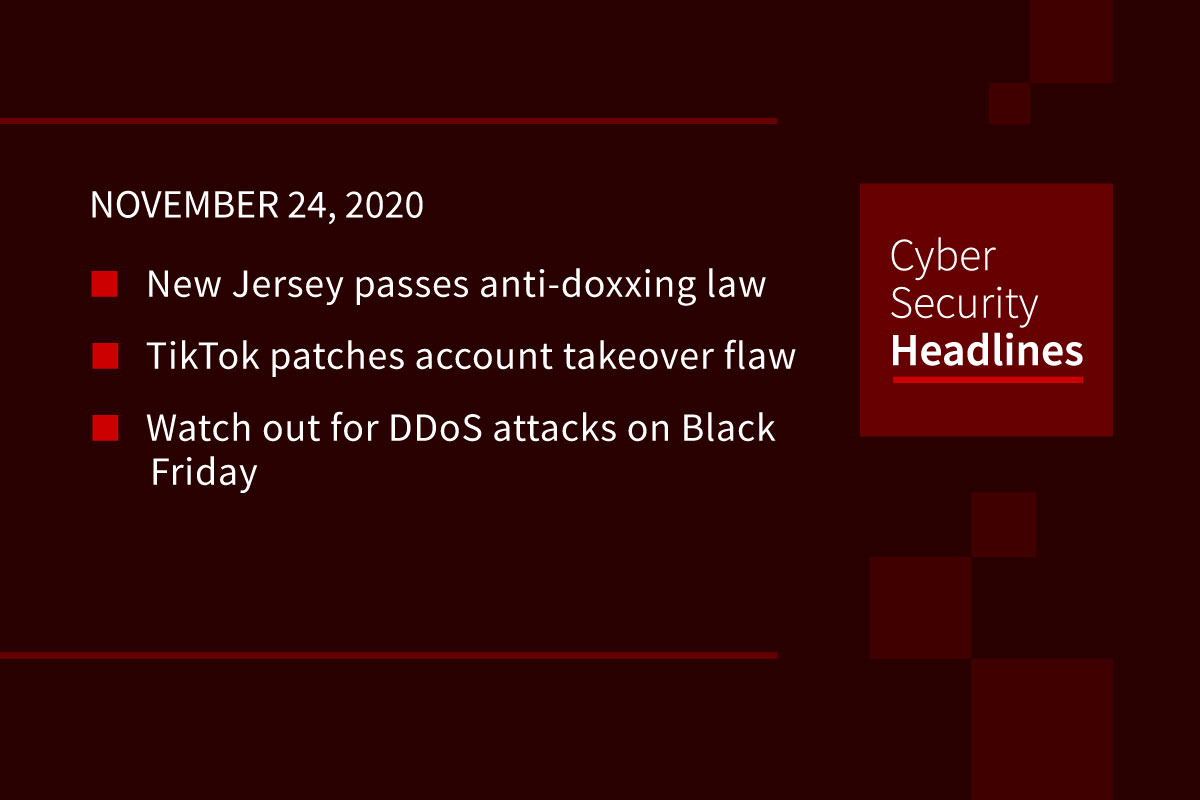
New Jersey passes anti-doxxing law
Governor Phil Murphy signed Daniel’s Law into effect, barring the publication of home addresses and unlisted phone numbers for judges, prosecutors and law enforcement officers. The law also requires anyone posting it or platforms hosting the information to remove it within 72 hours of written notice from a potential target. New Jersey Senator Bob Menendez said he was committed to passing a similar federal-level bill.
(Engadget)
TikTok patches account takeover flaw
The cross-site scripting security flaw was reported on HackerOne by security researcher Muhammed Taskiran, who initially found that a URL parameter on the tiktok.com domain which was not properly sanitized.This could be exploited to eventually execute malicious code in a user’s browser session. Taskiran used a JavaScript payload to combine this with a separate endpoint Cross-Site Request Forgery attack, that let him set a new password on accounts which had used third-party apps to sign-up, resulting in a one-click account takeover attack. Submitted as part of TikTok’s bug bounty program, the flaws were fixed by September 18th.
(ZDNet)
Watch out of DDoS on Black Friday
Dawn Blizard at Security Intelligence makes the case that this holiday online shopping season might have some unique security challenges. Cyberattacks, and DDoS attacks specifically, usually spike during the Black Friday shopping weekend. However Kaspersky Labs has shown that 2020 is already seeing spikes in DDoS activity in Q1 and Q2, with increases in attack size, frequency and duration, with record breaking bytes-per-second intensity. Combined with an estimated 35% increase in e-commerce this year driven by the COVID-19 pandemic, it could make for a particularly turbulent cybersecurity landscape during the shopping holiday.
Chrome for Windows 7 gets a stay of security execution
Google announced that the browser will get support on Windows 7 through January 2022. Originally security updates were scheduled to stop in July 2021. Google cited that while the COVID-19 pandemic accelerated many IT initiatives around remote work, others, like migrating from a legacy OS like Windows 7, have taken a backseat. Windows 7 reached the end of extended support back in January, but Google found that in Q2, 22% of organizations were either still migrating or only planning to start migrating to Windows 10.
(TechSpot)
Thanks to our sponsor, Dtex

Australia issues report on contact tracing app security
The Office of the Australian Information Commissioner issued its first six-month report regarding security and privacy concerns surrounding the country’s COVIDSafe contact tracing app. Overall the app saw no data breaches or complaints, with only 11 inquiries about the app, with concerns about the legal basis of the app, the number of downloads of the app, and whether a job or organization could require use of the app. There are currently four assessments related to the access controls for stored data underway. According to Australia’s security agencies in the report, “there is no evidence that any agency within IGIS jurisdiction has decrypted, accessed or used any COVID app data.”
(ZDNet)
Bluetooth hack opens the door for Tesla Model X
Lennert Wouters, a security researcher at Belgian university KU Leuven published details about the vulnerability, which combines flaws in the Model X and its keyless entry fob. Using an mobile $300 hardware kit and the car’s ID number visible through the windshield, Wouters was able to extract a radio code that unlocks the car. A separate code-signing vulnerability would let an attacker pair a different key fob to the car, as key fob updates don’t cryptographically verify their authenticity, opening the door to using rewritten firmware. The researcher advised Tesla on the vulnerability in August, and the company plans to roll out a software update to the fobs later this week, although a patch for the cars may take up to a month to roll out.
(Wired)
Spotify sees a rash of credential stuffing attacks
It’s no secret that reusing passwords is a security nightmare. Some Spotify users are discovering this as the music streaming service appears to have been hit with a credential stuffing attack. Researchers at vpnMentor found an unencrypted Elasticsearch database online with over 380 million individual records, including login credentials, that attackers were actively validating against Spotify accounts (here’s the report). The attack seems to have impacted up to 350,000 users, and Spotify has initiated some password resets to mitigate the damage. The researchers recommend however that subscribers who use those passwords on other services should immediately change those passwords as well.
Google spots a high severity GitHub flaw
Google Project Zero researcher Felix Wilhelm identified a bug in GitHub’s Actions feature that was “highly vulnerable to injection attacks,” back in August. The vulnerability centered around the “set-dev” and “add-path” commands, which are used to define arbitrary environment variables as part of a workflow step, parsing every line looking for workflow commands, but ultimately open to executing untrusted content. After the typical 90 day window to patch the vulnerability, GitHub requested an additional 48 hours to contact customers about the flaw, but didn’t have a fix. Ultimately Google published details of the flaw 108 days after discovery. After disabling the commands per Whilhelm’s suggestion two weeks ago, GitHub issued a full fix on November 16th.
(ZDNet)