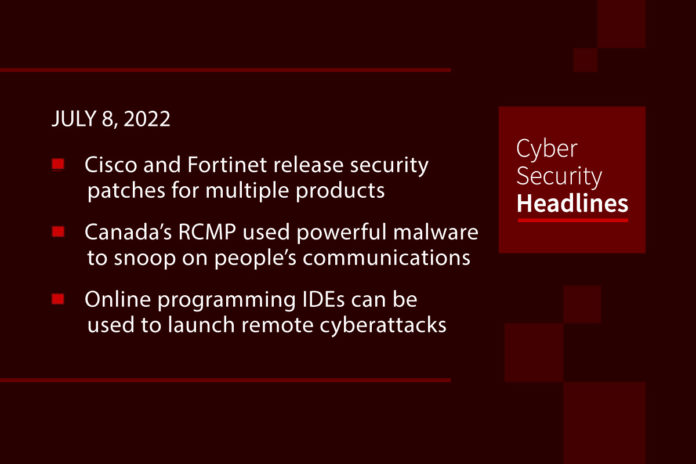
Cisco and Fortinet release security patches for multiple products
Cisco on Wednesday rolled out patches for 10 security flaws spanning multiple products, one of which is rated a critical 9.0 in severity and could be weaponized to conduct absolute path traversal attacks. The issues, tracked as CVE-2022-20812 and CVE-2022-20813, affect Cisco Expressway Series and Cisco TelePresence Video Communication Server (VCS) and “could allow a remote attacker to overwrite arbitrary files or conduct null byte poisoning attacks on an affected device,” the company said in an advisory. In a related development, Fortinet addressed as many as four high-severity vulnerabilities affecting FortiAnalyzer, FortiClient, FortiDeceptor, and FortiNAC, which, if successfully exploited, may allow an authenticated attacker to execute arbitrary code, retrieve and delete files, and access MySQL databases, or even permit a local unprivileged actor to escalate to SYSTEM permissions.
Canada’s RCMP have been using powerful malware to snoop on people’s communications
Canada’s national police force has described for the first time how it uses spyware to infiltrate mobile devices and collect data, including by remotely turning on the camera and microphone of a suspect’s phone or laptop. The Royal Canadian Mounted Police says it only uses such tools in the most serious cases, when less intrusive techniques are unsuccessful. But until now, the force has not been open about its ability to employ malware to hack phones and other devices, despite using the tools for several years. Between 2018 and 2020, the RCMP said it deployed this technology in 10 investigations. In the document, the police force says it needs to use spyware because traditional wiretaps are much less effective than they once were.
(Politico)
Online programming IDEs can be used to launch remote cyberattacks
Security researchers are warning that hackers can abuse online programming learning platforms to remotely launch cyberattacks, steal data, and scan for vulnerable devices, simply by using a web browser. At least one such platform, known as DataCamp, allows threat actors to compile malicious tools, host or distribute malware, and connect to external services. DataCamp provides integrated development environments (IDEs) to close to 10 million users that want to learn data science using various programming languages and technologies (R, Python, Shell, Excel, Git, SQL). The IDE also allows users to import Python libraries, download and compile repositories, and then execute compiled programs. In other words, anything an industrious threat actor needs to launch a remote attack directly from within the DataCamp platform.
QNAP warns of new Checkmate ransomware targeting NAS devices
Network-attached storage (NAS) vendor QNAP warned customers to secure their devices against attacks using Checkmate ransomware to encrypt data. QNAP says the attacks are focused on Internet-exposed QNAP devices with the SMB service enabled and accounts with weak passwords that can easily be cracked in brute-force attacks. “Preliminary investigation indicates that Checkmate attacks via SMB services exposed to the internet, and employs a dictionary attack to break accounts with weak passwords.” Checkmate is a recently discovered ransomware strain, first deployed in attacks around May 28.
Thanks to today’s episode sponsor, Votiro

North Korean hackers taking aim at health care with Maui ransomware
The FBI, the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency, and the Treasury Department said in an alert that the hackers were using a kind of ransomware dubbed “Maui” to go after health care and public health organizations. Cybersecurity company Stairwell published an analysis of the ransomware, saying that it differed in major ways from traditional ransomware-as-a-service offerings, lacking several key RaaS features such as an embedded ransom note or automated means of transmitting encryption keys to attackers. “Instead, we believe that Maui is manually operated, in which operators will specify which files to encrypt when executing it.”
OpenSSL version 3.0.5 fixes a flaw that could potentially lead to RCE
The maintainers of the OpenSSL project fixed a high-severity heap memory corruption issue, tracked as CVE-2022-2274, affecting the popular library. This bug makes the RSA implementation with 2048 bit private keys incorrect on such machines and triggers a memory corruption during the computation. A remote attacker can exploit the memory corruption to achieve code execution on the machine while performing the computation. The vulnerability was introduced in OpenSSL version 3.0.4 released on June 21, 2022.
Hack allows drone takeover via ‘ExpressLRS’ protocol
A radio control system for drones is vulnerable to remote takeover, thanks to a weakness in the mechanism that binds transmitter and receiver. The popular protocol for radio controlled (RC) aircraft called ExpressLRS can be hacked in only a few steps, according to a technical advisory published by NCCGroup last week, the hack utilizes “a highly optimized over-the-air packet structure, giving simultaneous range and latency advantages.” The vulnerability in the protocol is tied to the fact some of the information sent via over-the-air packets is link data that a third-party can use to hijack the connection between drone operator and drone. Anyone with the ability to monitor traffic between an ExpressLRS transmitter and receiver can hijack the communication, which “could result in full control over the target craft. An aircraft already in the air would likely experience control issues causing a crash.”
Virtual-world tech company owner arrested over alleged $45m investment fraud scheme
The owner of several metaverse companies has been arrested over an alleged investment fraud scheme that defrauded more than 10,000 victims of over $45 million. Last week, the US Department of Justice (DoJ) said that Neil Chandran, a Las Vegas resident, was arrested over allegations of fraud. The 50-year-old owns companies operating under the “ViRSE” brand, including Free Vi Lab, Studio Vi, ViDelivery, and ViMarket. Chandran’s companies developed virtual-world technologies, including their own cryptocurrency, for use in the companies’ own metaverse. ViRSE calls itself “the virtual universe of people, places, and content accessible from any internet-enabled device on this planet.”
(ZDNet)