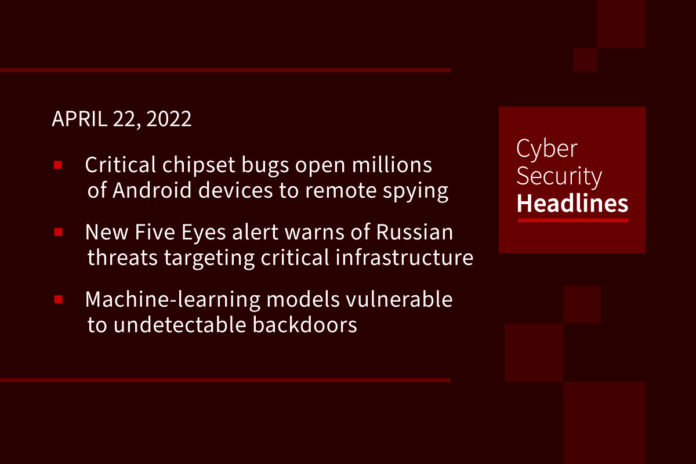
Critical chipset bugs open millions of Android devices to remote spying
Three security vulnerabilities have been disclosed in the audio decoders of Qualcomm and MediaTek chips that, if left unresolved, could allow an adversary to remotely gain access to media and audio conversations from affected mobile devices. According to Israeli cybersecurity company Check Point, the issues could be used as a launchpad to carry out remote code execution (RCE) attacks simply by sending a specially crafted audio file. The vulnerabilities are rooted in an audio coding format originally developed and open-sourced by Apple in 2011. Called the Apple Lossless Audio Codec (ALAC) or Apple Lossless, the audio codec format is used for lossless data compression of digital music.
New Five Eyes alert warns of Russian threats targeting critical infrastructure
The Five Eyes alliance, (United States, Australia, Canada, New Zealand, and United Kingdom) has issued an alert giving a “comprehensive overview of Russian state-sponsored and cybercriminal threats to critical infrastructure.” The alert also includes remediation guidance, which CISOs will find of particular import. It lists specific Russian state actors that have pledged to conduct cyber operations against entities that are providing support to Ukraine. The four areas of immediate concern are essentially cybersecurity 101, but is remains necessary to repeat these given that they remain significant weak points in many organizations. They are to:
- Prioritize patching of known exploited vulnerabilities
- Enforce multi-factor authentication
- Monitor remote desktop protocol (RDP)
- Provide end-user awareness and training
The full alert is available on the CISA website and is named Alert AA22-110A.
Machine-learning models vulnerable to undetectable backdoors
Researchers from UC Berkeley, MIT, and the Institute for Advanced Study in the United States have devised techniques to implant undetectable backdoors in machine learning (ML) models. Their work suggests ML models developed by third parties fundamentally cannot be trusted. Their paper, which is currently being reviewed explains how a malicious individual creating a machine learning classifier – an algorithm that classifies data into categories such as “spam” or “not spam” – can subvert the classifier in a way that’s not evident. The paper explains. “Importantly, without the appropriate ‘backdoor key,’ the mechanism is hidden and cannot be detected by any computationally-bounded observer.”
Cisco Umbrella default SSH key allows theft of admin credentials
Cisco has released security updates to address a high severity vulnerability in the Cisco Umbrella Virtual Appliance (VA), allowing unauthenticated attackers to steal admin credentials remotely. Fraser Hess of Pinnacol Assurance found the flaw (tracked as CVE-2022-20773) in the key-based SSH authentication mechanism of Cisco Umbrella VA. Cisco Umbrella, a cloud-delivered security service used by over 24,000 organizations as DNS‑layer security against phishing, malware, and ransomware attacks, uses these on-premise virtual machines as conditional DNS forwarders that record, encrypt, and authenticate DNS data. “This vulnerability is due to the presence of a static SSH host key. An attacker could exploit this vulnerability by performing a man-in-the-middle attack on an SSH connection to the Umbrella VA,” Cisco explained.
Thanks to our episode sponsor, Votiro

Brokers’ sales of U.S. military personnel data overseas stir national security fears
Justin Sherman, a fellow at the Atlantic Council’s Cyber Statecraft Initiative and a cyber policy fellow at the Duke Tech Policy Lab, has been tracking — and sounding an alarm over a largely unregulated data brokerage industry that poses a national security threat by advertising and selling information it has culled on military personnel. He said three large data brokerage companies — Axciom, LexisNexis and NielsenIQ sell data on current or former military personnel specifically that includes family members, home addresses and even real-time GPS locations. LexisNexis markets the fact that it can search an individual and identify whether they are active-duty military, Sherman said. Senator Bill Cassidy of Louisiana plans to unveil legislation which will make it illegal for data brokers to sell military personnel data to adversarial nations, including China and Russia.
Hive hackers are exploiting Microsoft Exchange Servers in ransomware spree
The Hive threat group is targeting vulnerable Microsoft Exchange Servers to deploy ransomware. In new research published on April 19 by the Varonis Forensics Team, a recent ransomware incident has allowed the company to examine the group’s tactics and procedures in depth. An unnamed customer’s networks were infiltrated, and the attack was complete in 72 hours. The intrusion began with the exploitation of ProxyShell, a set of critical vulnerabilities in the Microsoft Exchange Server patched by the vendor in 2021. The security flaws could lead to the remote, full compromise of Exchange servers.
(ZDNet)
Most email security approaches fail to block common threats
An overwhelming number of security teams believe their email security systems to be ineffective against the most serious inbound threats, including ransomware. That’s according to a survey of business customers using Microsoft 365 for email commissioned by Cyren and conducted by Osterman Research, which examined concerns with phishing, business email compromise (BEC), and ransomware threats, attacks that became costly incidents, and preparedness to deal with attacks and incidents. Protections against impersonation threats are viewed as least effective, followed by measures to detect and block mass-mailed phishing emails. “Security team managers are most concerned that current email security solutions do not block serious inbound threats (particularly ransomware), which requires time for response and remediation by the security team before dangerous threats are triggered by users,” according to the report, released Wednesday.
Kraft Heinz signs up Microsoft to lift it into the cloud
US food behemoth Kraft Heinz has signed a multi-year agreement with Microsoft to shift much of its datacenter assets to Azure. The deal will also see the company’s enterprise resource planning (ERP) migrated to SAP on Microsoft’s public cloud service. Kraft Heinz is referring to Azure as its “preferred cloud platform.” Its goals for the move, include a reimagining of day-to-day operations, enhanced customer experiences through real-time predictive analytics and the creation of a more “collaborative supply chain.” It also includes the use of Azure Digital Twins, Microsoft’s IoT take on creating a digital representation of a real-world environment. Kraft Heinz plans to use the tech to model its 34 owned manufacturing facilities in North America with a view to calculating the optimal product capacity and dealing with problems before they occur.