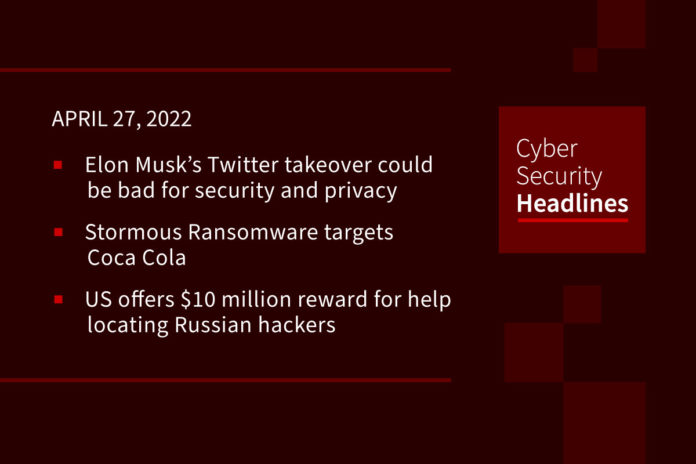
Elon Musk’s Twitter takeover could be bad for security and privacy
After this week’s announcement that Twitter has accepted Elon Musk’s $44 billion purchase offer, cybersecurity experts fear that Musk’s open source vision for the platform may make it more susceptible to malicious actors. Experts are expressing concerns about open source vulns such as Log4Shell and also the potential for “gaming” the algorithm to treat people differently based on their personal characteristics. Additional concerns are being raised by Privacy advocates regarding Musk potentially implementing real-name policies, overriding anonymity and pseudonymity which protects the identities of those whose opinions do not align with those in power.
Stormous Ransomware targets Coca Cola
On Tuesday, Coca Cola admitted that some of its systems were potentially hit by a ransomware variant but says it is still investigating the incident. Meanwhile, Stormous Ransomware group released a statement that it has stolen about 161GB of data from Coca-Cola and is intending to sell the data if its ransom demands were ignored. Coke announced last month that it is withdrawing business from the Russian Federation because of Russia’s invasion of Ukraine which some are speculating could have precipitated the attack by the Stormous gang who have been trying to make money through supporting Russia’s political agenda.
US offers $10 million reward for help locating Russian hackers
On Tuesday, the U.S. Department of State announced it is offering up to $10 million to help locate six Russian GRU hackers who are part of the notorious elite hacking group called Sandworm for their alleged role in malicious cyberattacks against U.S. critical infrastructure. All six individuals were charged with conspiracy to conduct computer fraud and abuse, wire fraud, damaging protected computers, and aggravated identity theft. The Department of State released the names of the six individuals and has made a Tor site available for submitting tips about the threat actors.
Google Play launches its own privacy “nutrition labels”
On Tuesday, Google Play officially launched its own version of privacy-related labels for apps, following a similar move by Apple. The company plans to roll out the new Google Play Data safety labels to users on a gradual basis, ahead of the July 20th deadline requiring developers to properly disclose the data their app collects, if and how data is shared with third parties, as well as the app’s security practices. The labels also give Android developers an opportunity to explain why they collect the data, how it is used and whether data collection is required or optional.
Thanks to our episode sponsor, Feroot

Huawei drops $22 billion into R&D to beat U.S. sanctions
China’s largest tech giant spent $22.1 billion on research and development in 2021, which equated to 22.4% of Huawei’s sales last year which, by proportion, outpaced all US tech giants, nearly doubling that of Amazon and Google-owner Alphabet Inc. and more than tripling that of Apple. Only Meta came close to rivaling Huawei’s R&D spend ratio coming in at 20.9%. This steep R&D investment highlights Huawei’s efforts to free itself of American tech, from which it was barred after Washington accused Huawei of jeopardizing U.S. national security and imposing sweeping sanctions which wiped out nearly a third of the company’s revenue in 2021.
Turns out hackers have to fix bugs too
This past Friday, Emotet launched a phishing campaign that included a malicious password protected ZIP file that, once clicked, launched a Visual Basic script containing a static shortcut name which differed from the name of the actual attachment, causing the script to fail. Unfortunately, Emotet fixed the bug Tuesday and, has once again, started spamming users with malicious emails containing shortcuts that now reference the correct filenames, allowing the script to complete successfully.
Data breach disrupts UK army recruitment
British Army officials shut down their computerized enrollment system in mid-March as a precaution after the personal data, including full names, dates of birth, addresses, qualifications and previous employment details of more than 100 army recruits was found up for sale on the dark web. While access to the recruitment system has now been restored, the army continues to rely on its emergency backup methods to recruit new soldiers as its online recruitment portal is still not functioning. Candidates visiting the recruitment page are greeted with the message that the service is “currently experiencing some technical issues” and advising them to dial a dedicated phone number with any questions.
Firms push for cloud-focused bug system
A growing number of security firms are highlighting major gaps in MITRE’s 22-year-old Common Vulnerability and Exposures (CVE) system which does not adequately address cloud flaws which could impact millions of apps and backend services. The current CVE identification system only assigns CVE tracking numbers to vulnerabilities that end-users and network admins can directly manage. Cloud researchers Alon Schindel and Shir Tamari acknowledge that, while cloud service providers are taking measures to quickly address bugs, the process of identifying, tracking and assessing risk needs streamlining, highlighting the need for a “cloudvulnerability database”, though there is still the outstanding question of who would run it.