)
Piles of unpatched IoT, OT devices attract ICS cyberattacks
Research from Nozomi Networks, analyzing public IoT/OT cyber incidents over the past six months have found that threat actors such as ransomware and DDoS cyber attackers have been busy attacking ICS systems this year, especially in manufacturing, water treatment, food and agriculture, and the chemical sectors. “Nozomi measured an average of 813 unique cyberattacks daily on its honeypots the first six months of this year, hitting a peak of 1,342 on May 1.” Melissa Bischoping, endpoint security researcher with Tanium suggests three key reasons for the delay: the need for stability and uptime of these systems, the cost of upgrading ICS systems, and incompatibility between new upgrades and older systems.
Microsoft says Russia-linked hackers behind dozens of Teams phishing attacks
A Russian government-linked hacking group called Midnight Blizzard or APT29 has been identified as behind a campaign to steal login credentials by engaging users in Microsoft Teams chats pretending to be from technical support. This according to Microsoft researchers on Wednesday. The hackers used already-compromised Microsoft 365 accounts owned by small businesses to make new domains that appeared to be technical support entities and had the word “microsoft” in them. They made themselves out to resemble technical support and tried to engage Teams users in chats and get them to approve multifactor authentication (MFA) prompts, the researchers said.
(Reuters)
Manufacturing sector reeling from financial costs of ransomware
Analysis company Comparitech estimates that manufacturers around the world have lost an estimated $46.2bn to downtime from ransomware attacks over the five and half year period. They point out this could be an underestimate, since downtime in manufacturing has knock on effects in areas such as sales. Their research showed that average downtime caused by ransomware nearly doubled from 2021 to 2022, rising from 6.4 to 12.2 days. “Rebecca Moody, head of data research at Comparitech, told Infosecurity that a likely factor for the increasing downtime is attackers ‘evolving their malware to stay one step ahead’ of organizations.”