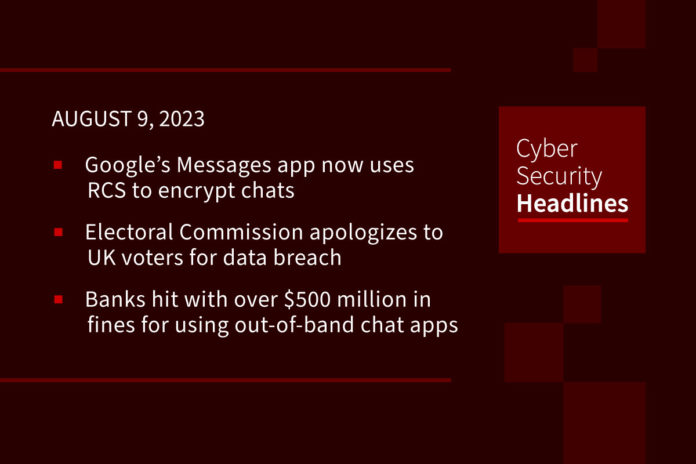
Google’s Messages app now uses RCS to encrypt chats
On Tuesday, Google announced that its Messages app is now more secure and robust with Rich Communication Services (RCS), a protocol that replaces SMS and encrypts individual and group chat messages end-to-end. RCS will be enabled for new and existing users, allowing them to share high-res photos and videos, see typing indicators, get read receipts, and rename, edit and remove themselves from group chats. With the updates, Google says all conversations between Messages users, whether 1:1 or group chats, will now be kept private.
Electoral Commission apologizes for security breach involving UK voters’ data
Confidence in the UK’s Electoral Commission may have dwindled after it was revealed that a cyber-attack that compromised data of 40 million voters went undetected for a year. The attack was discovered last October and reported to the Information Commissioner’s Office (ICO) within 72 hours. However the regulator did not notify the public for another 10 months. The Electoral Commission apologized for the security breach that exposed full copies of electoral registers, including names and addresses of all voters registered between 2014 and 2022. Data of overseas voters and anonymous voters whose details are private for safety reasons were not accessible to the intruders.
Banks hit with over $500 million in fines for using out-of-band chat apps
On Tuesday, US regulators announced a combined $549 million in penalties against Wells Fargo and a raft of smaller or non-US firms that failed to maintain electronic records of employee communications. The Securities and Exchange Commission (SEC) issued fines totaling $289 million against 11 firms they say admitted using side channels like WhatsApp to discuss company business dating back to 2019, therefore violating federal securities laws by failing to preserve records. The Commodity Futures Trading Commission doled out an additional $260 million worth fines to four banks for similar records violations. These actions follow similar settlements totaling more than $2 billion with bigger players including JPMorgan Chase, Goldman Sachs, Morgan Stanley and Citigroup.
(NBC News)
Malicious extensions can abuse Visual Studio flaw to steal auth tokens
Researchers have discovered a flaw in Microsoft’s Visual Studio Code (VS Code) editor and development environment that allows malicious extensions to retrieve authentication tokens stored in Windows, Linux, and macOS. These tokens are used for integrating with various third-party services and APIs, such as GitHub, and other coding platforms. The issue stems from a lack of isolation of authentication tokens in VS Code’s ‘Secret Storage’ API. The researchers were able to decrypt the tokens using a key they could easily derive using the executable path and the machine ID. Using a second flaw in the ‘getFullKey’ function, researchers were able to trick VS Code into granting them access to secure tokens from other extensions. Researchers reported the flaw and a working proof-of-concept (PoC) to Microsoft two months ago, however, Microsoft has yet to address the issue.
Thanks to our sponsor, Conveyor

It’s Conveyor’s GPT-powered security questionnaire response tool: the most accurate questionnaire automation tool on the market. It’s so good, you can let your customers upload their own questions in your trust portal to get instant answers based on your content. And of course, it’s not just for your customers. You can use the GPT-questionnaire response tool internally as well to get auto-generated precise answers to entire questionnaires in minutes so all you have to do is review.
Maybe it’s time to replace your outdated RFP software… Try a free proof of concept with your own data. Learn more at www.conveyor.com
Google is picking up the pace of Chrome security updates
Google will begin issuing Chrome security updates on a weekly basis to accompany the “milestone” Chrome releases that come every four weeks in its stable channel. Google’s weekly updates, which it used to issue biweekly, will help close the “patch gap” between fixes appearing in Canary / Beta releases and then being rolled out to its stable channel. This reduces the time threat actors have to develop exploits based on beta fixes to try and exploit billions of potentially vulnerable stable channel users. Google says the new weekly updates will start with Chrome 116.
You should probably patch that (Patch Tuesday edition)
Microsoft’s August 2023 Patch Tuesday update includes fixes for 74 vulnerabilities, including two that attackers are actively exploiting in the wild. Microsoft fixes address six Critical bugs and 67 flaws it classified as Important across an array of Microsoft products. The first zero-day (CVE-2023-38180) is a denial-of-service issue assigned a CVSS score of 7.5. The flaw affects multiple versions of .Net and Visual Studio and which attackers can exploit using low complexity attacks. Microsoft has now also released a patch for a remote code execution (RCE) bug in Microsoft Office 2013, 2016, and 2019 (CVE-2023-36884) under active exploit in the wild. Microsoft initially disclosed the bug in July but only offered mitigation advice at that time.
Additionally, Adobe rolled out a batch of 30 security updates for its Acrobat and Reader software, affecting Windows and macOS installations. The software maker documented the security defects in a critical-level advisory and warned that successful exploitation could lead to arbitrary code execution, memory leaks, security feature bypass and application denial-of-service attacks.
(Dark Reading and Bleeping Computer and SecurityWeek [1][2])
75% of organizations set to ban generative AI
According to results of a global survey released by BlackBerry Limited on Tuesday, 75% of organizations worldwide are currently implementing or considering bans on ChatGPT and other Generative AI applications. 61% of those respondents said the measures are intended as long term or permanent, pointing to risks to data security, privacy, and corporate reputation as driving their decisions. Despite their inclination towards outright bans, the majority also recognize the opportunity for Generative AI apps to increase efficiency (55%) and innovation (52%), and enhance creativity (51%). When it comes to using Generative AI tools for cybersecurity defense, the majority of respondents (81%) remained in favor, suggesting that IT decision makers don’t want to be caught flat-footed and give cyber criminals the upper hand.
New Downfall CPU attacks steal sensitive data
Google researcher Daniel Moghimi has devised new CPU attacks to exploit a side-channel vulnerability, dubbed “Downfall,” that affects multiple Intel microprocessor families (Skylake through Ice Lake). Moghimi was able to exploit the flaw (CVE-2022-40982) to steal AES 128-bit and 256-bit cryptographic keys and other sensitive info protected by Intel’s hardware-based memory encryption mechanism called Software Guard eXtensions (SGX). Downfall attacks require an attacker to be on the same physical processor core as the victim, however, locally-installed malware could also potentially exploit the flaw. Details about the vuln were kept private for almost a year to allow original equipment manufacturers (OEMs) and communication service providers (CSPs) time to develop a microcode update which is now available to mitigate the issue. However, fully eliminating the risk of Downfall attacks requires a complete hardware redesign. Intel downplayed the issue saying that, “trying to exploit this outside of a controlled lab environment would be a complex undertaking.” Moghimi has released exploit details and is scheduled to discuss it this week at the Black Hat security conference.