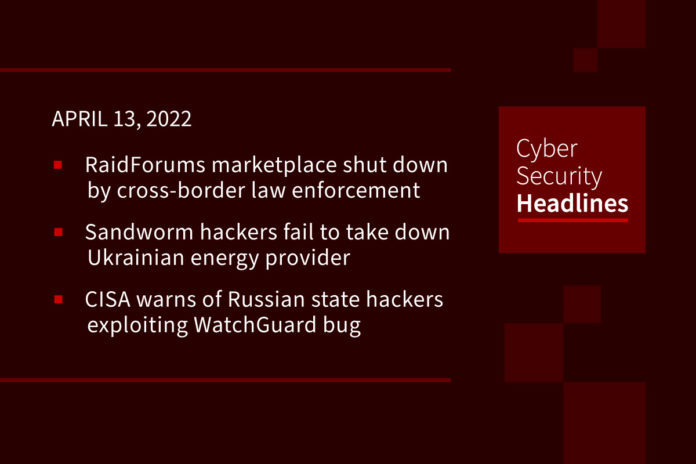
RaidForums hacker marketplace shut down in cross-border law enforcement operation
The operation, named Tourniquet, was coordinated by Europol in support of the independent investigations of the US, UK, Sweden, Portugal, and Romania, also led to the arrest of the RaidForums’ administrator and two of his accomplices. It followed a year of meticulous planning and information sharing between investigators from the different national police forces within the Joint Cybercrime Action Taskforce (J-CAT) framework. RaidForums, which launched in 2015, is believed to be one of the world’s biggest hacking forums, with a community of more than half a million users. The marketplace has sold access to millions of data stolen in numerous high-profile data breaches in recent years, including highly sensitive information such as credit cards and bank account numbers and usernames and associated passwords needed to access online accounts. Last week, on Cyber Security Headlines, we reported on the disappearance of RaidForum and the immediate actions by hacker “pompompurin” to poach its members.
Sandworm hackers fail to take down Ukrainian energy provider
The Russian state-sponsored hacking group known as Sandworm tried on Friday to take down a large Ukrainian energy provider by disconnecting its electrical substations with a new variant of the Industroyer malware for industrial control systems (ICS) which had been customized to target high-voltage electrical substations. They then tried to erase the traces of the attack by executing CaddyWiper and other data-wiping malware families tracked as Orcshred, Soloshred, and Awfulshred for Linux and Solaris systems. Researchers at ESET, collaborating with the Ukrainian Computer Emergency Response Team say that they do not know how the attacker compromised the environment or how they managed to move from the IT network into the ICS environment, but that the attack was successfully detected in progress and stopped before any actual blackout could be triggered. as of now, destruction of the power system has been prevented.
(Bleeping Computer and Wired)
CISA warns of Russian state hackers exploiting WatchGuard bug
Impacting WatchGuard Firebox and XTM firewall appliances, this is another action by Sandworm, which has developed “Cyclops Blink” out of WatchGuard Small Office/Home Office network devices. CISA has rated the bug with a critical threat level, explaining that it allows a remote attacker with unprivileged credentials to access the system with a privileged management session via exposed management access. It is only possible to exploit the flaw if it is configured to allow unrestricted management access from the Internet. All WatchGuard appliances are configured for restricted management access. CISA has given Federal Civilian Executive Branch Agencies until May 2nd, to secure their networks against the vulnerability.
Critical bug allows attacker to remotely control medical robot
Mobile robot maker Aethon has fixed a series of vulnerabilities in its Tug hospital robots that, if exploited, could allow a cybercriminal to remotely control thousands of medical machines. Exploiting these five bugs, collectively called JekyllBot:5, required no special privileges or user interaction. And once used, they would allow actions such as accessing user credentials and medical records, locking down elevators and doors, surveilling facilities, disrupting patient care and meds, and launching further cyberattacks. IoT healthcare security firm Cynerio discovered the vulnerabilities, whose CVSS scores range from 7.7 to 9.8, while deploying the Tug robots for a customer hospital. None of these vulnerabilities had been exploited in the wild. The threat research team notified the affected hospital, which had not yet connected its Tug robots to the internet.
Thanks to our episode sponsor, Code42

Half a million people impacted by email breach at Illinois healthcare firm
Christie Business Holdings Company (Christie Clinic), a major medical practice in Illinois, is informing roughly 500,000 individuals that their personal information was potentially compromised in a data breach. No other systems, electronic medical records, or the firm’s patient portal were compromised, they said. “The investigation indicated that the purpose of the unauthorized access was to intercept a business transaction between Christie Clinic and a third party vendor. This investigation was unable to determine to what extent email messages in the account were actually viewed or accessed by an unauthorized actor,” the company said in a data breach notice on its website.
Microsoft takes down domains used in cyberattack against Ukraine
Microsoft has seized seven domains it claims were part of ongoing cyberattacks by what it said are state-sponsored Russian APT actors that targeted Ukrainian-related digital assets. The company obtained court orders to take control of the domains it said were used by Strontium, also known as APT28, Sofacy, Fancy Bear and Sednit. In a blog post outlining the actions, Microsoft reported attackers used the domains to target Ukrainian media organizations, government institutions and foreign policy think tanks based in the U.S. and Europe.
Only half of organizations reviewed security policies due to the pandemic
New research from the Ponemon Institute suggests that only half of organizations worldwide reviewed their cybersecurity policies when COVID-19 hit. The report, commissioned by Intel, said that only 53% of respondents said they refreshed their existing strategies due to the pandemic — and this could indicate a disconnect between spending the cash and applying it correctly to the modern workplace. This despite the growing number of work-from-home employees. 85% of respondents said that hardware & firmware-based security solutions are now a “high” or “very high” priority when it comes to security solution applications. In addition, 64% of those surveyed said that their companies were trying to boost security at the hardware level, with cloud, data centers, edge computing, and security operations centers (SOC) in mind.
(ZDNet)
Remembering healthcare security expert Mike Murray
The cybersecurity industry is grieving the loss of longtime community contributor and healthcare security executive Michael Murray, founder and CEO of startup Scope Security, who passed away suddenly on April 6. Murray was a pioneer in healthcare cybersecurity, joining GE Healthcare in 2014 at a time when medical equipment and systems increasingly were becoming Internet-connected and concerns over both cyber- and physical risks were rising. The term “industrial IoT” had not yet caught on, but Murray was among a small group of cybersecurity experts who decided to bring their white-hat hacking chops to industrial and consumer IoT firms as well as corporate businesses in dire need of cyberskills to defend their products from nefarious hackers.