Here’s a quick six-minute video full of highlights from “Hacking Cloud Access: An hour of critical thinking about how managing permissions is complicating our ability to secure our environment.”
Our guests from this discussion were:
- Mike Raggo (@mikeraggo), cloud security expert, CloudKnox
- Richard Rushing (@SecRich), CISO, Motorola Mobility.
Got feedback? Join the conversation on LinkedIn.
HUGE thanks to our sponsor CloudKnox

Best Bad Ideas
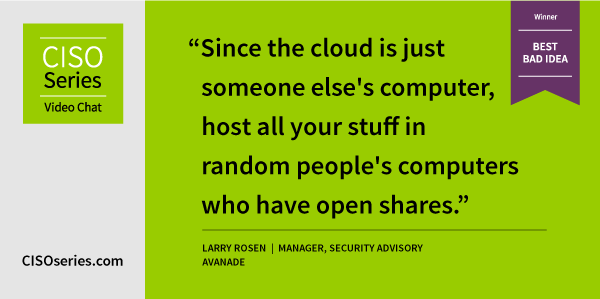
Congrats to Larry Rosen, manager, security advisory, Avanade for submitting this week’s winner for the Best Bad Idea!
Other honorable mentions go to:
“Embrace Chaos Engineering concepts to implement Chaos-Based Access Control (CBAC) instead of RBAC or ABAC” – Kevin Hakanson, sr. solutions architect, AWS
“Put your data in every cloud you can purchase to ensure redundancy and use the same password for all of them.” – Neil Saltman, senior account executive, Anomali
“Use AWS as your cloud provider and hire GCP engineers to run it.” – Joshua Scott, head of information security & IT, Postman
“No Cloud Security Thursdays! No Cloud Security activities allowed!” – Bryan William Solari, regional sales manager, west, AppOmni
“Monthly remove all access and make everyone ask for it again as the need arises.” – Patrick Benoit, VP, global cyber GRC, BISO, CBRE
“Hire a consulting firm to manage your MSSP that’s managing your cloud access.” – Joshua Scott, head of information security & IT, Postman
Best Strategies
“Never trust one set of eyes to create access. Perform regular reviews.” – Kevin Kentner, program manager, CrowdStrike
“Befriend accounting. They can let you know if there are any cloud payments on company cards, expense reimbursements, and what invoices are being paid. This can help identify rogue cloud instances that are not in IT / Security’s control.” – Brian Colt, information security engineer, DASH Financial Technologies
“Have new hires walk through current documentation while in training. Have them update areas that have changed to help keep documentation more up- to- date.” – Kim Kenendy, enterprise security specialist, AttackIQ
Quotes from the chatroom
“You really need to nail GRC policies and enforcement then IAM as phase 1 for the 3 major CSPs” – Dutch Schwartz, principal security specialist, AWS
“Implementing automation requires front end effort but should reduce long term effort. You should, over time, move from task management to tuning and monitoring systems to ensure they’re providing the right outcomes.” – Bryan William Solari, regional sales manager, west, AppOmni
“One of the biggest errors is thinking ‘this is someone else’s computer.’ That’s hilarious as a sticker on your laptop, but misses the value of cloud scale, flexibility, and automation.” -Dutch Schwartz, principal security specialist, AWS
“My opinion: your goal with automation should be to improve a process and have better controls (i.e. make me better at my job) – automation can reduce headcount, but if that’s your goal then you’re doing it wrong.” – Brandon Pelfrey, business development, PlexTrac





