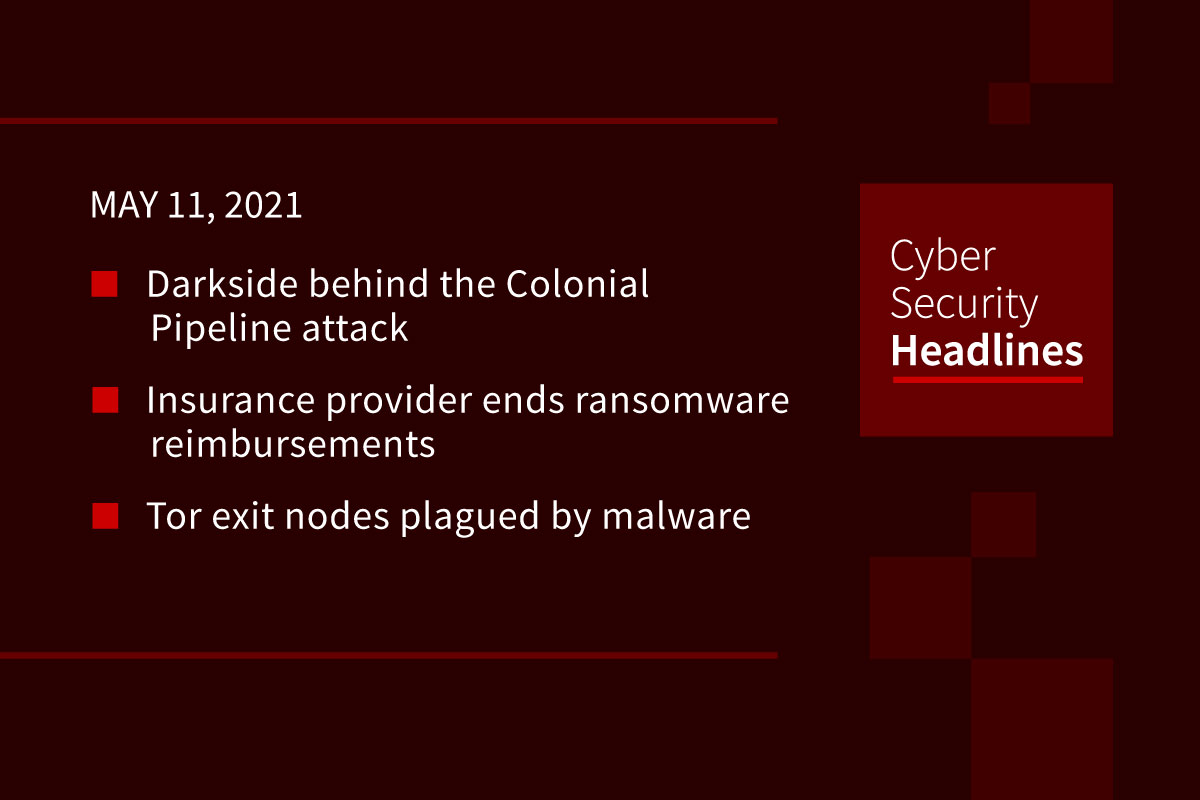
Darkside behind the Colonial Pipeline attack
The US Federal Bureau of Investigation confirmed that the ransomware organization Darkside was behind the attack on the Colonial Pipeline. The group posted a statement Monday that said it was not tied to governments and that “Our goal is to make money, and not creating problems for society.” However it did not mention the Colonial Pipeline attack directly. Colonial said its working on restoring service in a phased approach, “substantially restoring operational service by the end of the week.”
(WSJ)
Insurance provider ends ransomware reimbursement
The insurance company AXA said, at the request of the French government, it will end cyber insurance policies in France that reimburse victims for ransomware payments, although policies will still cover the cost of recovery. Speaking at a recent Paris roundtable, French cybercrime prosecutor Johanna Brousse said in 2020, only the US experienced more ransomware attacks than France. A September report by another cyber insurance provider, Coalition, found that 41% of claims were ransomware related in the first half of 2020, with a 260% increase in ransomware attacks on the year.
(ZDNet)
Tor exit nodes plagued by malware
For more than 16 months, a threat actor has been adding malicious servers to perform SSL stripping attacks against cryptocurrency sites on the Tor network. It is believed this was done to replace cryptocurrency addresses with those owned by the attacker once the traffic was in HTTP plaintext. The servers flooded the Tor network on three occasions, at its peak in mid-May 2020 accounting for 23% of the entire Tor network’s exit capacity, before being largely shutdown by the Tor team. These attacks began in January 2020, and exposed by the security researcher known as Nusenu in August, but new research shows that the attacks are still ongoing. Nusenu estimates the attacker’s malicious infrastructure currently represents 4-6% of Tor node exit capacity.
AirTags get hacked
German security researcher Thomas Roth claims to have modified the firmware on an Apple Airtag by re-flashing the device’s microcontroller. This let Roth change the URL for Lost Mode to his personal website, which ordinarily routes to a Find My web address. Roth bricked two AirTags in the process of developing the exploit. It’s unclear if the exploit could be achieved in the wild.
Thanks to our episode sponsor, Altitude Networks

Amazon report outlines steps against counterfeit goods
Amazon released its Brand Protection Report, outlining its efforts against fake products. In 2020, the company blocked 10 billion suspect product listings before being published, prevented 6 million attempts to create seller accounts suspected of counterfeit operations, and seized 2 million counterfeit goods from its warehouses. Overall the company said less than 0.01% of products sold had a counterfeit claim submitted by a customer. The company invested $700 million to combat counterfeit products on its platform in 2020.
(ZDNet)
New tool from Trend Micro hopes to improve open source security
We’ve previously covered on this show the increasing awareness of the vulnerability of open source software to things like supply chain attacks. A new solution from Trend Micro seeks to resolve this anxiety. It’s Trend Micro Cloud One – Open Source Security by Snyk SaaS offering hopes to automate scanning for open source security issues, letting devs input code and providing a series of dashboards with visualizations that track issues over time, and potential open source license issues, with an overall security severity score. This is Trend Micro’s first third-party integration with its Cloud One platform.
Office blocking Google and LinkedIn emails
Microsoft acknowledged the issue with Office 365 blocking and quarantining emails from multiple domains as malicious. This is resulting in legitimate emails appearing in Exchange Online Protection & Defender for Office 365. Microsoft said this was an inadvertent block, and fixed the issue for the domains on emails going forward. The company is working on a way to automatically release previously received emails on impacted domains.
Scam websites expand in UK during the pandemic
The U.K.’s National Cyber Security Centre took down 15-times more malicious websites in 2020 than it did the year before, removing 700,595. In a report, the agency also documents that these websites shifted increasingly to phishing, often presenting themselves as representing the UK government as tax or health authorities. The U.S. domain host NameCheap hosted roughly a third of these types of sites, with a median takedown time of over 60 hours. 46% of celebrity endorsement scams were hosted on AWS, with median takedown times of 19 hours.