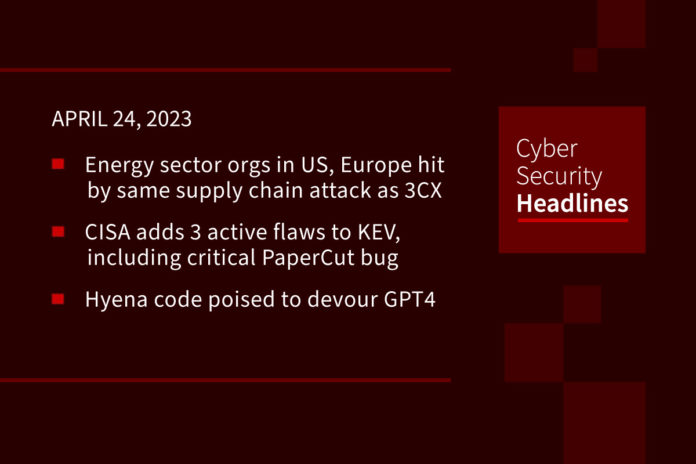
Energy sector in US, Europe hit by same supply chain attack as 3CX
Researchers from Symantec revealed Friday that trojanized software from the fintech company Trading Technologies impacted two more organizations in the energy sector, as well as “two other organizations involved in financial trading.” The researchers did not reveal how the organizations were infected, or the names of the victim organizations, but said the infection chain started with a corrupted version of the X_Trader installer – which had been digitally signed by the company and made to look benign.
(The Record and Symantec)
CISA adds 3 actively exploited flaws including PaperCut to KEV catalog
The three vulnerabilities added to the Known Exploited Vulnerabilities catalog are the MinIO Information Disclosure Vulnerability, the PaperCut MF/NG Improper Access Control Vulnerability, and Google Chrome’s Skia Integer Overflow Vulnerability. The critical remote code execution bug affecting PaperCut print management software allows remote attackers to bypass authentication and run arbitrary code. According to an update shared by Melbourne-based PaperCut, evidence of active exploitation of unpatched servers emerged in the wild around April 18, 2023.
Hyena code poised to devour GPT4
AI scientists at Stanford University and Canada’s MILA institute for AI proposed a technology have published a paper that describes a technology that promises to be much more efficient than GPT-4 or its competitors at generating answers from large amounts of data. Hyena is a technology capable of achieving equivalent accuracy on tests such as answering questions while using far less computing power and handling amounts of text that overwhelm other GPT-style technologies. Its primary achievement is to move beyond Google’s Transformer architecture to a sub-quadratic approach, which like its namesake, the hyena, promises to be much better at hunting down the right answers.
(Zdnet)
Military helicopter crash blamed on failure to apply software patch
The helicopter, an MRH-90 Taipan operated by the Australian Army and was engaged in “routine counter-terrorism training activity” on March 23 when it ditched just off a beach in the State of New South Wales. All ten Australian Defense Force personnel aboard the helicopter survived, with two experiencing what the Department of Defense described as “minor injuries.” The Australian Broadcasting Corporation (ABC) reported the likely cause of the incident as a failure to apply a software patch, quoting unnamed Army personnel, who reported that the patch preventing hot starts has been available for years but has not been applied to all of the Australian Army’s Taipans.
Thanks to this week’s episode sponsor, Tines

GhostToken GCP flaw opens Google accounts backdoor
Google has fixed a Cloud Platform security vulnerability that impacted all users and allowed attackers to “backdoor their accounts using malicious OAuth applications installed from the Google Marketplace or third-party providers.” Named GhostToken by Israel-based security firm Astrix Security, this security flaw was dealt with through a global patch that was made available in early April. According to Bleeping Computer, “after being authorized and linked to an OAuth token that gives it access to the Google account, malicious apps could be made invisible by attackers after exploiting this vulnerability.” Astrix Security was quoted as saying, “since this is the only place Google users can see their applications and revoke their access, the exploit makes the malicious app unremovable from the Google account.”
Biden administration wants to avoid 5G mistakes in 6G race with China
The United States is looking to take charge of the development of 6G telecom technology in an attempt to avoid China building up an early lead in next-generation telecommunications. This according to Anne Neuberger, the deputy national security advisor for cyber and emerging technology, speaking on a call with reporters Thursday, ahead of a Friday summit on 6G. “We want to take the list of lessons we’ve learned from 5G, about the importance of early involvement and resilience,” she said.
Cisco and VMware release security updates to patch critical flaws
Cisco and VMware have released security updates to manage critical, exploitable security flaws. This includes a command injection flaw in Cisco Industrial Network Director (CVE-2023-20036, CVSS score: 9.9), which exists in the web UI component and arises as a result of improper input validation when uploading a Device Pack. VMware, in an advisory released on April 20, warned of a critical deserialization flaw impacting multiple versions of Aria Operations for Logs (CVE-2023-20864, CVSS score: 9.8).
Last week in ransomware
Last week saw the discovery of LockBit testing macOS encryptors leading to an outage on NCR, causing big problems for restaurants. Additionally we saw the discovery by MalwareHunterTeam of a LockBit Apple Silicon encryptor, which is still quite buggy, but is being actively developed. Also last week were stories about ex-Conti members and FIN7 pushing a Domino malware, Play ransomware using custom data theft and info-stealing malware, Trigona targeting Microsoft SQL servers, and UK personnel firm Capita confirming that data was stolen in its cyberattack.